Computer Science: CUET Mock Test - 7 - CUET MCQ
30 Questions MCQ Test CUET Mock Test Series - Computer Science: CUET Mock Test - 7
The Programming language Python is named after:
A relational database, which is in 3NF, may have undesirable data redundancy because there may exist
____ constraints apply only to individual column.
We know that RJ-45 is an eight-wire connector that connects a computer to LAN, especially Ethernets. Here, what is the expansion of RJ?
Which of the following options is not correct?
Study the following program:
x = 1
while true:
if x % 5 = = 0:
break print(x) x + = 1
What will be the output of this code?
Which of the following statements is incorrect in the context of binary files?
A perfect hash function maps every input key to a unique index in the hash table. If the hash function is perfect, collisions will______.
For which constraints are indexes created when the constraint is added?
Where would you look for errors from the database engine?
Which protocol is the foundation of data communication for the World Wide Web?
What will be the output of the following Python code?
def f1(a,b=[]):
b.append(a)
return b
print (f1(2,[3,4]))
Syntax of seek function in Python is myfile.seek(offset, reference_point) where myfile is the file object. What is the default value of reference_point?
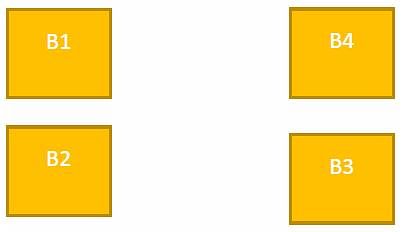
A company ABC Enterprises has four blocks of buildings as shown in the figure:
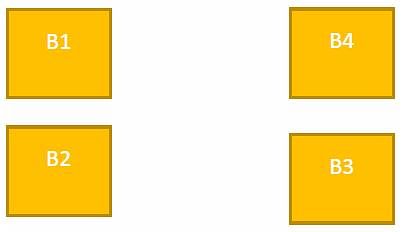
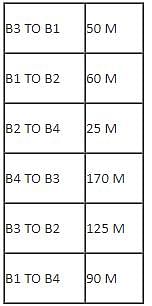
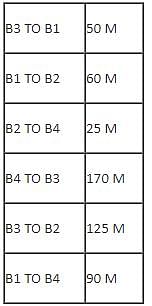
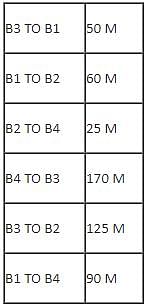
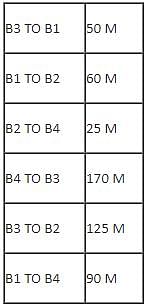
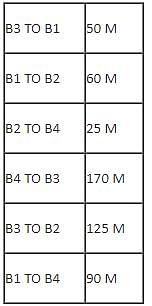
Center to center distance between various blocks:
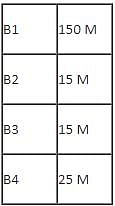
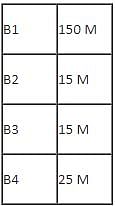
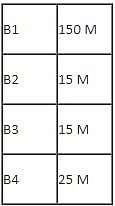
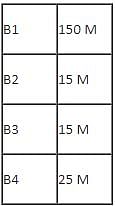
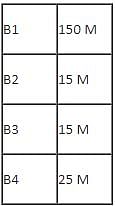
Number of computers in each block:
Computers in each block are networked but blocks are not networked. The company has now decided to connect the blocks also.
Q. Suggest the most appropriate topology for the connections between the blocks.
A company ABC Enterprises has four blocks of buildings as shown in the figure:
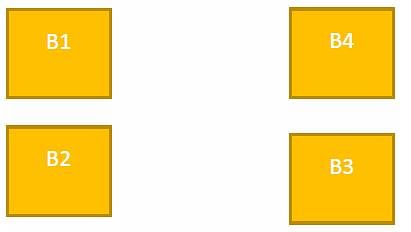
Center to center distance between various blocks:
Number of computers in each block:
Computers in each block are networked but blocks are not networked. The company has now decided to connect the blocks also.
Q. Which one of the following devices will you suggest for connecting all the computers with in each of their blocks?
A company ABC Enterprises has four blocks of buildings as shown in the figure:
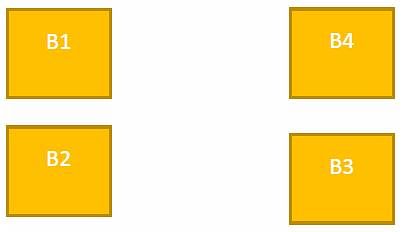
Center to center distance between various blocks:
Number of computers in each block:
Computers in each block are networked but blocks are not networked. The company has now decided to connect the blocks also.
Q. Suggest the most appropriate location of the server, to get the best connectivity for maximum number of computers.
A company ABC Enterprises has four blocks of buildings as shown in the figure:
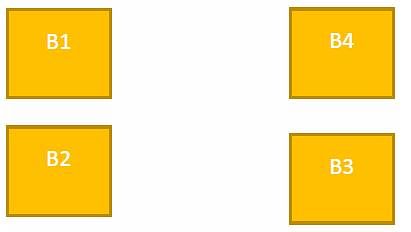
Center to center distance between various blocks:
Number of computers in each block:
Computers in each block are networked but blocks are not networked. The company has now decided to connect the blocks also.
Q. The company wants internet accessibility in all the blocks. The suitable and cost-effective technology for that would be:
A company ABC Enterprises has four blocks of buildings as shown in the figure:
Center to center distance between various blocks:
Number of computers in each block:
Computers in each block are networked but blocks are not networked. The company has now decided to connect the blocks also.
Q. The company is planning to link its head office situated in New Delhi with the offices in hilly areas. Suggest a way to connect it economically:
What error does the following code produce?
num = 6
print(math.factorial(num))
Python executes the else part of try-except-else:
Example 1:
Consider array has 4 elements and a searching element 16.
A[4]= {10, 16, 22, 25}
The number of iterations are required to search an element by using a binary search= T1
Example 2:
Consider array has 4 elements and a searching element 22.
A[4]= {10, 16, 22, 25}
The number of iterations are required to search an element by using a binary search= T2
Note: Searching is successful.
Which of the following statement are true?
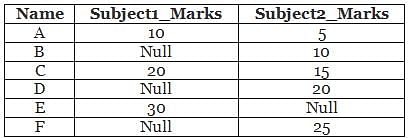
Consider the following student relation.
Student relation has Name, Subject1_Marks, and Subject2_Marks attributes.
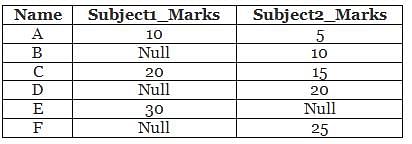
What is the output for the given SQL query?
Query:
Select sum(subject1_Marks)+sum(Subject2_Marks)
From student;
Is the following Python code valid?
try:
# Do something
except [exception-name]:
# Do something
except:
# Do something
The range of the following data 95, 115, 25, 20, 35, 55 is
Which of the following sorting algorithm required the least swap to sort the following list?
L1: [52,18,16,12,36,26,22]
|
8 docs|148 tests
|