IDS and IPS
IDS and IPS
In today's interconnected world, computer networks face constant threats from malicious actors trying to breach security, steal data, or disrupt operations. Two critical security appliances that help protect networks are Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS). These systems act as watchful guardians, monitoring network traffic and system activities to identify and respond to potential security threats. While they share similar functions, they differ fundamentally in how they respond to detected threats. This document will guide you through everything you need to know about IDS and IPS, from basic concepts to practical implementations.
Understanding Network Intrusions
Before diving into IDS and IPS, we need to understand what we're protecting against. A network intrusion is any unauthorized activity on a computer network that attempts to access, manipulate, disable, or steal information from the system. These intrusions can take many forms:
- Unauthorized access: Someone gaining entry to systems they shouldn't have access to
- Malware infections: Viruses, worms, trojans, and other malicious software
- Denial of Service (DoS) attacks: Overwhelming systems to make them unavailable
- Port scanning: Probing networks to find vulnerabilities
- Data exfiltration: Stealing sensitive information from the network
- Exploitation of vulnerabilities: Taking advantage of weaknesses in software or configurations
Think of network intrusions like burglaries in the physical world. Just as burglars might try different methods to break into a building-picking locks, breaking windows, or sneaking through unlocked doors-cyber attackers use various techniques to penetrate network defenses.
What is an Intrusion Detection System (IDS)?
An Intrusion Detection System (IDS) is a security appliance or software application that monitors network traffic and system activities for malicious behavior or policy violations. When suspicious activity is detected, the IDS generates alerts to notify security administrators.
Key Characteristics of IDS
- Passive monitoring: IDS operates in a monitoring mode, observing traffic without interfering with it
- Detection and alerting: The primary function is to detect threats and notify administrators
- No direct prevention: IDS does not actively block or stop threats
- Operates out-of-band: Typically placed so that a copy of traffic is sent to it for analysis
An IDS is like a security camera system in a building. It watches everything that happens, records suspicious activity, and alerts security personnel when something looks wrong. However, it doesn't physically stop the intruder-that's the job of security guards (or in network terms, an IPS or firewall).
How IDS Works
An IDS continuously analyzes network packets and system logs, comparing observed patterns against known attack signatures and behavioral baselines. The process typically follows these steps:
- Data collection: The IDS captures network packets or system event logs
- Analysis: Collected data is analyzed using detection methods (signature-based or anomaly-based)
- Pattern matching: The system compares traffic patterns against its database of known threats
- Alert generation: When a match or anomaly is found, an alert is created
- Logging: All detected events are logged for future analysis and forensics
- Notification: Administrators are notified through various channels (email, dashboard, SIEM integration)
What is an Intrusion Prevention System (IPS)?
An Intrusion Prevention System (IPS) is an active security appliance that not only detects threats like an IDS but also takes automatic action to prevent or block those threats from succeeding. The IPS sits directly in the network traffic path and can drop malicious packets, block connections, or reset sessions in real-time.
Key Characteristics of IPS
- Active prevention: Takes immediate action to stop detected threats
- Inline deployment: Positioned directly in the traffic path between network segments
- Real-time blocking: Can drop packets, terminate connections, or redirect traffic
- Operates in-band: All traffic must pass through the IPS
- Detection and response: Combines detection capabilities with automated response mechanisms
If an IDS is like a security camera, an IPS is like an automated security gate with a guard. It not only watches who's trying to enter but also physically blocks anyone who looks suspicious or doesn't have proper credentials-all automatically and in real-time.
How IPS Works
The IPS operates similarly to IDS in detection but adds enforcement capabilities:
- Inline traffic inspection: All network traffic flows through the IPS
- Real-time analysis: Packets are analyzed as they pass through
- Threat detection: Malicious patterns are identified using signatures and anomaly detection
- Automated response: The IPS takes immediate action based on configured policies
- Traffic forwarding: Legitimate traffic is allowed to continue to its destination
- Logging and alerting: Actions taken are logged and administrators are notified
IDS vs IPS: Key Differences
While IDS and IPS share similar detection capabilities, their fundamental difference lies in their response to threats and network positioning:
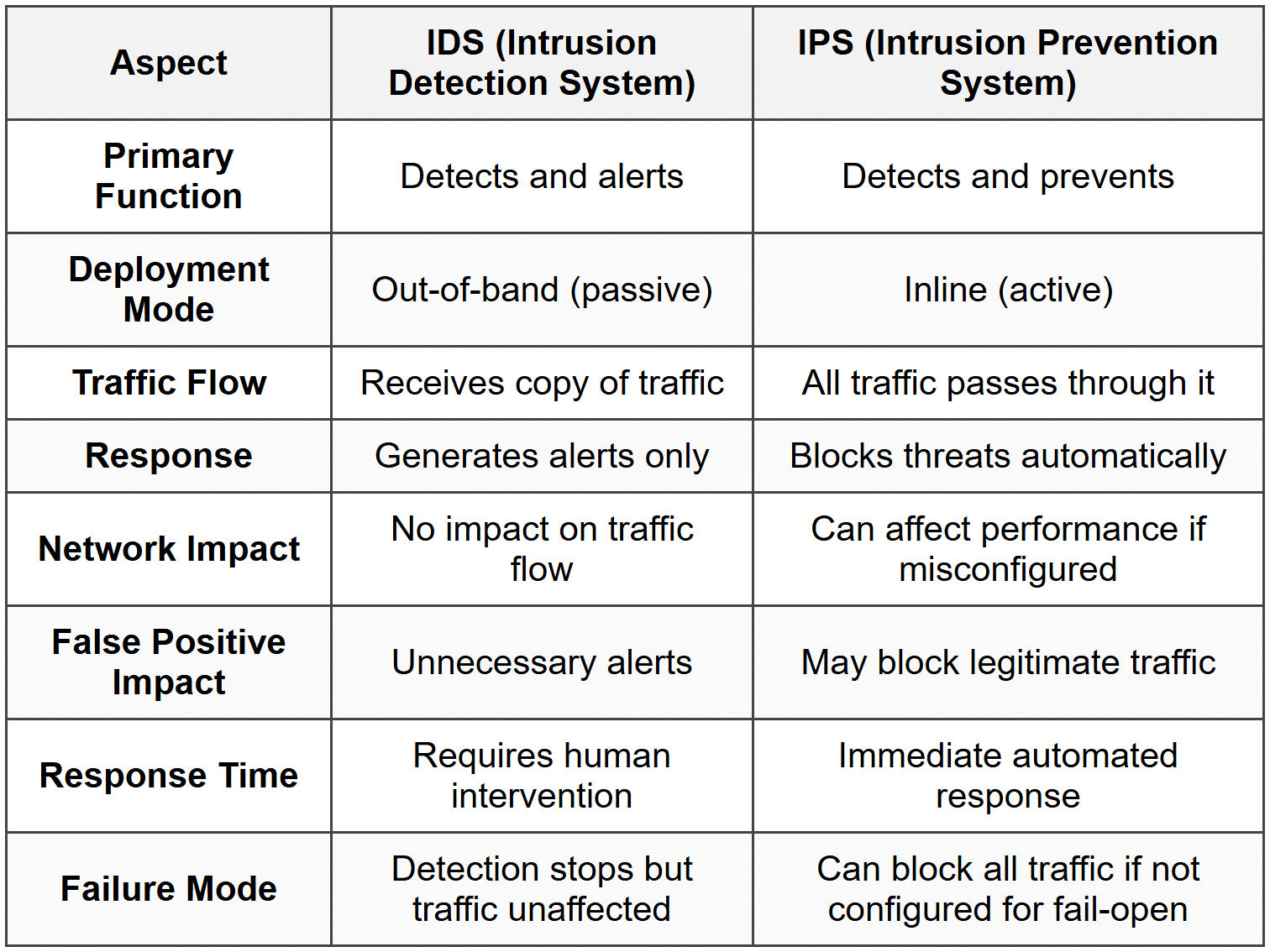
Important Note: The choice between IDS and IPS depends on your organization's security requirements, risk tolerance, and network architecture. Many organizations use both: IPS for critical network segments requiring active protection, and IDS for monitoring and forensic analysis.
Types of IDS and IPS
Both IDS and IPS can be categorized based on their deployment location and what they monitor:
Based on Deployment Location
Network-Based IDS/IPS (NIDS/NIPS)
Network-Based Intrusion Detection/Prevention Systems monitor network traffic at strategic points in the network infrastructure. They analyze packets flowing across the network segment they're protecting.
Characteristics:
- Monitors all network traffic on a specific network segment
- Typically deployed at network boundaries, before/after firewalls, or between network segments
- Can protect multiple hosts simultaneously
- Analyzes packet headers and payloads
- Detects network-based attacks like port scans, DoS attacks, and protocol violations
Common Placement Points:
- Between the internet and perimeter firewall
- Behind the firewall protecting the internal network
- In the DMZ (Demilitarized Zone) protecting public-facing servers
- Between network segments (e.g., separating departments)
Host-Based IDS/IPS (HIDS/HIPS)
Host-Based Intrusion Detection/Prevention Systems are installed on individual computers or servers and monitor activities on that specific host.
Characteristics:
- Monitors activities on a single host
- Analyzes system logs, file integrity, system calls, and application behavior
- Can detect attacks that network-based systems might miss
- Protects against insider threats and local attacks
- Monitors file system changes, registry modifications, and running processes
What HIDS/HIPS Monitors:
- System and application logs
- File system integrity (unauthorized changes to files)
- Running processes and services
- System configuration changes
- User login attempts and privilege escalations
- Registry changes (on Windows systems)
Wireless IDS/IPS (WIDS/WIPS)
Wireless Intrusion Detection/Prevention Systems are specialized systems designed specifically to monitor and protect wireless networks.
Characteristics:
- Monitors wireless network traffic (Wi-Fi)
- Detects rogue access points
- Identifies unauthorized wireless clients
- Detects wireless-specific attacks (evil twin, deauthentication attacks)
- Can locate physical position of rogue devices
Based on Detection Method
Regardless of deployment type, all IDS and IPS systems use one or more detection methods:
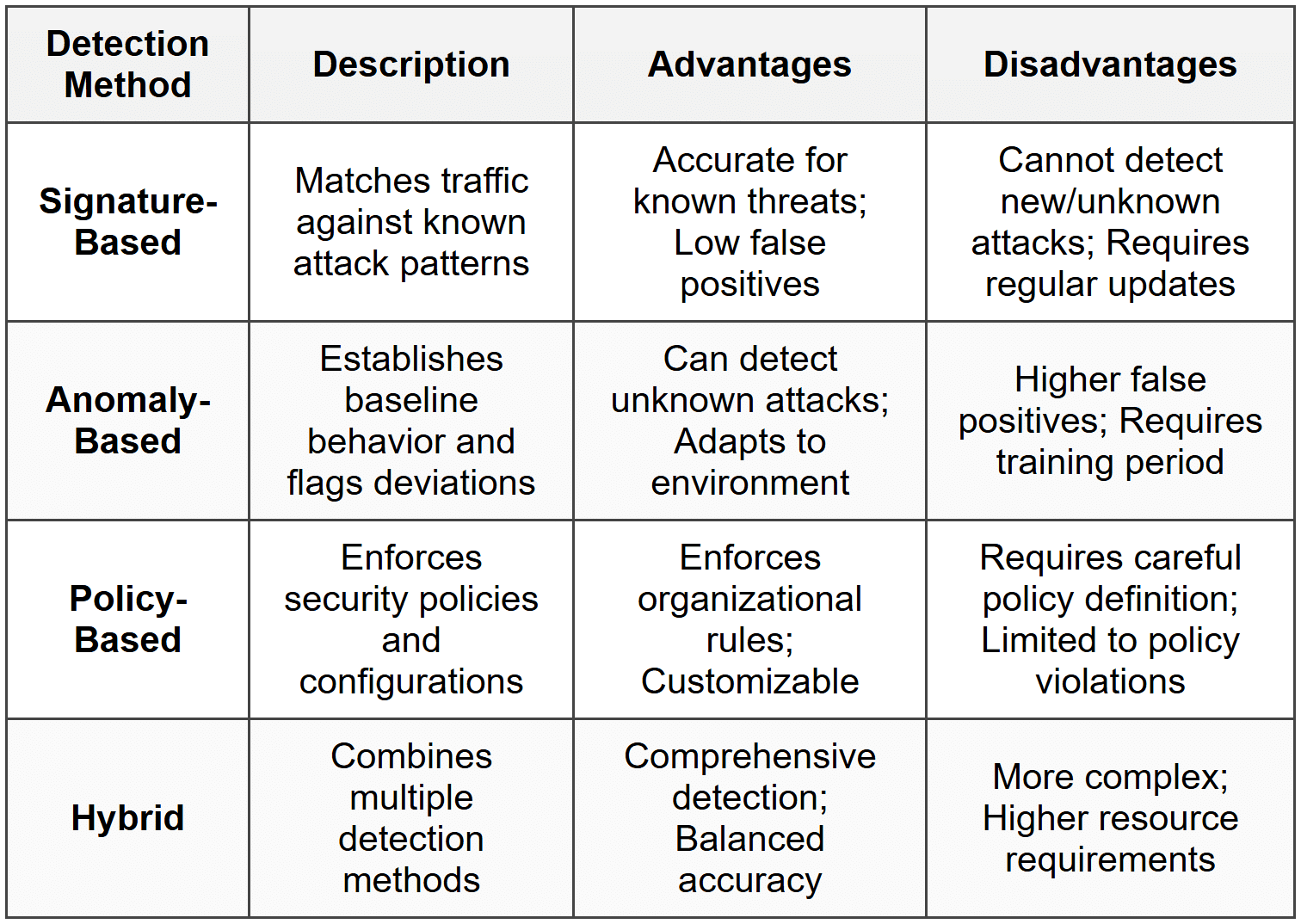
Detection Methods in Detail
Signature-Based Detection
Signature-based detection (also called pattern matching or misuse detection) works by comparing observed traffic or activities against a database of known attack signatures. A signature is a specific pattern that identifies a particular type of attack or malicious behavior.
How It Works:
- The IDS/IPS maintains a database of attack signatures
- Incoming traffic or system activities are analyzed
- The system searches for matches with known signatures
- When a match is found, an alert is generated (IDS) or action is taken (IPS)
Example Signatures:
- Specific byte sequences in packet payloads that indicate malware
- Patterns of network requests characteristic of SQL injection attempts
- Command sequences typical of buffer overflow exploits
- Traffic patterns indicative of port scanning activity
Signature-based detection is like having a "most wanted" poster book at a security checkpoint. Guards (the IDS/IPS) compare every person (network packet) against the photos in the book. If there's a match, they know it's a known criminal. However, if a criminal who's not in the book tries to enter, they'll pass through undetected.
Advantages:
- Very accurate for known attacks
- Low false positive rate
- Can identify specific attack types
- Fast processing and decision-making
Limitations:
- Cannot detect new or unknown attacks (zero-day exploits)
- Requires constant signature updates
- Attackers can modify attacks to evade known signatures
- Signature database can become very large
Anomaly-Based Detection
Anomaly-based detection (also called behavioral detection) establishes a baseline of normal network behavior and then identifies deviations from this baseline as potential threats.
How It Works:
- Training phase: The system observes network traffic during a "normal" period to learn typical behavior
- Baseline creation: Statistical models are created representing normal traffic patterns, protocol usage, bandwidth consumption, etc.
- Monitoring phase: Ongoing traffic is compared against the baseline
- Anomaly detection: Significant deviations from the baseline trigger alerts
What Constitutes Normal Behavior:
- Typical bandwidth usage patterns
- Standard protocols and ports used
- Normal connection frequencies and durations
- Expected traffic volumes at different times
- Usual applications and services running
- Typical user behavior patterns
Anomaly-based detection is like a parent who knows their child's normal behavior. If the child usually comes home at 3 PM but suddenly arrives at midnight, that's an anomaly worth investigating. The parent doesn't need to have seen this specific situation before-they just know it's unusual and potentially concerning.
Advantages:
- Can detect previously unknown attacks (zero-day exploits)
- Doesn't require constant signature updates
- Adapts to environment changes over time
- Effective against insider threats and unusual behavior
Limitations:
- Higher false positive rate
- Requires a learning period to establish baseline
- Legitimate changes in behavior may trigger false alarms
- If trained on compromised data, malicious behavior becomes "normal"
- More computationally intensive
Policy-Based Detection
Policy-based detection enforces specific security policies defined by the organization. It checks whether network activities comply with established rules and configurations.
Examples of Policies:
- No peer-to-peer file sharing applications allowed
- Only specific IP addresses can access database servers
- No outbound traffic on port 25 except from mail servers
- Specific protocols are prohibited on the network
- Administrative access only during business hours
Advantages:
- Enforces organizational security requirements
- Highly customizable to specific needs
- Clear rules with predictable behavior
Limitations:
- Requires careful policy creation and maintenance
- Only detects policy violations, not all attacks
- Overly restrictive policies can impact productivity
IDS and IPS Architecture and Deployment
Network-Based IDS/IPS Deployment
The placement of network-based IDS/IPS devices is critical to their effectiveness. Common deployment scenarios include:
1. Perimeter Deployment
Placing IDS/IPS at the network perimeter monitors all traffic entering and leaving the network:
- Before the firewall: Sees all attack attempts including those the firewall will block; useful for threat intelligence
- After the firewall: Monitors traffic that passed firewall rules; reduces load by only analyzing allowed traffic
- In DMZ: Protects public-facing servers like web and email servers
2. Internal Deployment
Placing IDS/IPS internally monitors traffic between network segments:
- Between departments or security zones
- Protecting sensitive data centers
- Monitoring traffic to/from critical servers
- Detecting lateral movement during attacks
- Identifying insider threats
3. Distributed Deployment
Multiple IDS/IPS devices are deployed throughout the network with centralized management:
- Sensors at various network points collect data
- Central management console aggregates and analyzes data
- Provides comprehensive network visibility
- Enables correlation of events across the network
Traffic Acquisition Methods
For IDS/IPS to analyze traffic, it must first acquire it. Different methods are used depending on whether the system is inline (IPS) or passive (IDS):
Network TAP (Test Access Point)
A network TAP is a hardware device that creates an exact copy of network traffic without disrupting the flow:
- Physical device inserted into network cable
- Sends copy of all traffic to IDS
- No impact on network performance
- Completely passive-cannot be detected
- Reliable even during high traffic loads
SPAN Port (Switched Port Analyzer)
A SPAN port (also called mirror port) is a switch feature that mirrors traffic from one or more ports to a monitoring port:
- Configured on network switches
- Can mirror specific ports, VLANs, or all traffic
- No additional hardware required
- May drop packets during high traffic loads
- Can impact switch performance
Inline Deployment (IPS)
For IPS, the device is placed directly in the traffic path:
- All traffic flows through the IPS
- Can actively block or modify traffic
- Introduces latency (typically minimal)
- Single point of failure unless redundancy is implemented
- Requires careful tuning to avoid blocking legitimate traffic
IDS and IPS Components
A complete IDS or IPS solution consists of several key components working together:
1. Sensors (Network Interface)
The sensor is the component that captures network traffic or monitors host activities. In network-based systems, sensors have network interfaces configured in promiscuous mode to capture all packets on the network segment.
Functions:
- Captures packets from the network
- Performs initial packet processing
- Filters traffic based on configuration
- Forwards data to analysis engine
2. Analysis Engine
The analysis engine (also called detection engine) is the core component that examines captured data and identifies potential threats.
Functions:
- Processes captured packets or system logs
- Applies detection algorithms (signature, anomaly, policy-based)
- Matches patterns against signature database
- Compares behavior against baseline
- Determines severity of detected events
- Generates alerts for suspicious activity
3. Signature/Rule Database
The signature database contains patterns and rules used to identify known attacks and malicious behavior.
Contents:
- Attack signatures and patterns
- Protocol anomaly definitions
- Detection rules and logic
- Regular expressions for pattern matching
- Vulnerability-specific exploits
Maintenance:
- Requires regular updates from vendors or security organizations
- Custom rules can be added by administrators
- Rules can be enabled/disabled based on environment
- Tuning required to reduce false positives
4. Management Console
The management console provides the interface for administrators to configure, monitor, and manage the IDS/IPS.
Capabilities:
- Real-time alert viewing and management
- Configuration of sensors and detection rules
- Policy creation and management
- Report generation and analysis
- Dashboard with security metrics
- User management and access control
5. Database/Storage
IDS/IPS systems maintain databases to store alerts, logs, and configuration information:
- Stores alerts and events
- Archives packet captures for forensics
- Maintains historical data for trend analysis
- Supports searching and querying capabilities
- Enables long-term storage for compliance
6. Response Component (IPS)
For IPS systems, the response component takes active measures to prevent detected threats:
Actions:
- Drop/block malicious packets
- Terminate TCP connections (send RST packets)
- Block IP addresses (temporary or permanent)
- Redirect traffic to honeypots or quarantine zones
- Trigger firewall rules
- Scrub malicious content from packets while allowing benign parts through
Common Attacks Detected by IDS and IPS
IDS and IPS are designed to detect various types of network attacks and malicious activities:
Reconnaissance Attacks
Reconnaissance attacks are attempts to gather information about a network before launching an actual attack:
- Port scanning: Probing which ports are open on target systems
- Network mapping: Discovering network topology and connected devices
- Vulnerability scanning: Identifying weaknesses in systems and applications
- OS fingerprinting: Determining operating systems running on targets
- Ping sweeps: Identifying active hosts on a network
Reconnaissance is like a burglar walking through a neighborhood noting which houses have security systems, which windows are unlocked, and when residents are typically away. The burglar hasn't committed a crime yet, but the activity is suspicious and indicates harmful intent.
Denial of Service (DoS) and Distributed Denial of Service (DDoS)
DoS/DDoS attacks attempt to overwhelm systems or networks, making them unavailable to legitimate users:
- SYN flood: Overwhelming servers with TCP connection requests
- UDP flood: Flooding targets with UDP packets
- ICMP flood (Ping flood): Overwhelming with ICMP echo requests
- HTTP flood: Overloading web servers with HTTP requests
- Amplification attacks: Using third-party servers to amplify attack traffic
Exploitation Attacks
These attacks exploit vulnerabilities in software or systems to gain unauthorized access or execute malicious code:
- Buffer overflow: Overwriting memory to execute arbitrary code
- SQL injection: Injecting malicious SQL code into database queries
- Cross-site scripting (XSS): Injecting malicious scripts into web pages
- Remote code execution: Executing code on remote systems
- Privilege escalation: Gaining higher access levels than authorized
Malware and Virus Activity
IDS/IPS can detect various forms of malware based on network behavior or signatures:
- Virus and worm propagation: Self-replicating malware spreading through the network
- Trojan horse activity: Malicious programs masquerading as legitimate software
- Ransomware: Malware that encrypts files and demands payment
- Botnet command-and-control traffic: Communication between infected systems and attacker servers
- Backdoor access: Unauthorized remote access mechanisms
Policy Violations
Activities that violate organizational security policies:
- Use of prohibited applications or protocols
- Access to restricted websites or services
- Unauthorized network connections
- Data exfiltration attempts
- Use of unauthorized encryption or tunneling
Insider Threats
Malicious or negligent activities by authorized users:
- Unauthorized access to sensitive data
- Excessive data downloads
- After-hours access to restricted systems
- Unusual file access patterns
- Privilege abuse
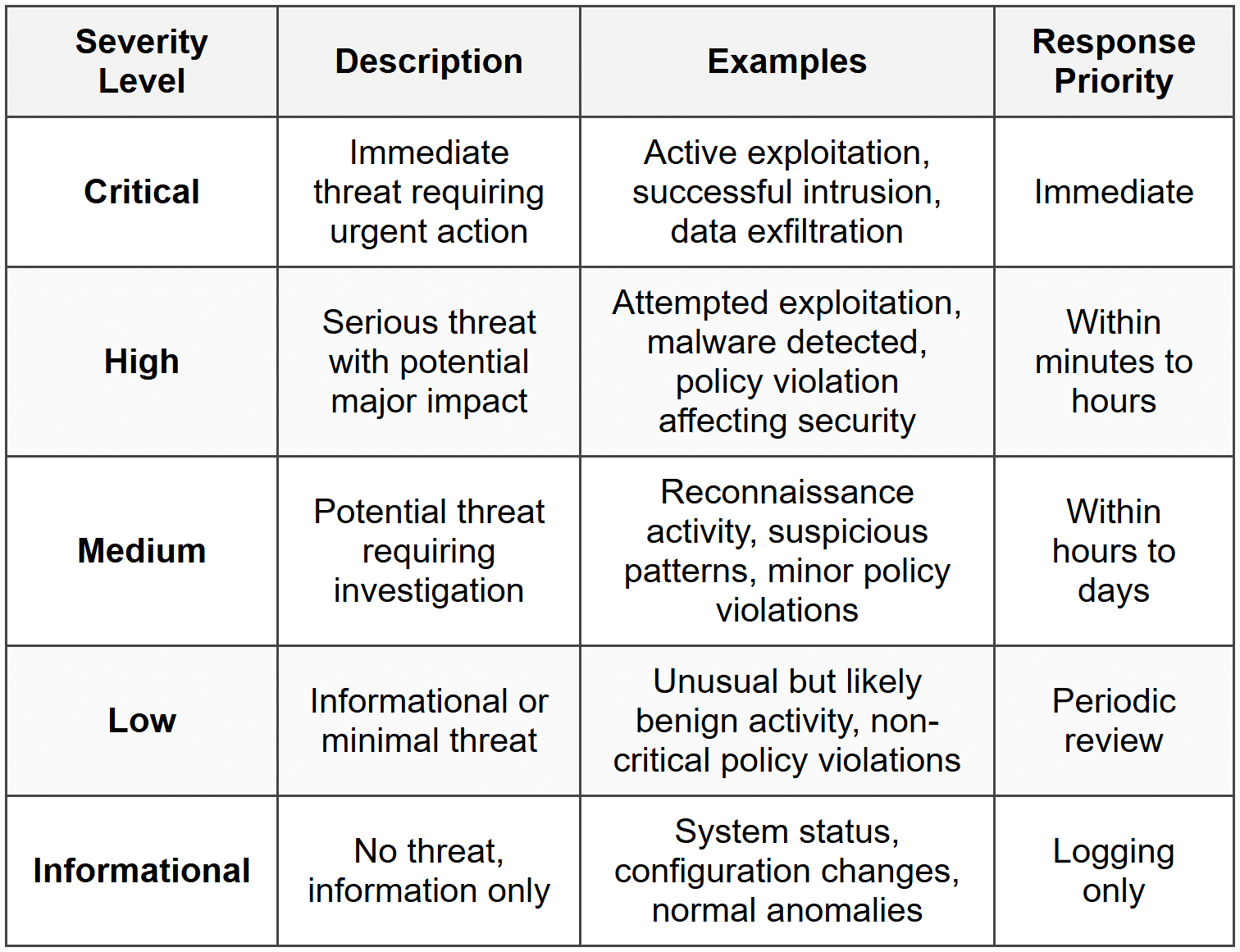
Alert Types and Severity Levels
When IDS/IPS detects suspicious activity, it generates alerts classified by type and severity:
Alert Classifications
True Positive
A true positive is an alert generated for actual malicious activity. This is the desired outcome-the system correctly identified a real threat.
False Positive
A false positive is an alert generated for legitimate activity that the system mistakenly identified as malicious. False positives are problematic because they:
- Waste administrator time investigating non-threats
- Can lead to alert fatigue (ignoring alerts)
- May cause blocking of legitimate traffic (in IPS)
- Reduce confidence in the system
True Negative
A true negative occurs when the system correctly allows legitimate traffic without generating an alert. This represents normal operation.
False Negative
A false negative occurs when the system fails to detect actual malicious activity. This is the most dangerous outcome because attacks go undetected.
Important: Tuning an IDS/IPS involves finding the right balance between false positives and false negatives. More sensitive settings catch more attacks but generate more false positives. Less sensitive settings reduce false positives but may miss some attacks.
Severity Levels
Alerts are typically classified by severity to help prioritize response:
IDS and IPS Performance Considerations
Throughput and Latency
Throughput refers to the amount of traffic the IDS/IPS can process, typically measured in gigabits per second (Gbps) or packets per second (pps). The system must be able to handle peak network loads without dropping packets.
Latency is the delay introduced by the IDS/IPS when processing traffic. For IPS systems operating inline, latency is critical:
- Typical IPS latency: 10-100 microseconds
- High latency can impact application performance
- Must remain below threshold for real-time applications
Resource Requirements
IDS/IPS systems require significant computational resources:
- CPU: For packet processing and analysis
- Memory: For holding packets during inspection and maintaining state tables
- Storage: For logs, alerts, and packet captures
- Network interfaces: High-speed interfaces matching network speed
Scalability
As networks grow, IDS/IPS systems must scale:
- Handle increasing traffic volumes
- Manage growing signature databases
- Process larger numbers of concurrent connections
- Store expanding volumes of logs and alerts
Scaling strategies:
- Distributed sensors with centralized management
- Load balancing across multiple devices
- Hierarchical deployment with different devices at different network layers
- Cloud-based or virtualized IDS/IPS instances
Tuning and Optimization
Effective IDS/IPS deployment requires ongoing tuning to maintain accuracy and minimize false positives:
Baseline Establishment
Before tuning, establish what "normal" looks like in your network:
- Monitor network traffic patterns during typical operations
- Document legitimate applications and services
- Identify expected traffic flows between systems
- Note regular maintenance and backup activities
- Record business processes that generate network traffic
Rule Tuning
Adjust detection rules to fit your environment:
- Disable irrelevant rules: Turn off signatures for vulnerabilities not present in your environment
- Adjust thresholds: Modify triggers for anomaly detection based on your baseline
- Create exceptions: Whitelist known legitimate activities that trigger false positives
- Customize rules: Modify existing rules or create new ones for your specific environment
- Set appropriate severity levels: Adjust alert priorities based on your risk assessment
Regular Maintenance
- Keep signature databases updated
- Review and adjust rules periodically
- Monitor system performance and resource utilization
- Review logs and alerts to identify patterns
- Update baseline as network changes
- Test IDS/IPS effectiveness with simulated attacks
Alert Management
Effective alert management prevents alert fatigue:
- Implement alert aggregation to group related alerts
- Use correlation to identify attack patterns across multiple alerts
- Configure alerting thresholds to reduce noise
- Route alerts to appropriate personnel based on severity
- Integrate with Security Information and Event Management (SIEM) systems
- Establish clear response procedures for different alert types
Evasion Techniques and Countermeasures
Attackers use various techniques to evade detection by IDS/IPS systems. Understanding these helps in configuring systems to counter them:
Common Evasion Techniques
1. Fragmentation
Attackers split malicious payloads across multiple packets to avoid signature matching:
- IP fragmentation: Breaking packets into smaller fragments
- TCP segmentation: Sending data in very small segments
- Countermeasure: Enable stateful inspection and packet reassembly
2. Obfuscation
Disguising attack patterns to avoid signature detection:
- Encoding payloads (Base64, Unicode, hexadecimal)
- Encryption of malicious traffic
- Polymorphic code that changes appearance
- Countermeasure: Use protocol analyzers that decode common encodings; implement SSL/TLS inspection
3. Timing Attacks
Spreading attacks over time to avoid rate-based detection:
- Slow port scans over hours or days
- Low-and-slow attacks that stay under thresholds
- Countermeasure: Implement long-term behavioral analysis and correlation
4. Protocol Manipulation
Exploiting protocol implementations or using unusual protocol features:
- Invalid TCP flags or options
- Overlapping TCP segments
- Malformed packets
- Countermeasure: Enable protocol anomaly detection and normalization
5. Encryption and Tunneling
Hiding malicious traffic inside encrypted or legitimate protocols:
- Using HTTPS to hide attacks
- Tunneling through allowed protocols (DNS, ICMP)
- VPN or SSH tunnels
- Countermeasure: Implement SSL/TLS inspection; monitor for unusual tunneling patterns
6. Resource Exhaustion
Overwhelming the IDS/IPS to prevent proper inspection:
- Flooding with traffic to exceed processing capacity
- Generating massive numbers of alerts to hide real attacks
- Countermeasure: Deploy adequately resourced systems; implement rate limiting and traffic prioritization
Integration with Security Infrastructure
IDS and IPS are most effective when integrated with other security technologies:
Integration with Firewalls
IDS/IPS and firewalls complement each other:
- Firewalls: Block traffic based on source/destination addresses, ports, and basic protocol information
- IDS/IPS: Perform deep packet inspection and behavioral analysis
- Integration: IPS can automatically update firewall rules to block detected threats
SIEM Integration
Security Information and Event Management (SIEM) systems collect and analyze security events from multiple sources:
- IDS/IPS sends alerts and logs to SIEM
- SIEM correlates IDS/IPS alerts with events from firewalls, servers, applications, etc.
- Provides comprehensive view of security posture
- Enables advanced threat detection through correlation
- Centralizes reporting and compliance monitoring
Threat Intelligence Integration
Modern IDS/IPS can leverage external threat intelligence:
- Feeds of known malicious IP addresses and domains
- Indicators of Compromise (IoCs) from security organizations
- Information about emerging threats and zero-day vulnerabilities
- Reputation services for IPs, URLs, and file hashes
Endpoint Security Integration
Combining network-based IDS/IPS with host-based security:
- Network IDS/IPS monitors traffic between endpoints
- Endpoint protection monitors activities on individual systems
- Coordinated response when threats are detected
- Comprehensive coverage of network and host layers
Best Practices for IDS and IPS Deployment
Follow these best practices to maximize the effectiveness of your IDS/IPS implementation:
Planning and Design
- Define objectives: Clearly identify what you want to protect and against what threats
- Conduct risk assessment: Understand your network's vulnerabilities and threat landscape
- Choose appropriate type: Select IDS vs. IPS and network-based vs. host-based based on requirements
- Plan sensor placement: Position sensors at strategic network points for optimal coverage
- Ensure adequate resources: Size systems to handle peak traffic loads with headroom for growth
Implementation
- Start in monitoring mode: Deploy IPS in IDS mode initially to understand behavior before enabling blocking
- Establish baseline: Allow time to learn normal network behavior before aggressive tuning
- Implement gradually: Roll out in phases, starting with critical segments
- Configure high availability: Implement redundancy to prevent single points of failure
- Enable bypass mechanisms: Ensure IPS can fail-open if necessary to prevent network outages
Operation and Maintenance
- Keep signatures updated: Regularly update signature databases
- Monitor performance: Track resource utilization and processing latency
- Review alerts daily: Investigate alerts promptly and adjust rules based on findings
- Tune continuously: Ongoing refinement to reduce false positives without missing attacks
- Test regularly: Conduct penetration testing to verify effectiveness
- Document everything: Maintain documentation of configurations, tuning decisions, and incident responses
- Train staff: Ensure personnel understand how to use and maintain the system
Security Considerations
- Secure the IDS/IPS: Protect management interfaces and ensure only authorized access
- Encrypt management traffic: Use secure protocols for remote management
- Monitor the monitors: Log and audit access to IDS/IPS systems
- Implement change control: Track and approve configuration changes
- Backup configurations: Regularly backup system configurations and rules
Limitations of IDS and IPS
While powerful, IDS and IPS have limitations that must be understood:
Technical Limitations
- Encrypted traffic: Cannot inspect encrypted payloads without SSL/TLS decryption (which has privacy and performance implications)
- High-speed networks: May struggle to inspect all traffic at very high speeds (10 Gbps+) without specialized hardware
- Zero-day exploits: Signature-based detection cannot identify completely new attacks
- False positives/negatives: No system is perfectly accurate; tuning is always a compromise
- Resource constraints: Limited by available CPU, memory, and storage
Operational Limitations
- Requires expertise: Effective deployment and tuning requires skilled security personnel
- Maintenance overhead: Ongoing effort required for updates, tuning, and alert management
- Alert fatigue: High volumes of alerts can overwhelm analysts
- Configuration complexity: Complex rule sets difficult to manage and maintain
- Limited context: Network-based systems may lack context about applications and users
Strategic Limitations
- Not a complete solution: Must be part of layered security approach
- Cannot prevent all attacks: Determined attackers may find ways to evade detection
- Reactive nature: Even IPS reacts to attacks rather than preventing vulnerabilities
- Insider threats: Limited effectiveness against authorized users misusing access
- Physical security: Cannot protect against physical access to systems
Remember: IDS and IPS are essential components of network security, but they should never be the only layer of defense. Defense-in-depth requires multiple complementary security measures working together.
Future Trends in IDS and IPS
IDS and IPS technology continues to evolve to address emerging threats and network changes:
Machine Learning and AI
Artificial intelligence and machine learning are being integrated into IDS/IPS:
- Better anomaly detection through learning algorithms
- Automatic rule generation based on observed patterns
- Improved accuracy in distinguishing attacks from legitimate activity
- Adaptive systems that evolve with changing threat landscapes
- Predictive capabilities to anticipate attacks before they occur
Cloud-Based IDS/IPS
As organizations move to cloud infrastructure:
- Virtual IDS/IPS appliances for cloud environments
- Native cloud service provider security services
- Hybrid approaches protecting both on-premises and cloud assets
- Scalable inspection capabilities matching cloud elasticity
Encrypted Traffic Analysis
With increasing encryption, new approaches are needed:
- Analyzing encrypted traffic without decryption using metadata and behavioral patterns
- Improved SSL/TLS inspection with better performance
- Detection based on certificate analysis and TLS handshake patterns
IoT and OT Security
Specialized IDS/IPS for Internet of Things and Operational Technology:
- Understanding IoT-specific protocols and traffic patterns
- Protecting industrial control systems and SCADA networks
- Anomaly detection tailored to deterministic OT environments
Threat Intelligence Integration
Deeper integration with global threat intelligence:
- Real-time updates of emerging threats
- Automated response based on threat intelligence feeds
- Sharing of threat information between organizations
- Context-aware detection using external reputation data
Review Questions
- What is the fundamental difference between an IDS and an IPS in terms of how they respond to detected threats?
- Explain the difference between network-based IDS/IPS (NIDS/NIPS) and host-based IDS/IPS (HIDS/HIPS). What does each monitor?
- Describe how signature-based detection works. What are its main advantages and limitations?
- What is anomaly-based detection and how does it differ from signature-based detection? Why might it generate more false positives?
- What is the difference between a true positive and a false positive alert? Why are false positives problematic?
- Explain the concept of inline deployment versus out-of-band deployment. Which type of deployment is used by IPS systems and why?
- What is a network TAP and how does it differ from a SPAN port for traffic acquisition?
- List at least four types of attacks that IDS and IPS systems are designed to detect.
- What is "alert fatigue" and how can it impact the effectiveness of an IDS deployment?
- Why is tuning important for IDS/IPS systems? What might happen if a newly deployed IPS is not properly tuned before being placed in blocking mode?
- Describe three evasion techniques attackers might use to avoid detection by IDS/IPS systems.
- How do IDS/IPS systems integrate with SIEM systems, and what benefits does this integration provide?
- What is the purpose of establishing a baseline when deploying an anomaly-based IDS?
- What are some limitations of IDS/IPS systems when dealing with encrypted network traffic?
- Explain why IDS and IPS should be considered part of a layered security approach rather than standalone solutions.
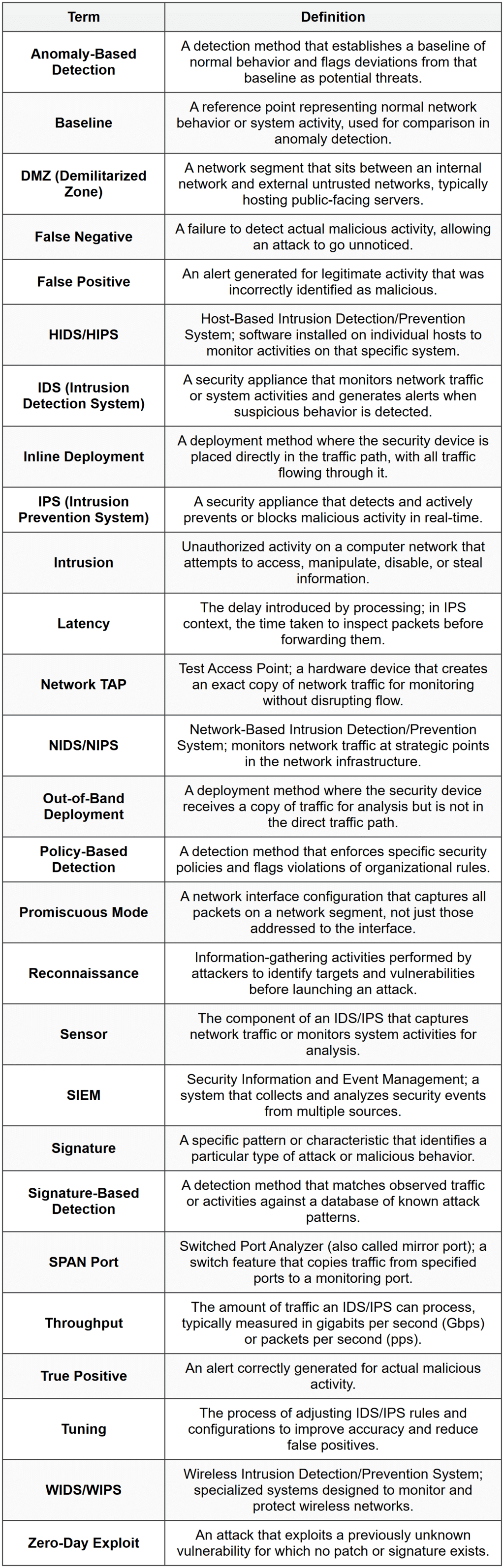
Glossary