Media Access Protocols
Introduction
The data link layer provides node-to-node data transfer and hides the physical medium from the network layer. It is commonly split into two sublayers: Logical Link Control (LLC), which provides flow control, framing and error control; and Media Access Control (MAC), which governs how multiple stations share the physical medium and resolves contention or collisions.
Data Link Control
Data link control ensures reliable transmission over a direct link by providing framing, error detection and correction, acknowledgement, and flow control. When two devices have a dedicated link, these functions are sufficient to manage the communication.
Multiple Access Protocols - overview
When the medium is shared by multiple stations (for example, a shared bus, wireless channel or broadcast medium), stations must follow a multiple access protocol to coordinate use of the channel and avoid or resolve collisions. Without such a protocol, simultaneous transmissions will interfere and frames can be lost or corrupted.
Analogy: imagine a classroom where many students try to answer a question at once. The teacher (the multiple access protocol) imposes rules so that students do not speak all together and their answers can be heard.
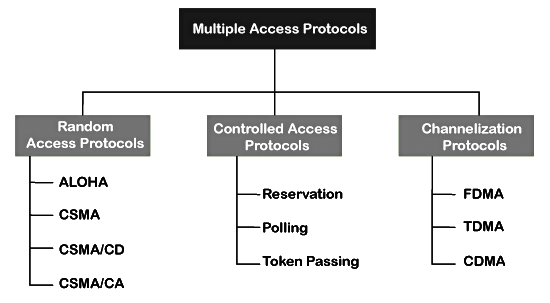
Multiple access protocols are classified into three broad families:
- Random access protocols - stations transmit whenever they have data, using built-in mechanisms to detect or recover from collisions (examples: ALOHA, CSMA variants).
- Controlled access protocols - a coordination mechanism grants permission to one station at a time (examples: polling, token passing, reservation).
- Channelization protocols - the channel bandwidth is divided among users by frequency, time or code so that multiple users can transmit simultaneously without colliding (examples: FDMA, TDMA, CDMA).
Random Access Protocols
Random access schemes give stations equal opportunity to transmit whenever they have a frame. No single station controls the medium; decisions are local and depend only on the station's knowledge of the channel. Collisions can occur; the protocol must include mechanisms to detect collisions or to retransmit after collision.
Common random access methods are:
- ALOHA
- CSMA (Carrier Sense Multiple Access)
- CSMA/CD (with collision detection)
- CSMA/CA (with collision avoidance)
ALOHA
ALOHA was an early random access protocol developed for a shared wireless medium. Any station transmits a frame whenever it has data. If a collision occurs, the sender waits a random time and retransmits.
Key rules of ALOHA:
- Any station may transmit a frame at any time.
- No carrier sensing is required.
- Frames that collide are lost and must be retransmitted.
- After transmission, the sender expects an acknowledgement; if none is received within a timeout it retransmits after a random backoff interval.
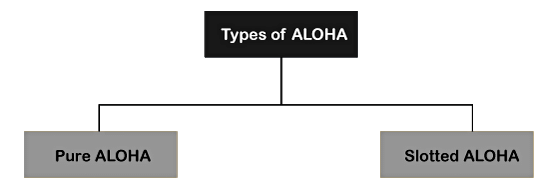
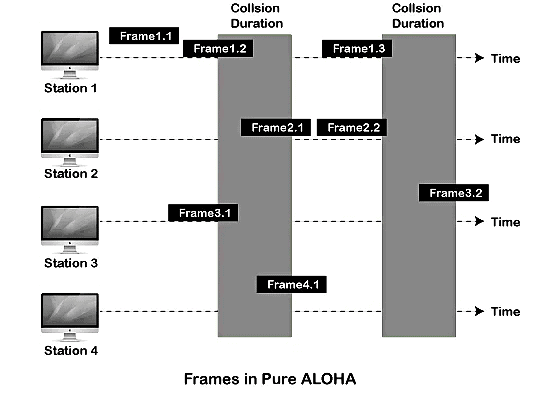
Pure ALOHA
In Pure ALOHA, stations transmit immediately when a frame is ready. Since transmissions may begin at arbitrary times, the vulnerable interval for a frame is twice the frame time (2 × Tfr): any other transmission that begins up to one frame time before or after the start of this frame will collide.
- The vulnerable time is 2 × Tfr.
- Throughput (successful frames per frame time) is S = G × e-2G, where G is the average number of transmission attempts per frame time.
- Maximum throughput occurs at G = 1/2 and is approximately 0.184 (18.4%) of the channel capacity.
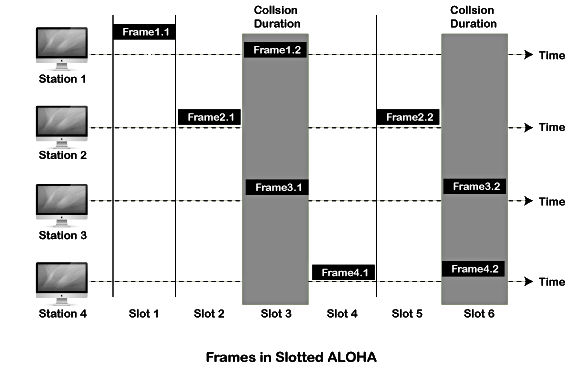
Slotted ALOHA
Slotted ALOHA improves Pure ALOHA by dividing time into equal slots of one frame time. Stations may begin transmission only at slot boundaries, which halves the vulnerable interval compared with Pure ALOHA and increases efficiency.
- The vulnerable time for a slot is Tfr (one frame time).
- Throughput is S = G × e-G, where G is the offered load in slots per frame time.
- Maximum throughput occurs at G = 1 and is approximately 1/e ≈ 0.368 (36.8%).
Carrier Sense Multiple Access (CSMA)
CSMA reduces collisions by making a station sense the carrier (the channel) before transmitting. If the channel is sensed idle, the station transmits; if it is busy, the station defers transmission.
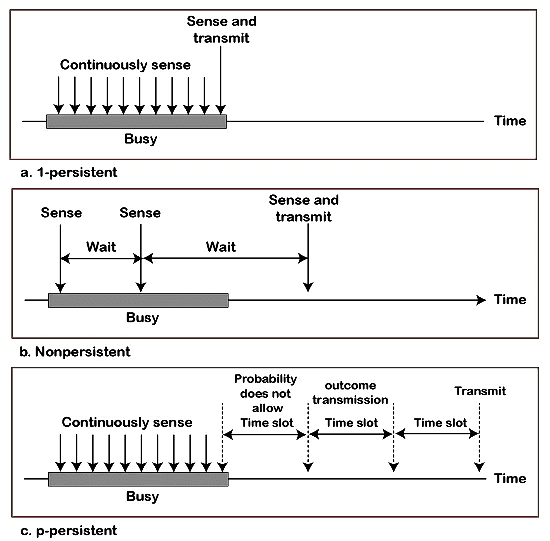
CSMA access modes
- 1-persistent CSMA: the station continuously senses the channel; if idle it transmits immediately (probability 1). If the channel is busy it continues sensing and transmits as soon as the channel becomes idle.
- Non-persistent CSMA: the station senses the channel; if busy it waits a random time before sensing again. This reduces contention but increases average delay.
- P-persistent CSMA: used with slotted channels. When a slot begins and the channel is idle, the station transmits with probability p; with probability (1-p) it defers to the next slot. This is a compromise between the 1-persistent and non-persistent behaviours.
- O-persistent (ordered-persistent): stations are assigned an order or priority; when the channel becomes free, each station waits a predetermined time based on its order before transmitting. This gives predictable prioritisation.
CSMA/CD (Collision Detection)
CSMA/CD adds collision detection to CSMA. While transmitting, a station monitors the channel to detect whether a collision has occurred (e.g., by sensing an unexpected increase in signal). If a collision is detected the sender immediately transmits a short jam signal to ensure all stations become aware of the collision, then stops and schedules a retransmission after a random backoff.
Additional points:
- CSMA/CD is effective on wired media where a station can sense transmissions from others (e.g., classic Ethernet on a shared coaxial bus).
- Retransmission uses a binary exponential backoff: after the k-th collision a station chooses a random number of slot times uniformly from 0..2k-1 (up to a maximum k). This reduces the probability of repeated collisions under heavy load.
- CSMA/CD cannot be used effectively on many wireless networks because a sender cannot reliably sense collisions while transmitting (the transmitted signal may overwhelm the received signal).
CSMA/CA (Collision Avoidance)
CSMA/CA is designed for environments, notably wireless LANs (IEEE 802.11), where collision detection is difficult. Instead of detecting collisions, stations try to avoid them using additional mechanisms.
Collision-avoidance techniques used in CSMA/CA include:
- Interframe spaces (IFS): different fixed waiting intervals are used to create priorities. Stations wait for an IFS after the channel becomes idle before attempting transmission; a shorter IFS means higher priority.
- Random backoff within a contention window: after the channel is sensed idle, a station chooses a random number of slot times from the current contention window and waits that many slots before transmitting; the window typically grows after collisions (exponential backoff).
- RTS/CTS (Request to Send / Clear to Send): optional short control frames used before data transmission to reserve the medium. The sender sends RTS; intended receiver replies with CTS. Neighbouring stations that hear RTS or CTS defer their transmissions, helping to mitigate the hidden terminal problem.
- Acknowledgements (ACK): the receiver sends an ACK after successful frame reception; absence of ACK prompts retransmission.
CSMA/CA reduces collisions in wireless networks at the cost of increased overhead (control frames and waiting times).
Controlled Access Protocols
Controlled access schemes coordinate access by granting explicit permission to a station before it may transmit. These methods avoid collisions (or reduce them to a minimum) at the expense of control overhead and possibly increased latency.
Common controlled access methods are:
- Reservation: stations reserve slots in advance. Reservation can be static (pre-assigned slots) or dynamic (stations contend to reserve upcoming slots). Reservation is useful for supporting guaranteed bandwidth and predictable delays.
- Polling: a central controller (the poller) sequentially polls stations asking if they have data. Only the polled station may transmit. Polling eliminates collisions but introduces polling overhead and may be inefficient if many stations are idle.
- Token passing: a special control frame (the token) circulates among stations in a logical order; only the station holding the token may transmit. Token passing provides orderly access and predictable maximum latency. Examples include Token Ring and some implementations of FDDI.
Channelization Protocols
Channelization divides the available channel resources so that several stations can transmit simultaneously without interfering, by allocating separate frequency, time or code resources to each user.
Three principal channelisation techniques are:
- FDMA - Frequency Division Multiple Access
- TDMA - Time Division Multiple Access
- CDMA - Code Division Multiple Access
FDMA
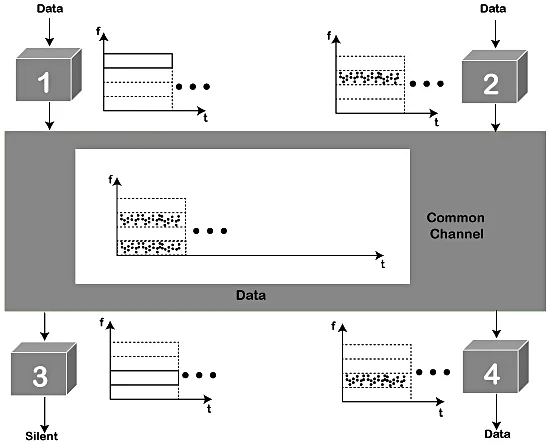
FDMA divides the total available bandwidth into non-overlapping frequency bands (channels) and assigns each user a distinct frequency band for the duration of the call or session. Users transmit simultaneously but on separate frequency bands. FDMA requires guard bands to limit interference between adjacent channels and simple filtering at receivers.
- Advantages: continuous transmission (no slotting), simple implementation for analogue and early digital systems.
- Disadvantages: inefficient use of spectrum if users are inactive; need for precise frequency allocation and filters; limited number of channels determined by bandwidth.
TDMA
TDMA shares a single frequency among multiple users by dividing time into repeating frames, each containing a number of time slots. Each user is assigned one or more time slots and transmits only in its assigned slots. Synchronisation is critical so that transmissions from different users do not overlap.
- Advantages: deterministic slot allocation, good spectral efficiency when traffic is bursty, easy to multiplex into higher-rate channels.
- Disadvantages: requires tight time synchronisation and guard times between slots; users transmit only in their slots (may introduce delay).
CDMA
CDMA uses spread spectrum techniques in which each user is assigned a unique spreading code sequence. All users transmit simultaneously over the same frequency band; the receiver separates users by correlating the received signal with the desired user's code. Orthogonal or pseudo-random codes allow multiple transmissions to co-exist.
- Advantages: good capacity for many simultaneous users, graceful degradation with increased load, flexible allocation without rigid slot or frequency assignment.
- Disadvantages: requires power control to mitigate the near-far problem, complex receivers, and careful code management to limit mutual interference.
Comparison and Practical Points
- Random access is simple and works well at low loads; efficiency degrades under heavy load due to collisions.
- Controlled access avoids collisions and provides predictable performance but introduces control overhead and can increase latency when many stations are idle.
- Channelization allows simultaneous transmissions and is suitable for systems requiring continuous bandwidth or many concurrent users, but it requires frequency/time/code planning and synchronisation.
- Wireless vs wired: collision detection (CSMA/CD) is feasible on many wired media; CSMA/CA and RTS/CTS are used in wireless networks where collision detection is impractical.
- Protocols often combine techniques. For example, IEEE 802.11 (Wi-Fi) uses CSMA/CA with RTS/CTS and contention windows; cellular systems combine TDMA/FDMA/CDMA ideas depending on the generation and standard.
Applications and Examples
- ALOHA - early radio networks and satellite access; inspires slotted ALOHA used in some random access channels.
- CSMA/CD - classic Ethernet (shared medium variants) used CSMA/CD and binary exponential backoff.
- CSMA/CA - IEEE 802.11 wireless LANs.
- Token passing - Token Ring, some industrial networks and certain deterministic LANs.
- FDMA, TDMA, CDMA - widely used in cellular systems and other multiuser wireless networks according to technology generation and requirements.
Summary
Media access protocols govern how multiple stations share a common transmission medium. The major approaches are random access (simple, works best at low load), controlled access (collision-free but with overhead), and channelization (divide resources by frequency, time or code). Practical systems choose or combine these approaches based on medium characteristics (wired or wireless), traffic patterns and the required trade-off between efficiency, delay, fairness and complexity.
 | Explore Courses for Computer Science Engineering (CSE) exam |  |
 | Get EduRev Notes directly in your Google search |  |



