Cyber Ethics: Chapter Notes | Computer Application: Class 10 PDF Download
➢ E-commerce and security: In e-commerce, the transaction takes place over the network. E-commerce is the ability to do business online via the internet. The privacy in E-commerce means the protection of privacy of the parties involved in trading through E-commerce. Transaction security is vital in E-commerce. ➢ Fraud is an intentional false representation of a fact.
➢ Fraud is an intentional false representation of a fact.
➢ Fraud comes in many forms like,
- Credit card fraud
- Refund fraud
- Card testing
- Friendly fraud
- Identity theft
- Phishing
- Triangulation fraud
 ➢ Security is an essential part of any transaction that takes place over the internet. Customers will lose his / her faith in e-business if its security is compromised. Encryption is a technology which keeps the messages secret from unauthorized access. Digital signature is another security provision provided by the internet which ensures the authenticity of the information. A digital signature is a digital code that can be authenticated through encryption and password attached to an electronically transmitted message to uniquely identify the sender. Digital certificates are electronic files containing user name, user's public key, and name of certification authority such as Verisign, issuing the certificate. Secure Socket Layer [ SSL ] is a security protocol developed by Netscape Communications to protect communication over the internet.
➢ Security is an essential part of any transaction that takes place over the internet. Customers will lose his / her faith in e-business if its security is compromised. Encryption is a technology which keeps the messages secret from unauthorized access. Digital signature is another security provision provided by the internet which ensures the authenticity of the information. A digital signature is a digital code that can be authenticated through encryption and password attached to an electronically transmitted message to uniquely identify the sender. Digital certificates are electronic files containing user name, user's public key, and name of certification authority such as Verisign, issuing the certificate. Secure Socket Layer [ SSL ] is a security protocol developed by Netscape Communications to protect communication over the internet.
➢ Computer ethics: Computer ethics are a set of moral standards that govern the use of computers. It is society's views about the use of computers, both hardware and software. Privacy concerns, intellectual property rights and effects on the society are some of the common issues of computer ethics.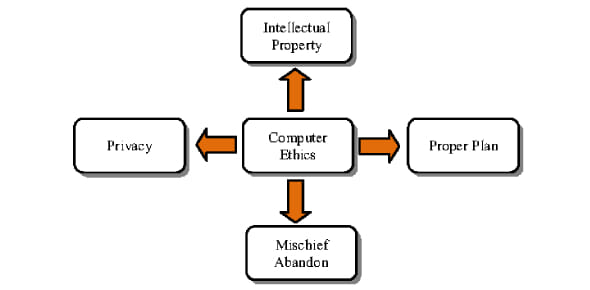 ➢ Privacy Concerns
➢ Privacy Concerns
- Hacking: It is unlawful intrusion into a computer or a network. A hacker can intrude through the security levels of a computer system or network and can acquire unauthorised access to other computers.
- Malware: It means malicious software which is created to impair a computer system. Common malware are viruses, spyware, worms and trojan horses. A virus can delete files from a hard drive, while a spyware can collect data from a computer.
- Data Protection: Also known as information privacy or data privacy, it is the process of safeguarding data which intends to influence a balance between individual privacy rights, while still authorising data to be used for business purposes.
- Anonymity: It is a way of keeping a user’s identity masked through various applications.
 ➢ Intellectual Property Rights: Intellectual property rights are the legal rights that cover the privileges given to individuals who are the owners and inventors of a work, and have created something with their intellectual creativity. Individuals related to areas such as literature, music, invention, etc., can be granted such rights, which can then be used in the business practices by them.
➢ Intellectual Property Rights: Intellectual property rights are the legal rights that cover the privileges given to individuals who are the owners and inventors of a work, and have created something with their intellectual creativity. Individuals related to areas such as literature, music, invention, etc., can be granted such rights, which can then be used in the business practices by them.
The creator/inventor gets exclusive rights against any misuse or use of work without his/her prior information. However, the rights are granted for a limited period of time to maintain equilibrium.
The following list of activities which are covered by the intellectual property rights are laid down by the World Intellectual Property Organisation (WIPO) —
- Industrial designs
- Scientific discoveries
- Protection against unfair competition
- Literary, artistic, and scientific works
- Inventions in all fields of human endeavor
- Performances of performing artists, phonograms, and broadcasts
- Trademarks, service marks, commercial names, and designations
- All other rights resulting from intellectual activity in the industrial, scientific, literary, or artistic fields
➢ Intellectual Property Rights can be further classified into the following categories: ➢ Software Licences: A software license agreement is a contract between the licensor or the author and the purchaser of a piece of software which establishes the purchaser's rights. It defines how that software can be used and what happens in the event of breach.
➢ Software Licences: A software license agreement is a contract between the licensor or the author and the purchaser of a piece of software which establishes the purchaser's rights. It defines how that software can be used and what happens in the event of breach.
➢ Proprietary software: Proprietary software (sometimes referred to as closed source software) is software that legally remains the property of the organisation, group, or individual who created it. The organisation that owns the rights to the product usually does not release the source code, and may insist that only those who have purchased a special licence key can use it.
➢ Free software: Free software (also called freeware) is licensed at no cost, or for an optional fee. It is usually closed source.
➢ A program is free software when the user has
- the freedom to run the program, for any purpose
- the freedom to access the source code and study how the program works
- the freedom to adapt it to user’s needs
- the freedom to redistribute copies
- the freedom to improve the program and release the improvements to the public, so that the whole community benefits
➢ Open source software: Open source software is free and openly available to everyone. People who create open source products publish the code and allow others to use and modify it. Communities of programmers often work together to develop the software and to support users. Open source products are usually tested in public by online contributors.
➢ Large companies such as Twitter, Facebook and the BBC make use of open source technology. For example, the BBC makes use of MySQL and it creates open source software, such as the program to improve the compatibility of iPlayer on smart TVs.
➢ FOSSM: The Free Open Source Software Movement (FOSSM) or Free/Libre Open Source Software (FLOSS) is a social movement with the goal of obtaining and guaranteeing certain freedoms for software users, to use, study, modify and redistribute. The Free Software movement and the open source movement are two separate movements. The term "open source" has different approach and philosophy. For the open source movement, the issue of whether software should be open source is a practical rather than an ethical question. GNU General Public License, is intended to guarantee our freedom to share and change free software, and to make sure the software will remain free for all the users. ➢ Freedom of Information: In India, Freedom of Information Act was implemented in 2002. The main principle behind Freedom of Information legislation is that people have a right to know about the activities of public authorities held by governments and government institutions. According to the Act, this information is in principle public and may only be withheld for legitimate reasons.
➢ Freedom of Information: In India, Freedom of Information Act was implemented in 2002. The main principle behind Freedom of Information legislation is that people have a right to know about the activities of public authorities held by governments and government institutions. According to the Act, this information is in principle public and may only be withheld for legitimate reasons.
According to this Act,
- Everybody has a right to access official information. Non-disclosure of information should be the default.
- An applicant does not need to give you a reason for wanting the information. On the contrary, the department must justify refusing them information.
- All the requests have to be treated equally.
➢ Right to Information Act, 2005 (RTI) is a revolutionary Act under which, a common man can demand any government agency to furnish information. The organisation is bound to provide the information, that too within 30 days, failing which the officer concerned is slapped with a monetary fine.
➢ Digital Divide: The Digital Divide, or the Digital Split, is a social issue referring to the differing amount of information between those who have access to the Internet and those who do not have access. The term became popular among concerned parties, such as scholars, policy makers, and advocacy groups, in the late 1990s. Broadly speaking, the difference is not necessarily determined by the access to the Internet, but by access to ICT (Information and Communications Technologies) and to Media that the different segments of society can use. With regards to the Internet, the access is only one aspect, other factors such as the quality of connection and related services should be considered. Today, the most discussed issue is the availability of the access at an affordable cost and quality.The problem is often discussed in an international context, indicating certain countries are far more equipped than other developing countries to exploit the benefits from the rapidly expanding Internet. The digital divide is not indeed a clear single gap which divides a society into two groups. Researchers report that disadvantage can take such forms as lower-performance computers, lower-quality or high price connections (i.e. narrowband or dialup connection), difficulty of obtaining technical assistance, and lower access to subscription-based contents.
Broadly speaking, the difference is not necessarily determined by the access to the Internet, but by access to ICT (Information and Communications Technologies) and to Media that the different segments of society can use. With regards to the Internet, the access is only one aspect, other factors such as the quality of connection and related services should be considered. Today, the most discussed issue is the availability of the access at an affordable cost and quality.The problem is often discussed in an international context, indicating certain countries are far more equipped than other developing countries to exploit the benefits from the rapidly expanding Internet. The digital divide is not indeed a clear single gap which divides a society into two groups. Researchers report that disadvantage can take such forms as lower-performance computers, lower-quality or high price connections (i.e. narrowband or dialup connection), difficulty of obtaining technical assistance, and lower access to subscription-based contents.
- The idea that some information and communication technologies are vital to quality civic life is not new. Some suggest that the internet and other ICTs are somehow transforming society, improving our mutual understanding, eliminating power differentials, realising a truly free and democratic world society, and other benefits.
➢ Why is there a gap?
- Lack of infrastructure
- Limited literacy rate
➢ Why should we bridge the gap?
- For reducing economic inequalities
- For social mobility
- For health democracy
- For overall economic growth.
➢ How can we bridge the gap?
- Equipping rural areas
- Reducing cost of internet
- Arranging training camps
➢ "Netiquette" refers to Internet etiquette. This simply means the use of good manners in online communication such as e-mail, forums, blogs, and social networking sites to name a few. It is important to use netiquette because communication online is non-verbal.
(i) Accuracy of information: Misleading others is obviously a major breach of online etiquette. This is true even if if s unintentional. Check facts before providing information or giving advice. Provide sources. If you're not an expert on a topic, maybe you shouldn't be acting like you are.
(ii) Use internet resources ethically: Online study resources should be used to support learning, not replace it.
(iii) Promote healthy discussions: To get the most out of online forums, a useful netiquette guideline is to promote healthy discussion. You can help your online community by posing questions, sharing experiences, providing positive feedback, asking follow-up questions, and referring to information sources. Being a positive contributor is better than being a critic, troll or other negative force.
(iv) Ignore inflammatory comments by trolls: It's generally best to ignore trolls. These are internet users who try to bait other users into a reaction.
(v) Respect others as equals: Show a little respect and humility online.
(vi) Remember, your words are permanent: Be careful with what you post online. Once it's out there, you may not be able to get it back.
(vii) Make your point in a nice way: Write in a way to get the kind of reaction you want. A little thoughtfulness, strategy and netiquette can go a long way in online discussions.
➢ Plagiarism is the wrongful appropriation and stealing and publication of another author's language, thoughts, ideas as one's own original work.
➢ Types of plagiarism are:
(i) Collusion
(ii) Complete plagiarism
(iii) Partial plagiarism
(iv) Self-plagiarism
(v) Copying and Pasting
(vi) Word Switch
(vii) Concealing sources
(viii) Inadvertently
Know the Terms
➢ LAMP: Linux , Apache , MySQL , PHP
➢ FLOSS: Free/Libre Open Source Software
➢ GNU: Generally Not Unix
- Go through this video and understand in detail Cyber Ethics for Class 10: Cyber Ethics Video Explanation
- Test your knowledge and attempt the test of Cyber Ethics for Class 10 through this link.
|
11 videos|49 docs|18 tests
|
FAQs on Cyber Ethics: Chapter Notes - Computer Application: Class 10
| 1. What is cyber ethics and why is it important? |  |
| 2. How can individuals protect their privacy and personal information online? |  |
| 3. What are the potential risks and challenges associated with cyber ethics? |  |
| 4. How can parents and educators promote cyber ethics among children and students? |  |
| 5. What are the legal consequences of unethical online behavior? |  |

|
Explore Courses for Class 10 exam
|

|


















