SOC 2 & SOC 3 Reports
SOC 2 and SOC 3 Reports are attestation engagements performed by CPAs to evaluate and report on an organization's controls related to one or more Trust Services Criteria. These reports are critical for service organizations (e.g., cloud providers, data centers, SaaS companies) to demonstrate control effectiveness to users and stakeholders. SOC 2 provides detailed information for restricted use, while SOC 3 offers a general-use summary suitable for public distribution.
1. Trust Services Criteria (TSC)
The Trust Services Criteria framework consists of five categories of principles and criteria used to evaluate controls at service organizations. These criteria are established by the AICPA and form the foundation for SOC 2 and SOC 3 engagements.
1.1 Security (Common Criteria - Always Required)
Security is the foundational criterion and must be included in every SOC 2 or SOC 3 engagement. All other criteria are optional and selected based on user needs.
- Definition: Protection of system resources against unauthorized access, use, disclosure, modification, or destruction
- Key Control Areas: Access controls (logical and physical), network security, system hardening, intrusion detection, multi-factor authentication
- Example Controls: Password complexity requirements, firewall configurations, segregation of duties, background checks for personnel
- Exam Focus: Security is mandatory; other criteria are optional add-ons
1.2 Availability
Availability ensures the system is accessible and usable as committed or agreed upon in service level agreements (SLAs).
- Definition: System is available for operation and use as committed or agreed
- Key Control Areas: System monitoring, capacity planning, disaster recovery planning, business continuity, redundancy mechanisms
- Example Controls: Backup systems, load balancing, network monitoring tools, incident response procedures
- Performance Metrics: Uptime percentages (e.g., 99.9% availability), recovery time objectives (RTO), recovery point objectives (RPO)
- Common Trap: Availability differs from security; it focuses on uptime, not unauthorized access prevention
1.3 Processing Integrity
Processing Integrity addresses whether system processing is complete, valid, accurate, timely, and authorized.
- Definition: System processing is complete, valid, accurate, timely, and authorized to meet entity objectives
- Key Control Areas: Input validation, error handling, processing controls, output reconciliation, data transformation accuracy
- Example Controls: Edit checks on data entry, batch totals reconciliation, automated exception reports, dual authorization for transactions
- Exam Relevance: Critical for transaction processing systems, billing systems, payroll applications
- Common Confusion: Processing Integrity is about data processing accuracy, not data storage confidentiality
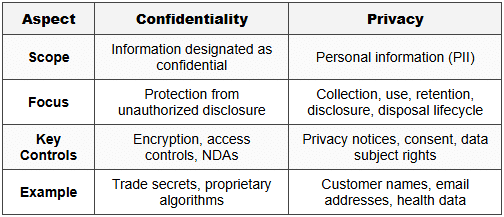
1.4 Confidentiality
Confidentiality protects information designated as confidential throughout its lifecycle.
- Definition: Information designated as confidential is protected as committed or agreed
- Key Control Areas: Data classification, encryption (at rest and in transit), access restrictions, confidentiality agreements, secure disposal
- Example Controls: Non-disclosure agreements (NDAs), AES-256 encryption, role-based access controls, data masking, secure shredding
- Scope Difference: Applies only to information designated as confidential, not all data (contrast with Privacy)
- Exam Alert: Confidentiality and Privacy are distinct criteria with different scopes
1.5 Privacy
Privacy addresses the collection, use, retention, disclosure, and disposal of personal information in accordance with privacy commitments.
- Definition: Personal information is collected, used, retained, disclosed, and disposed of in conformity with commitments and privacy notice
- Key Control Areas: Privacy notice communication, consent mechanisms, data subject rights (access, correction, deletion), third-party disclosure controls
- Example Controls: Cookie consent banners, opt-in/opt-out mechanisms, data retention policies, privacy impact assessments
- Regulatory Link: Aligns with GDPR, CCPA, HIPAA privacy requirements
- Critical Distinction: Privacy covers personal information lifecycle management; Confidentiality covers designated confidential data protection
1.6 Comparison Table: Confidentiality vs. Privacy
2. SOC 2 Type I vs. Type II Reports
SOC 2 reports come in two types, differing primarily in the time period evaluated and the nature of the CPA's opinion.
2.1 Type I Report
A Type I report evaluates the design and implementation of controls at a specific point in time.
- Time Period: As of a specific date (e.g., December 31, 20X1)
- CPA Opinion Addresses:
- Fairness of management's description of the system
- Suitability of design of controls to meet applicable Trust Services Criteria
- Whether controls were implemented as of the specified date
- Does NOT Include: Operating effectiveness testing or evaluation over a period of time
- Use Case: Initial assessments, new service organizations, preliminary evaluations before committing to Type II
- Exam Trap: Type I does NOT test operating effectiveness; it only evaluates design and implementation
2.2 Type II Report
A Type II report evaluates both design and operating effectiveness of controls over a minimum period of six months.
- Time Period: Over a period of time (minimum 6 months, typically 12 months for annual assessments)
- CPA Opinion Addresses:
- Fairness of management's description of the system
- Suitability of design of controls to meet applicable Trust Services Criteria
- Whether controls were operating effectively throughout the specified period
- Includes: Tests of controls, sample testing, observation of control operation, evidence of control execution
- Use Case: Most common for vendor due diligence, compliance requirements, customer assurance needs
- Standard Period: While 6 months is minimum, 12-month periods are industry standard for annual reporting cycles
- Exam Focus: Type II provides higher assurance because it tests controls over time, not just at a point in time
2.3 Comparison Table: Type I vs. Type II
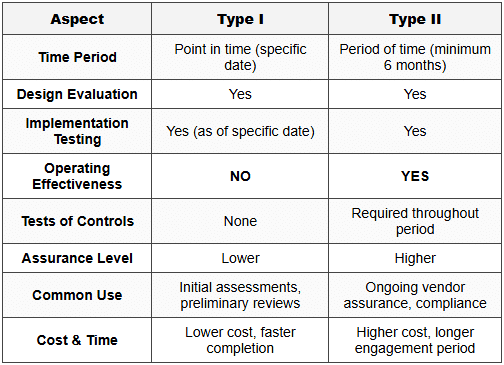
Critical Exam Point: The key differentiator is operating effectiveness testing over time. Type I = design + implementation at a point. Type II = design + implementation + operating effectiveness over a period.
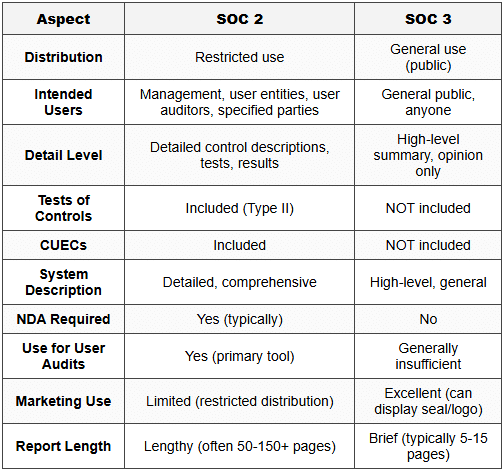
3. SOC 2 Restricted Use Reports
SOC 2 reports are restricted use reports intended for a limited audience with sufficient knowledge and understanding of the system.
3.1 Intended Users
- Management of Service Organization: Entity whose controls are being evaluated
- User Entities: Organizations that use the service organization's services (e.g., customers of a cloud provider)
- User Auditors: CPAs auditing the financial statements of user entities
- Regulators: Government agencies with oversight authority (when specified)
- Others: Specified parties as agreed (e.g., business partners, prospective customers under NDA)
3.2 Restriction Rationale
- Technical Nature: Reports contain detailed control descriptions and test results requiring specialized knowledge to interpret
- Context Required: Users must understand how service organization controls relate to their own internal control environment
- Complementary User Entity Controls (CUECs): SOC 2 reports assume user entities have certain controls in place; without this context, reports can be misinterpreted
- Confidentiality Concerns: Detailed control information may reveal proprietary processes or security vulnerabilities
3.3 Report Components (SOC 2)
- Independent Service Auditor's Report: CPA's opinion on management's description and control effectiveness
- Management's Assertion: Service organization management's written assertion about system description and controls
- System Description: Detailed narrative of the system, boundaries, control environment, and relevant controls
- Trust Services Criteria: Specific criteria selected for evaluation (Security always + optional others)
- Tests of Controls and Results (Type II only): Nature, timing, extent of tests performed and any exceptions identified
- Complementary User Entity Controls (CUECs): Controls that user entities should implement for effective system operation
- Other Information: Management responses to exceptions, corrective actions planned
3.4 Distribution Restrictions
- Restricted Use Paragraph: Report includes explicit language limiting distribution to specified parties
- NDA Requirements: Service organizations typically require NDAs before sharing SOC 2 reports with prospective customers
- No Public Distribution: SOC 2 reports cannot be posted publicly or distributed broadly without restriction
- Exam Alert: Restricted use is a defining characteristic of SOC 2; violating distribution restrictions can lead to professional liability issues
4. SOC 3 General Use Reports
SOC 3 reports are general use reports designed for broad public distribution without restriction.
4.1 Purpose and Users
- General Public: Anyone can read and rely on SOC 3 reports without specialized knowledge
- Marketing Tool: Service organizations display SOC 3 reports or seals on websites to demonstrate control effectiveness
- Prospective Customers: Provides high-level assurance without disclosing sensitive control details
- Broad Distribution: Can be freely shared, posted publicly, or included in marketing materials
4.2 Report Components (SOC 3)
- Independent Service Auditor's Report: CPA's opinion on whether system achieved Trust Services Criteria (opinion only, no detailed tests)
- Management's Assertion: Brief statement from management about system and controls
- System Description: High-level, general description without sensitive details
- Trust Services Criteria: Identification of criteria met (Security + any optional criteria)
- NO Detailed Control Descriptions: Unlike SOC 2, does not include specific control activities
- NO Tests of Controls Details: Does not disclose testing procedures, sample sizes, or exceptions
- NO CUECs: Does not identify complementary user entity controls
4.3 SOC 3 Limitations
- Less Detailed: Provides opinion on criteria achievement but lacks operational detail
- Insufficient for User Auditors: User auditors generally cannot rely on SOC 3 for financial statement audit purposes; they require SOC 2 detail
- Not Suitable for Detailed Risk Assessment: Organizations performing vendor risk management typically need SOC 2 reports
- Type II Only: SOC 3 reports are typically Type II (operating effectiveness over time); Type I SOC 3 reports are rare
4.4 Comparison Table: SOC 2 vs. SOC 3
5. Engagement Performance and Reporting Standards
5.1 Applicable Standards
- AT-C Section 105: Concepts Common to All Attestation Engagements (establishes foundational attestation principles)
- AT-C Section 205: Examination Engagements (SOC 2 and SOC 3 are examination-level attestation engagements)
- AT-C Section 320: Reporting on an Examination of Controls at a Service Organization Relevant to User Entities' Internal Control Over Financial Reporting (SOC 1, not SOC 2/3)
- TSP Section 100: Trust Services Principles and Criteria (provides the Trust Services Criteria framework)
- AICPA Guide: SOC 2 Reporting Guide provides implementation guidance
5.2 Service Auditor Requirements
- Independence: Must be independent of service organization under AICPA Code of Professional Conduct
- Competence: Requires specialized knowledge in IT controls, information security, and attestation standards
- Due Professional Care: Exercise professional skepticism and obtain sufficient appropriate evidence
- Quality Control: Firm must have system of quality control per SQCS No. 8
5.3 Management's Responsibilities
- System Description: Prepare accurate, complete description of the system and boundaries
- Assertion: Provide written assertion about description fairness and control effectiveness
- Control Design and Implementation: Design, implement, and maintain effective controls
- Evidence Provision: Provide auditor with access to personnel, systems, and documentation
- Remediation: Address control deficiencies identified during examination
5.4 Service Auditor Procedures
For Type I engagements:
- Obtain understanding of system through inquiry, observation, inspection
- Evaluate whether description fairly presents the system
- Evaluate suitability of control design to meet Trust Services Criteria
- Determine whether controls were implemented as of specified date
For Type II engagements (includes Type I procedures plus):
- Perform tests of controls to evaluate operating effectiveness throughout period
- Test control operation through inquiry, observation, inspection, reperformance
- Determine appropriate sample sizes based on risk, control frequency, population size
- Evaluate and report exceptions, deviations, control failures
- Assess whether exceptions affect opinion on control effectiveness
5.5 Opinion Types
- Unmodified Opinion: Service auditor concludes controls are suitably designed and operating effectively (Type II) or implemented (Type I) with no material exceptions
- Modified Opinion:
- Qualified: Material exceptions exist but do not completely undermine control effectiveness
- Adverse: Controls are not suitably designed or not operating effectively to meet criteria
- Disclaimer: Unable to obtain sufficient appropriate evidence (scope limitation)
6. Complementary User Entity Controls (CUECs)
CUECs are controls that user entities must implement for service organization controls to operate effectively. Understanding CUECs is critical for proper SOC report interpretation.
6.1 Definition and Importance
- Definition: Controls that management of the service organization assumes user entities have in place
- Shared Responsibility Model: Control effectiveness depends on both service organization and user entity controls working together
- Example Scenario: Cloud provider encrypts data in transit (service org control), but user entity must protect authentication credentials (CUEC)
- Risk: If user entities do not implement CUECs, overall control objectives may not be achieved despite effective service organization controls
6.2 Common Examples of CUECs
- Access Management: User entities must promptly communicate terminations to service organization for user access removal
- Password Security: User entities must enforce strong passwords and protect credentials for accessing service organization systems
- Data Input Accuracy: User entities must ensure data entered into service organization systems is accurate and complete
- Change Management: User entities must test and approve system changes before implementation in production
- Output Review: User entities must review reports and outputs from service organization for accuracy and completeness
6.3 User Auditor Considerations
- Identify Relevant CUECs: Review SOC 2 report Section IV to identify which CUECs apply to user entity
- Evaluate Implementation: Determine whether user entity has implemented identified CUECs
- Test User Entity Controls: Perform tests of controls at user entity for relevant CUECs
- Impact on Financial Statement Audit: Ineffective CUECs may require additional substantive testing or affect audit opinion
- Exam Focus: User auditors cannot simply rely on SOC 2 report; they must verify user entity has implemented CUECs
7. Subservice Organizations and Carve-Out Method
7.1 Subservice Organizations
- Definition: Service organization that provides services to another service organization that are part of the service organization's system
- Example: SaaS provider (primary service org) uses AWS for infrastructure hosting (subservice org)
- Control Responsibility: Some controls relevant to user entities are performed by subservice organization, not primary service organization
7.2 Carve-Out Method (Exclusive Method)
- Definition: Service organization's description and service auditor's report exclude subservice organization's controls
- Management Assertion: Limited to controls at service organization; does not cover subservice organization
- Service Auditor Testing: Does not test or opine on subservice organization controls
- User Auditor Action Required: Must obtain separate SOC report from subservice organization to evaluate those controls
- Disclosure: SOC report clearly identifies which functions are performed by subservice organization and are carved out
7.3 Inclusive Method
- Alternative Approach: Service organization includes subservice organization's relevant controls in system description
- Service Auditor Testing: Tests controls at both service organization and subservice organization
- Single Report: Users receive one comprehensive report covering all relevant controls
- Less Common: Requires service auditor access to subservice organization, which may not be feasible
8. Common Exam Pitfalls and Key Takeaways
8.1 Trap Alert: Common Student Mistakes
- Confusing Type I and Type II: Type I = point in time, no operating effectiveness. Type II = period of time, includes operating effectiveness testing
- Assuming All Criteria Are Required: Only Security is mandatory; Availability, Processing Integrity, Confidentiality, Privacy are optional
- Mixing Up Confidentiality and Privacy: Confidentiality = designated confidential data protection. Privacy = personal information lifecycle management per commitments
- Thinking SOC 3 Is Sufficient for User Auditors: SOC 3 lacks detail needed for user auditor reliance; SOC 2 is required for financial statement audit purposes
- Forgetting CUECs: User auditors must verify user entity implemented CUECs; cannot rely solely on SOC 2 report
- Assuming Restricted Use Means Confidential: Restricted use means limited to specified parties with knowledge; it's about interpretive context, not necessarily confidentiality
- Overlooking Carve-Outs: When subservice organizations are carved out, user auditors must obtain separate SOC reports for complete control evaluation
8.2 Memory Aid: SAPCP (Security Always, Privacy Criteria Plus)
Use SAPCP to remember the five Trust Services Criteria:
- S - Security (always required)
- A - Availability
- P - Processing Integrity
- C - Confidentiality
- P - Privacy
8.3 Memory Aid: Type I vs. Type II
- Type I = "I"mplemented (at a point)
- Type II = "II"me period (operating effectiveness over time)
9. Exam-Relevant Practice Questions with Full Solutions
9.1 Question 1: Trust Services Criteria Selection
Question: A cloud storage provider is obtaining a SOC 2 report. The provider wants to assure customers that data is protected from unauthorized access and that the system meets committed uptime levels. Which Trust Services Criteria must be included in the engagement?
Choices:
- Security only
- Security and Confidentiality
- Security and Availability
- Security, Availability, and Confidentiality
Correct Answer: C - Security and Availability
Full Solution:
- Security is mandatory for all SOC 2 engagements and addresses protection from unauthorized access
- Availability addresses system uptime and meeting committed service levels (SLAs)
- Confidentiality would only be necessary if specific data is designated as confidential; the question does not indicate this requirement
- Protection from unauthorized access is covered by Security (not Confidentiality)
- Therefore, Security (required) + Availability (for uptime commitments) = Answer C
9.2 Question 2: Type I vs. Type II Report Selection
Question: A user auditor is evaluating controls at a service organization that processes payroll transactions for the user entity. The user auditor needs assurance that controls operated effectively throughout the fiscal year. Which report should the user auditor request?
Choices:
- SOC 2 Type I report
- SOC 2 Type II report
- SOC 3 Type I report
- SOC 3 Type II report
Correct Answer: B - SOC 2 Type II report
Full Solution:
- User auditor needs operating effectiveness testing, which requires Type II (not Type I)
- User auditor needs detailed information for financial statement audit reliance, which requires SOC 2 (not SOC 3)
- SOC 3 reports lack the detail necessary for user auditor reliance (no test details, no CUECs)
- Type I only evaluates design and implementation at a point in time, not operating effectiveness over the fiscal year
- Therefore, SOC 2 Type II is the only report providing operating effectiveness evidence over a period with sufficient detail for user auditor needs
9.3 Question 3: Complementary User Entity Controls
Question: A service organization's SOC 2 Type II report includes a complementary user entity control (CUEC) stating: "User entities are responsible for immediately notifying the service organization when employee access should be terminated." The user auditor identifies that the user entity does not have a formal process to notify the service organization of terminations. What should the user auditor do?
Choices:
- Rely on the service organization's controls because the SOC 2 report had an unmodified opinion
- Test the service organization's access removal controls more extensively
- Implement additional substantive procedures or test alternative user entity controls addressing termination notifications
- Disclaim an opinion on internal controls over financial reporting
Correct Answer: C - Implement additional substantive procedures or test alternative user entity controls addressing termination notifications
Full Solution:
- The CUEC is a shared responsibility; the service organization's controls assume user entities implement this control
- Without effective termination notification from user entity, the service organization cannot timely remove access
- Even though the service organization's controls received an unmodified opinion, this does not eliminate the need for effective CUECs at the user entity
- User auditor cannot simply rely on SOC report when CUECs are not implemented
- User auditor must either: (1) test alternative compensating controls at user entity, or (2) perform additional substantive procedures to address the risk
- Disclaiming opinion is too severe unless the deficiency creates a scope limitation
- Testing service org controls more extensively doesn't address the gap in user entity controls
9.4 Question 4: SOC 2 vs. SOC 3 Distribution
Question: A service organization wants to display an attestation seal on its public website to demonstrate control effectiveness to potential customers. Which report type is most appropriate for this purpose?
Choices:
- SOC 2 Type I report
- SOC 2 Type II report
- SOC 3 report
- Either SOC 2 or SOC 3, as both can be publicly distributed
Correct Answer: C - SOC 3 report
Full Solution:
- SOC 2 reports are restricted use and cannot be publicly distributed or posted on websites
- SOC 3 reports are general use and specifically designed for public distribution and marketing purposes
- SOC 3 allows service organizations to display attestation seals or logos on websites
- Answer D is incorrect because SOC 2 cannot be publicly distributed without violating distribution restrictions
- SOC 3 provides opinion-level assurance suitable for general public without disclosing sensitive control details
9.5 Question 5: Carve-Out Method Implications
Question: A user auditor is reviewing a SOC 2 Type II report for a SaaS provider. The report uses the carve-out method and identifies that data center hosting services are provided by a subservice organization. The service auditor's opinion excludes the subservice organization's controls. What action should the user auditor take?
Choices:
- Rely on the SOC 2 report as written because it has an unmodified opinion
- Request that the service organization obtain an inclusive method SOC 2 report
- Obtain and evaluate a separate SOC 2 report from the subservice organization (data center provider)
- Perform direct testing of controls at the subservice organization
Correct Answer: C - Obtain and evaluate a separate SOC 2 report from the subservice organization (data center provider)
Full Solution:
- Under the carve-out method, subservice organization controls are excluded from the service organization's SOC report
- The service auditor's opinion does not cover subservice organization controls
- User auditor needs assurance over all relevant controls, including those at subservice organization
- Standard approach: obtain separate SOC report from subservice organization to evaluate carved-out controls
- Answer A is incorrect because relying only on the carved-out report leaves a gap in control evaluation
- Answer B is impractical; user auditor cannot require service organization to change report method after issuance
- Answer D is generally not feasible or cost-effective; obtaining SOC report is standard practice
- If subservice organization SOC report is not available, user auditor may need to perform alternative procedures or modify opinion
9.6 Question 6: Privacy vs. Confidentiality Criteria
Question: A healthcare service organization processes patient health records. The organization wants a SOC 2 report that addresses compliance with HIPAA privacy requirements regarding collection, use, and disclosure of patient information. Which Trust Services Criterion is most relevant?
Choices:
- Security
- Confidentiality
- Privacy
- Processing Integrity
Correct Answer: C - Privacy
Full Solution:
- Privacy criterion addresses collection, use, retention, disclosure, and disposal of personal information in accordance with privacy commitments and regulations
- HIPAA privacy requirements align with Privacy criterion scope (lifecycle management of personal health information)
- Confidentiality addresses protection of information designated as confidential from unauthorized disclosure, but does not address collection, use, and disclosure practices
- Security addresses protection from unauthorized access (always required but does not specifically address privacy practices)
- Processing Integrity addresses accuracy and completeness of processing, not privacy practices
- For HIPAA compliance assurance, Privacy (and Security) criteria should be included
9.7 Question 7: Service Auditor Opinion Modification
Question: During a SOC 2 Type II engagement, the service auditor identifies that user access reviews are designed to be performed quarterly, but testing reveals that reviews were not performed for two consecutive quarters during the examination period. Management implemented compensating detective controls that identified no unauthorized access. How should the service auditor report this finding?
Choices:
- Issue an unmodified opinion because compensating controls were effective
- Report the exception but issue an unmodified opinion if compensating controls adequately mitigate risk
- Issue a qualified opinion due to the control deviation
- Issue an adverse opinion because the control did not operate as designed
Correct Answer: B - Report the exception but issue an unmodified opinion if compensating controls adequately mitigate risk
Full Solution:
- Service auditor must report all exceptions identified during testing, including control deviations
- Exception should be clearly described in the test of controls section of the report
- Service auditor evaluates whether compensating controls adequately address the risk
- If compensating controls are effective and the overall control objective is met, an unmodified opinion may still be appropriate
- Answer A is incorrect because the exception must be disclosed even if opinion is unmodified
- Qualified or adverse opinions are appropriate when exceptions are material and compensating controls do not adequately mitigate risk
- The determination depends on risk assessment and compensating control effectiveness
- Transparency is critical: users need to know about exceptions to make informed decisions
Conclusion: SOC 2 and SOC 3 reports are essential attestation engagements for service organizations to demonstrate control effectiveness. Mastering the Trust Services Criteria framework, understanding Type I versus Type II distinctions, recognizing restricted versus general use reporting differences, and properly evaluating CUECs are critical for CPA Exam success and professional practice. Service auditors must apply rigorous examination procedures per attestation standards, while user auditors must understand how to properly use these reports in financial statement audits. The interplay between service organization controls, subservice organization controls, and user entity controls creates a shared responsibility model that requires careful evaluation and professional judgment.





