Textbook Solutions: Connections are made: Accessing the internet | IGCSE Cambridge Computing for Year 7 - Class 7 PDF Download
Q1. For each of the scenarios below, identify the characteristic of the transmission method that has caused the issue. For example, if a mobile phone is in a tunnel and has no connection to the wireless access point, this would be caused by interference.
Scenario 1
Abid uses Wi-Fi to connect his laptop to the network to share some important files containing personal information (his name, address and medical details). Abid has set up his network without a password, so that anybody who joins the network can view his files.
Scenario 2
Alyssa uses cellular data to access the internet on her mobile phone while walking around a local town. Alyssa has entered a supermarket and her internet has stopped working.
Scenario 3
Adam has connected his Bluetooth headphones to his PC to listen to music. However, when he goes downstairs to the kitchen his headphones stop working.
Ans:
Scenario 1 (Abid’s Wi-Fi Network): The issue here is lack of security. Abid’s Wi-Fi network is unsecured because he has not set up a password, which means there’s no encryption of the data being transmitted. As a result, anyone within the Wi-Fi range can potentially access the network and view the files shared over it.
Scenario 2 (Alyssa’s Cellular Data): The problem Alyssa is facing is likely due to signal attenuation. When she enters the supermarket, the building’s structure, which may include metal framing and other materials, can block or weaken the cellular signal, causing her internet connection to stop working.
Scenario 3 (Adam’s Bluetooth Headphones): Adam’s issue is related to range limitation. Bluetooth has a limited range, typically up to 10 meters (33 feet) without obstacles. When Adam goes downstairs, he moves out of the Bluetooth signal range, causing the headphones to disconnect from the PC.
Transmission characteristics
Q1. For each of the scenarios below, discuss with a partner which transmission type would be most appropriate. Remember to say why: for example, Wi-Fi would be an appropriate transmission type to send data to laptops and other devices on a home network. This is because most homes are no larger than 50metres, which means that the signal will reach the devices without interference.
- Wirelessly connecting a PC to a network in the home
- Wirelessly connecting a keyboard and mouse to a PC
- Connecting a mobile phone to a tablet computer to share photos
- Connecting a mobile phone to the internet while out walking
Ans:
Wirelessly connecting a PC to a network in the home: Wi-Fi would be the most appropriate transmission type for this scenario. Wi-Fi has a good range to cover the average home and supports high data transfer rates, which is ideal for connecting PCs that may need to transfer large amounts of data or stream high-definition content.
Wirelessly connecting a keyboard and mouse to a PC: Bluetooth is the best fit for this scenario. Bluetooth is designed for short-range communication and low power consumption, making it perfect for peripherals like keyboards and mice that don’t require a wide range and need to conserve battery life.
Connecting a mobile phone to a tablet computer to share photos: Bluetooth could again be used here for its ease of pairing and energy efficiency. However, if the file sizes are large or if one wants to transfer files quickly, Wi-Fi Direct or NFC (Near Field Communication) could be better as they offer faster data transfer rates.
Connecting a mobile phone to the internet while out walking: Cellular data transmission is the most suitable for this scenario. Cellular networks provide wide coverage, allowing for an internet connection while on the move, which Wi-Fi cannot consistently provide outside of homes or hotspots.
Q2. Which transmission method is most likely to be used to view a news page by someone using a tablet computer or mobile phone?
Ans: For viewing a news page on a tablet computer or mobile phone, Wi-Fi or cellular data would be the most likely transmission methods used. If the user is at home or in a place with Wi-Fi access, they would probably use Wi-Fi due to its higher speed and lower cost. If they are on the move or away from Wi-Fi, cellular data would be used to access the internet. Both methods are capable of providing the necessary bandwidth and speed to view news pages, which generally do not require a lot of data.
Accessing web pages: IP addresses
Q1. Explain to a partner what a server is and what it does.
Ans:
A server is a powerful computer that provides data, services, or programs to other computers, known as clients, over a network. In essence, it serves information to clients that request it. Servers can manage network resources, host websites, run applications, store data, and more. They are designed to be reliable, secure, and capable of handling multiple requests simultaneously.
Here’s a simple way to think about it: Imagine a restaurant where the server (waiter) brings the food (data) you order (request) from the kitchen (the server in our tech scenario) to your table (your computer). Just like a restaurant server is there to fulfill your requests, a computer server handles requests from clients and delivers the requested information or services.
Q2. In pairs, look at the list of IP addresses of servers for large websites below.
- Now you know what IP addresses should look like, identify whether they are correct (valid) or incorrect (invalid).
- If you find any that have problems, explain why the IP address is not valid.
- Copy and complete the table to show your answers.
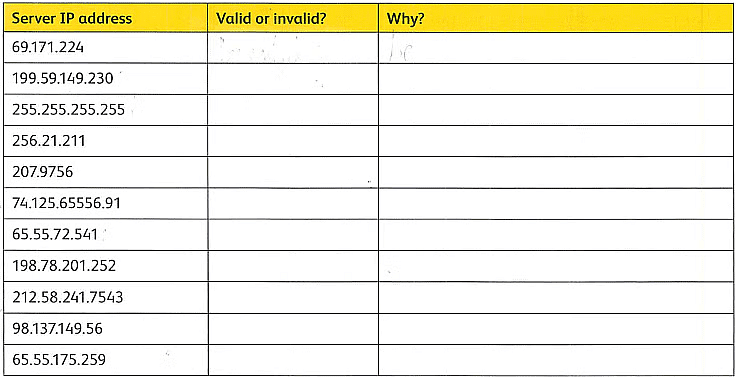
Ans:
Q3. Think about what the readers of the technology company news page might need to understand about IP addresses.
Ans:
Readers of a technology company news page might need to understand the following key points about IP addresses:
- Definition: An IP address is a unique identifier for a device on a network, similar to a home address for mail delivery.
- Function: It allows devices to find and communicate with each other on a network, whether it’s a local network or the internet.
- Types: There are two main types of IP addresses: IPv4, which is composed of four sets of numbers separated by periods (e.g., 192.168.1.1), and IPv6, which is longer and includes hexadecimal characters to accommodate more devices.
- Dynamic vs. Static: IP addresses can be dynamic (changing each time a device connects to a network) or static (permanently assigned to a device).
- Public vs. Private: Public IP addresses are used on the internet and must be unique worldwide, while private IP addresses are used on local networks and don’t need to be globally unique.
- Subnetting: This is a method used to divide a network into smaller, more manageable pieces.
- DHCP: The Dynamic Host Configuration Protocol automatically assigns IP addresses to devices on a network.
- NAT: Network Address Translation allows multiple devices on a local network to share a single public IP address.
URLs
Q1. Create a table listing five domain names that you have visited in the previous few weeks. Identify the URL, domain name and TLD for each, for example:
| URLs | Domain Name | TLD |
| https://www.netflix.com | netflix.com | .com |
Ans:
Q2. Work with a partner and explain what a I.JRL is to another pair. Make sure you include the following vocabulary in your explanation:
- URL
- Domain name
- TLD.
Ans:
A URL, or Uniform Resource Locator, is the address used to access a resource on the internet. It’s like the address you’d use to find a house in the real world, but for finding a webpage or file online. A URL consists of several parts, including the domain name and the TLD.
Domain Name: This is the human-readable address of the website, like ‘google’ in ‘google.com’. It’s unique to the website and is registered to the website owner.
TLD: The Top-Level Domain is the last part of the domain name, like ‘.com’, ‘.org’, or ‘.co.uk’. It can indicate the purpose of the website (like ‘.gov’ for government sites), the type of organization (‘.org’ for non-profits), or the country it’s associated with (‘.uk’ for the United Kingdom).
Accessing web pages: DNS
Q1. Explain to a partner how DNS enables users to access websites. Use this vocabulary in your explanation:
- URL
- IP address
- Web browser
- DNS server
- Request
- Web page.
Ans:
DNS, or Domain Name System, is like the phonebook of the internet. When you want to visit a website, you usually start by typing a URL (Uniform Resource Locator) into your web browser. This URL contains the domain name of the website you want to visit. However, the internet doesn’t understand words; it uses IP addresses to locate web servers.
So, when you make a request to visit a web page, your browser sends the domain name to a DNS server. The DNS server looks up the domain name in its database to find the corresponding IP address. Once it finds the IP address, it sends it back to your browser. Your browser then uses this IP address to send a request to the web server where the website is hosted. The web server then sends back the web page you requested, which your browser displays for you.
Q2. The following table shows the steps that DNS takes to translate a URL to an IP address, but they are in the wrong order.
Rewrite the steps in the correct order.
The URL gets sent to the DNS server to find the correct IP address.
If the higher-level DNS still cannot find it, a 404 error is returned.
If the DNS cannot find the IP address in its database, this search is then passed on to a higher-level DNS.
The web browser then sends a request to the web server's IP address, which returns the web page.
The IP address of the web server where the website is hosted is sent back to the user's computer.
A user types into their web browser the URL they would like to visit.
Ans:
- A user types into their web browser the URL they would like to visit.
- The URL gets sent to the DNS server to find the correct IP address.
- If the DNS cannot find the IP address in its database, this search is then passed on to a higher-level DNS.
- If the higher-level DNS still cannot find it, a 404 error is returned.
- The IP address of the web server where the website is hosted is sent back to the user’s computer.
- The web browser then sends a request to the web server’s IP address, which returns the web page.
Q3. Explain to a partner how a user would be able to view the Technology Company News Page. Use the vocabulary in the first task above.
Ans: To view the Technology Company News Page, a user would start by entering the URL of the news page into their web browser. The browser would send a request to a DNS server to translate the domain name into an IP address. The DNS server would find the IP address and send it back to the browser. The browser would then use this IP address to send a request directly to the web server hosting the news page. The server would process this request and send the web page back to the user’s browser, allowing them to read the latest technology news.
Padlocks and HTTPS
Q1. Explain to a partner how encryption is used to send data from one device to another.
Give some examples in your day-to-day life where you think it would be important to keep data secure during transmission.
Ans:
Encryption is a method of converting data into a code to prevent unauthorized access. When data is sent from one device to another, encryption scrambles the information into ciphertext, which is unreadable without the correct decryption key. The receiving device uses a key to decrypt the data back into its original form. This process ensures that even if the data is intercepted, it cannot be understood by anyone who doesn’t have the key.
Examples in day-to-day life where encryption is important include:
- Sending emails containing sensitive information.
- Online banking transactions.
- Messaging apps that handle private conversations.
- Storing personal data on cloud services.
- Making purchases on e-commerce websites.
Q2. Look at these examples and explain to a partner which need to be secure and which do not:
- A website that takes card payments for sports tickets
- A website that shows a list of top sports players and the number of points they have received in their sport
- A website that allows users to send pictures of their pets, including the owner's name and address.
Ans:
- A website that takes card payments for sports tickets: This needs to be secure to protect financial data and personal information from theft or fraud.
- A website that shows a list of top sports players and the number of points they have received in their sport: This does not need the same level of security as financial transactions, but basic security measures are still recommended to protect the integrity of the data.
- A website that allows users to send pictures of their pets, including the owner’s name and address: This needs to be secure to protect users’ personal information from being accessed by unauthorized individuals.
Q3. Discuss with a partner whether a technology company's news page would need to be secure.
Ans: A technology company’s news page should be secure to ensure the credibility of the content and protect the website from cyber threats. While it may not handle sensitive information like a payment portal, security measures can prevent hacking, which could lead to misinformation or malicious content being spread.
Q4. Explain to a partner exactly what to do to check a website's security.
Ans:
To check a website’s security, you can:
- Look for “https://” at the beginning of the URL, which indicates the site is using SSL/TLS encryption.
- Check for a padlock icon next to the URL, which also indicates an encrypted connection.
- Use browser security features that alert you to potential security risks.
- Review the website’s privacy policy to understand how your data is used and protected.
- Use online tools to scan the website for known vulnerabilities
Insecure websites
Q1. Identify whether the websites in the table below are secure or insecure.
- If it is secure, find the SSL certificate issuer (the organisation who gave the website its SSL certificate).
Copy and complete the table to show your results.
| Domain | Secure/Insecure | SSL certificate issuer |
| neverssl.com | ||
| bbc.co.uk | ||
| info.cern.ch | ||
| nasa.gov |
Ans:
Q3. Visit https://who.is and find out as much information as you can about the domain names listed below. This could include the owner, location or email address.
- neverssl.com
- bbc.co.uk
- amazon.com
- nasa.gov
Ans:
- neverssl.com: The domain is registered with Amazon Registrar, Inc., and the registrant contact information is protected by an identity protection service located in Hayes, Middlesex, UK3.
- bbc.co.uk: The domain is associated with the British Broadcasting Corporation, a public service broadcaster headquartered in London, England4.
- amazon.com: Amazon.com, Inc. is an American multinational technology company engaged in e-commerce, cloud computing, online advertising, digital streaming, and artificial intelligence5.
- nasa.gov: The National Aeronautics and Space Administration is America’s civil space program and the global leader in space exploration
Q4. Discuss with your partner why you think the websites you found with an SSL certificate have one. Do they send personal data?
What about the websites that do not have an SSL certificate? Why is this?
Ans:
Websites with SSL certificates typically have them because they handle sensitive data like personal information, financial transactions, or login credentials. The SSL certificate encrypts the data transmitted between the user’s browser and the website, making it difficult for unauthorized parties to intercept and read the information.
Websites that do not have an SSL certificate might not be dealing with sensitive data, or they could be informational sites where data encryption is not deemed necessary. However, it’s becoming increasingly common for all websites to use SSL certificates to ensure privacy and security, as well as to improve search engine rankings and user trust.
Keeping it all secure
Q1. Using the given Caesar cipher with a shift of two, write 9own the encrypted message for the plaintext message "COMPUTER".
Ans: AMKNSRCP
Q2. Using the given simple substitution cipher, write down the decripted message for the cipher message "UYZPBW".
Ans: CIPHER
Q3. Copy and complete this grid to create a Caesar cipher with a shift of six.
A B C D E F G H I J K L M N O P Q R S T U V W Y Z
Create an encrypted message (a word of your choice).
Ans:
To create a Caesar cipher with a shift of six, you shift each letter in the alphabet six places to the right. Here’s the completed grid:
Plain: A B C D E F G H I J K L M N O P Q R S T U V W X Y ZCipher: G H I J K L M N O P Q R S T U V W X Y Z A B C D E F
Let’s encrypt the word “HELLO” as an example:
Plain: H E L L OCipher: N K R R U
Q4. Why is encryption used during data transmission? Explain to a partner how encryption works. Include this vocabulary in your explanation:
- Network
- Security
Plaintext
- Scramble.
Ans: Encryption is used during data transmission to ensure security over a network. When data is sent from one device to another, it’s vulnerable to interception. To protect the data, it’s turned into plaintext and then scrambled using an encryption algorithm. This scramble transforms the plaintext into ciphertext, which is unreadable to anyone who doesn’t have the key to decrypt it. Only the intended recipient, who has the key, can decrypt the ciphertext back into readable plaintext.
Q5. Discuss why is it important that users understand how encryption works.
How can users check whether websites they use are encrypted?
How would you explain to somebody who has not created a cipher before how to encrypt and decrypt a message?
Ans:
It’s important for users to understand how encryption works because it helps them make informed decisions about their data privacy and security. Knowing about encryption can guide users in choosing secure services and practices when online.
Users can check if websites are encrypted by looking for “https://” at the beginning of the URL and a padlock icon in the address bar. These indicate that the website uses SSL/TLS encryption to secure the data transmitted between the user’s browser and the website.
To explain encryption and decryption to someone new:
- Encryption: Choose a method (like a Caesar cipher), take your original message (plaintext), and use the method’s rules to change the letters into a coded message (ciphertext).
- Decryption: To read an encrypted message, you need the key (like knowing the shift number in a Caesar cipher). Use the key to reverse the encryption process and turn the ciphertext back into plaintext.
Sending messages
Q1. In a small group, produce a mind map containing a section for each of the two bullet points below:
why errors occur in data transmission
what an error looks like.
Ans:
Why Errors Occur in Data Transmission:
Transmission Error: Caused by external electromagnetic interference, signal degradation, or faulty hardware1.
Data Packet Loss: Occurs due to errors in routing protocols, network congestion, or faulty networking devices1.
Network Latency: Arises from high network congestion or different processing powers of communicating devices1.
Configuration Errors: Result from misconfigured or outdated software1.
Physical Medium Issues: Such as thermal noise, electrical noise, and impulse noise2.
What an Error Looks Like:
Single-Bit Error: A single binary digit is altered, changing a 0 to a 1 or vice versa3.
Multiple-Bit Error: More than one bit is affected during transmission3.
Burst Error: Several consecutive bits are flipped, creating a sequence of incorrect values3.
Transmission Error Visuals: A logic 1 read as a logic 0, or vice versa, due to electromagnetic interference
Intelligent search engines
Q2. Think about the way in which search engines select the keywords from the search phrase. With a partner, discuss these questions:
- Why is it important to have an awareness of keywords when typing a search phrase?
- Did you find any examples that required more keywords to find the information you needed? Why?
Ans:
Importance of Keywords in Search Phrases:
- Relevance: Keywords help search engines understand the main focus of your query, leading to more relevant results.
- Efficiency: Using the right keywords can save time by narrowing down search results to what you’re actually looking for.
- Ranking: Search engines rank pages based on keywords, so choosing the right ones can lead you to higher-quality content.
Examples Requiring More Keywords:
- Specificity: If you’re looking for a particular aspect of a broad topic, adding more keywords can help. For example, searching for “tips for indoor gardening in small spaces” instead of just “gardening tips” can provide more targeted results.
- Context: Sometimes, a single keyword can have multiple meanings. Adding context can clarify your intent, like “Java programming” versus “Java coffee”.
- Updates: For recent information, adding keywords like “latest” or “2024” can filter out outdated content.
Al and reverse image searches
Q2. Explain to your partner how Al has improved the way that search engines work.
Ans:
AI has significantly enhanced the functionality of search engines in several ways:
Enhanced Search Results: AI-powered search engines can deliver more relevant and personalized search results. They go beyond simple keyword matching and use Natural Language Processing (NLP) to understand the context, intent, and semantics behind user queries1.
Voice-Activated Search: With AI, voice assistants like Siri, Google Assistant, and Alexa can interpret spoken queries and provide accurate information. This makes searching hands-free and more accessible1.
Personalized Recommendations: AI algorithms analyze user behavior, preferences, and historical data to offer personalized suggestions and content, improving the overall user experience1.
Visual and Image Search: AI has improved the capabilities of search engines to understand and process visual content, allowing users to search using images and receive information related to the visual content
Final project
Your task is to create a presentation to collate information about how certain technologies work. The information in your presentation will be used on the news page for the technology website.
1 Open the file Final Project.pptx provided by your teacher. Use this file to create your presentation, following the criteria from the technology company below.
The requirements of your presentation are:
Slide 1
a Explain how somebody could use Bluetooth, Wi-Fi and cellular data (4G and 5G) to connect their mobile device to the internet to access a web page.
b Describe when it may be better to use 5G than 4G and explain why.
Slides 2-3
a Explain what IP addresses are, how they work and what they are used for.
b Explain the structure of a URL and why we use URLs to locate web pages.
Slides 4-5
a Explain two ways that show a web page is secure and how to find information on the security certificates of a website.
b Explain how data can be transmitted securely using encryption, what this is and why it is important.
c Outline the reasons why errors can occur in data transmission.
Slides 6-8
Explain how a search engine categorises data (selects keywords from a search query).
Explain how Al is used in search-engine results.
List the steps that a computer takes when using Al to match images.
Outline another way in which Al is used, apart from search engines.
Ans:
Slide 1: Connecting to the Internet
Bluetooth: Connects devices over short distances without using wires. It can share internet access through a process called tethering1.
Wi-Fi: A wireless network that connects devices to the internet within a certain range, typically provided by a router connected to an ISP2.
Cellular Data (4G/5G): Uses cellular towers to provide internet access to mobile devices. 4G offers reliable speed and coverage, while 5G delivers faster speeds and lower latency3.
When to Use 5G Over 4G
5G is preferable when high-speed data transfer, low latency, and handling a large number of connected devices are crucial4. It’s ideal for streaming high-definition videos, real-time gaming, and IoT applications5.
Slides 2-3: IP Addresses and URLs
IP Addresses: Unique numerical labels assigned to devices on a network for identification and communication purposes. They facilitate the routing of data across the internet6.
URL Structure: Consists of a protocol, domain name, path, and parameters. It’s used to locate and retrieve resources on the web7.
Slides 4-5: Web Page Security and Data Transmission
Web Page Security Indicators:
HTTPS: Indicates secure communication between the browser and the web server8.
Padlock Icon: Visible in the browser’s address bar, signifying an encrypted connection9.
Finding Security Certificates: Check the certificate details by clicking on the padlock icon or use online tools to scan for website security certificates10.
Secure Data Transmission Using Encryption
Encryption: The process of converting plaintext into ciphertext using algorithms and keys, ensuring that only authorized parties can access the information11.
Importance: Protects sensitive data from unauthorized access, especially during transmission over the internet12.
Reasons for Errors in Data Transmission
Errors can occur due to noise, signal distortion, hardware failures, and synchronization issues between the transmitter and receiver13.
Slides 6-8: AI in Search Engines and Image Matching
Search Engine Data Categorization: Involves crawling, indexing, and ranking web pages based on relevance to the search query14.
AI in Search Results: AI helps interpret queries, match them to content, and continuously improve the quality of search results15.
AI Image Matching Steps:
Training Dataset Creation: Collect and label images.
Neural Network Training: Teach the AI model to recognize patterns.
Model Testing: Evaluate the model’s accuracy with new images16.
Other AI Applications: AI is also used in voice assistants, recommendation systems, and autonomous vehicles.
|
28 videos|17 docs|5 tests
|
FAQs on Textbook Solutions: Connections are made: Accessing the internet - IGCSE Cambridge Computing for Year 7 - Class 7
| 1. What are some common transmission characteristics of accessing web pages? |  |
| 2. How does DNS play a role in accessing web pages securely? |  |
| 3. Why is it important to use HTTPS and padlocks when accessing websites? |  |
| 4. How can users ensure that they are accessing secure websites? |  |
| 5. How do intelligent search engines play a role in accessing the internet? |  |





















