Zero Trust Architecture
Zero Trust Architecture
Zero Trust Architecture is a modern approach to network security that fundamentally changes how organizations protect their digital resources. Unlike traditional security models that assume everything inside a network perimeter can be trusted, Zero Trust operates on a simple principle: never trust, always verify. This means that no user, device, or network traffic is automatically trusted, regardless of whether it originates inside or outside the organization's network. In this comprehensive guide, you will learn what Zero Trust Architecture is, why it matters, how it works, and how to implement it as part of network hardening strategies.
The Problem with Traditional Network Security
To understand why Zero Trust Architecture emerged, we first need to understand the limitations of traditional security approaches.
The Castle-and-Moat Model
Traditional network security follows what experts call the castle-and-moat model or perimeter-based security.
Imagine a medieval castle surrounded by a moat filled with water. The moat keeps enemies out, but once someone crosses the drawbridge and enters the castle, they can move freely inside. Traditional network security works the same way: strong defenses at the network boundary (firewall, VPN), but once you're inside, you're trusted.
In this model:
- Everything outside the network perimeter is considered dangerous and untrusted
- Everything inside the network perimeter is considered safe and trusted
- Security focuses on defending the boundary between inside and outside
- Once authenticated, users typically have broad access to internal resources
Why the Traditional Model Fails Today
The castle-and-moat approach worked reasonably well when networks were simple and contained, but modern computing has changed dramatically:
- Network perimeters have dissolved: Employees work from home, coffee shops, and airports. Applications run in the cloud rather than on-premises. The clear boundary between "inside" and "outside" no longer exists.
- Insider threats are real: Studies show that 30-40% of security breaches involve insiders-employees, contractors, or partners who already have legitimate access.
- Lateral movement attacks: Once attackers breach the perimeter (through phishing, compromised credentials, or other means), they can move freely inside the network, accessing sensitive systems because internal traffic is trusted by default.
- Mobile and IoT devices: Organizations now support thousands of devices-smartphones, tablets, sensors, and smart devices-that don't sit behind a traditional network perimeter.
- Cloud adoption: Data and applications now reside across multiple cloud providers, not just in a corporate data center.
Real-world example: In many high-profile data breaches, attackers gained initial access through a single compromised credential or phishing email. Once inside the network, they spent weeks or months moving laterally, accessing databases, and extracting data-all because the internal network trusted them.
What is Zero Trust Architecture?
Zero Trust Architecture (ZTA) is a security framework that eliminates the concept of trust based on network location. Instead of assuming that anything inside the network is safe, Zero Trust requires continuous verification of every user, device, and transaction.
Core Principle
The foundational principle of Zero Trust is:
"Never trust, always verify"
This means:
- No user or device is trusted by default, regardless of location
- Every access request must be authenticated and authorized
- Access is granted on a least-privilege basis-users get only the minimum access they need
- Verification happens continuously, not just at initial login
Key Concepts
Zero Trust Architecture is built on several fundamental concepts:
1. Assume Breach
Zero Trust operates under the assumption that breach is inevitable or has already occurred. Rather than trying to build an impenetrable wall, Zero Trust focuses on limiting damage when (not if) attackers gain some level of access.
2. Explicit Verification
Every access request must be explicitly verified using all available data points:
- User identity (who is requesting access?)
- Device health (is the device secure and compliant?)
- Location (where is the request coming from?)
- Time (is this request happening at a normal time?)
- Behavior patterns (is this typical behavior for this user?)
3. Least Privilege Access
Least privilege means granting users the minimum level of access required to perform their job-nothing more. Instead of giving employees broad access to entire network segments, Zero Trust provides granular access to specific resources only when needed.
4. Micro-segmentation
Micro-segmentation divides the network into small, isolated zones. Each zone contains specific resources, and movement between zones requires authentication and authorization. This prevents lateral movement-if attackers compromise one part of the network, they cannot easily access other parts.
Think of micro-segmentation like compartments in a submarine. If one compartment floods, watertight doors prevent water from spreading to other compartments. Similarly, if one network segment is compromised, micro-segmentation prevents attackers from moving to other segments.
The Three Pillars of Zero Trust
Zero Trust Architecture rests on three fundamental pillars that work together to create comprehensive security:
1. Identity Verification
Identity is the new security perimeter in Zero Trust. Every user and service must be strongly authenticated before accessing any resource.
Components of identity verification:
- Multi-Factor Authentication (MFA): Requires users to provide multiple forms of proof (password + fingerprint, password + SMS code, etc.)
- Single Sign-On (SSO): Centralized authentication that allows users to access multiple applications with one set of credentials while maintaining strong verification
- Identity and Access Management (IAM): Systems that manage user identities, roles, and permissions centrally
- Continuous authentication: Ongoing verification throughout a session, not just at login
2. Device Trust
In Zero Trust, devices (laptops, smartphones, servers, IoT devices) must be verified and authorized just like users.
Device trust involves:
- Device registration: Only known, registered devices can access resources
- Security posture assessment: Checking if devices have current security patches, antivirus software, encryption, and proper configuration
- Health monitoring: Continuous monitoring to ensure devices remain compliant
- Device certificates: Cryptographic certificates that uniquely identify and authenticate devices
Example: A user tries to access company email from a personal laptop that hasn't been registered with the company and lacks required security software. Zero Trust would deny or restrict access, even if the user's password is correct.
3. Network and Application Security
The network infrastructure itself must be designed to support Zero Trust principles.
Key elements include:
- Encryption: All network traffic is encrypted, both in transit and at rest
- Micro-segmentation: Network divided into small, isolated zones with strict access controls between them
- Software-Defined Perimeter (SDP): Creates individual, dynamic perimeters around each resource rather than one perimeter around the entire network
- API security: Protecting application programming interfaces with authentication and monitoring
Zero Trust Architecture Components
A complete Zero Trust Architecture consists of several integrated components working together. Understanding each component helps you see how the full system operates.
Policy Engine and Policy Administrator
The Policy Engine (PE) is the brain of Zero Trust Architecture. It makes access decisions based on organizational policies and real-time information.
How it works:
- A user or device requests access to a resource
- The Policy Engine evaluates the request against multiple factors:
- User identity and authentication level
- Device security posture
- Resource sensitivity
- Environmental factors (location, time, threat level)
- Historical behavior patterns
- The Policy Engine makes a decision: grant, deny, or grant with conditions
- The Policy Administrator (PA) executes the decision, configuring access controls accordingly
Policy Enforcement Point
The Policy Enforcement Point (PEP) sits in the communication path and enforces the decisions made by the Policy Engine and Policy Administrator.
Functions of PEP:
- Intercepts access requests
- Communicates with the Policy Engine to obtain authorization decisions
- Enables or blocks connections based on policy decisions
- Monitors ongoing sessions to ensure continuous compliance
Think of the Policy Enforcement Point as a security checkpoint at an airport. It checks your credentials (passport, boarding pass), verifies you're allowed to pass, and monitors your behavior while you're in the secure area.
Identity Provider
The Identity Provider (IdP) is a trusted system that creates, maintains, and manages identity information for users and services.
Responsibilities:
- Authenticating users when they log in
- Storing user credentials securely
- Providing identity assertions to applications
- Managing user attributes and group memberships
- Supporting authentication protocols like SAML, OAuth, and OpenID Connect
Examples: Microsoft Azure Active Directory, Okta, Google Identity Platform, Ping Identity
Data Security
Zero Trust extends beyond network and identity security to protect data itself, regardless of where it resides or travels.
Data security measures:
- Data classification: Categorizing data by sensitivity (public, internal, confidential, restricted)
- Encryption: Protecting data with cryptographic algorithms both in storage and during transmission
- Data Loss Prevention (DLP): Tools that prevent sensitive data from leaving the organization inappropriately
- Rights management: Controlling who can view, edit, copy, or share specific data
Visibility and Analytics
Zero Trust requires comprehensive visibility into all network activity and continuous analysis of security telemetry.
Key capabilities:
- Logging: Recording all access requests, decisions, and activities
- Security Information and Event Management (SIEM): Collecting and analyzing security logs from across the environment
- User and Entity Behavior Analytics (UEBA): Using machine learning to detect anomalous behavior
- Threat intelligence: Incorporating external information about current threats and attack patterns
How Zero Trust Works: A Complete Example
Let's walk through a detailed example to see how all the Zero Trust components work together in a real scenario.
Scenario: Employee Accessing a Customer Database
Context: Sarah, a sales manager, needs to access the customer relationship management (CRM) database from her laptop while working from a coffee shop.
Step-by-Step Process
Step 1: Access Request
Sarah opens her web browser and navigates to the CRM application. The request reaches the Policy Enforcement Point (PEP) before touching the actual application.
Step 2: Initial Authentication
The PEP redirects Sarah to the Identity Provider for authentication. Sarah enters her username and password, then provides a second factor (a code from her authentication app on her phone). The Identity Provider validates both factors.
Step 3: Device Assessment
While Sarah authenticates, the Zero Trust system checks her device:
- Is this device registered in the corporate inventory?
- Does it have the latest operating system patches?
- Is antivirus software installed and up-to-date?
- Is the hard drive encrypted?
- Are there any signs of malware or compromise?
Step 4: Context Analysis
The Policy Engine gathers contextual information:
- User context: Sarah is a sales manager with legitimate need for CRM access
- Location: Connection originates from an IP address associated with a public Wi-Fi network (higher risk)
- Time: Request occurs during normal business hours (lower risk)
- Behavioral analysis: Sarah typically accesses the CRM daily, so this request matches historical patterns (lower risk)
- Resource sensitivity: CRM contains sensitive customer data (requires strong protection)
Step 5: Policy Decision
The Policy Engine evaluates the request against organizational policies. In this case, it decides to grant access with conditions:
- Sarah can view customer records
- Sarah can edit records she owns
- Sarah cannot export or download bulk data (because she's on an untrusted network)
- Session will expire after 1 hour of inactivity (more restrictive than the normal 4-hour timeout from trusted locations)
- All data transmission must be encrypted
Step 6: Access Granted with Monitoring
The Policy Administrator configures the access controls according to the Policy Engine's decision. The PEP establishes an encrypted connection between Sarah's device and the CRM application. Sarah can now work.
Step 7: Continuous Verification
While Sarah works, Zero Trust continues monitoring:
- Is her device still compliant?
- Is her behavior normal, or is she accessing unusually large numbers of records?
- Has the threat level changed (new vulnerabilities discovered, attacks detected)?
- Is the session still valid, or has it exceeded time limits?
If any conditions change-for example, if Sarah's device suddenly shows signs of malware infection-the system can immediately revoke access or increase restrictions.
Contrast with traditional security: In a perimeter-based model, once Sarah authenticated to the corporate VPN, she would typically have broad access to the entire internal network, including systems she doesn't need. Her access level would be the same whether she was in a secure office or on public Wi-Fi. The system would not continuously monitor her session or adapt to changing conditions.
Zero Trust Network Architecture Patterns
Organizations implement Zero Trust using several different architectural patterns. Understanding these patterns helps in designing and deploying Zero Trust solutions.
Pattern 1: Software-Defined Perimeter (SDP)
Software-Defined Perimeter creates individualized, dynamically provisioned network perimeters for each user or device.
How it works:
- Network infrastructure is "dark" by default-invisible and unreachable
- Users and devices authenticate to an SDP controller
- After successful authentication and authorization, the controller creates a custom, encrypted network connection between the user's device and specific authorized resources
- All other network resources remain invisible to the user
Imagine a building where every room is invisible until you're specifically granted access. When you're authorized to enter a particular room, a doorway appears just for you, and you can see and enter only that room. Other rooms remain invisible and inaccessible.
Benefits:
- Greatly reduces attack surface-attackers cannot see or probe resources they're not authorized to access
- Prevents network reconnaissance and scanning
- Provides granular access control
Pattern 2: Identity-Aware Proxy
An Identity-Aware Proxy sits between users and applications, making access decisions based on user identity and context rather than network location.
How it works:
- All application requests go through the proxy
- The proxy authenticates the user and evaluates their authorization
- The proxy inspects the request context (device health, location, etc.)
- If authorized, the proxy forwards the request to the backend application
- The backend application trusts the proxy's authentication decision
Benefits:
- Centralizes authentication and authorization logic
- Works with existing applications without modification
- Provides consistent access control across all applications
- Enables context-aware access decisions
Example implementations: Google BeyondCorp, Cloudflare Access, Zscaler Private Access
Pattern 3: Micro-Segmentation with Next-Generation Firewalls
This pattern divides the network into small segments with strict firewall rules between segments, often enforced at the host level.
How it works:
- Network is divided into numerous small zones (micro-segments)
- Each segment contains related resources (e.g., one application tier, one set of databases)
- Firewall rules between segments follow least-privilege principles
- Rules are based on workload identity and application requirements, not just IP addresses
- Host-based firewalls provide additional control at each endpoint
Benefits:
- Prevents lateral movement-attackers cannot easily spread from one segment to another
- Limits blast radius of security incidents
- Provides defense in depth
Pattern 4: Service Mesh for Microservices
In modern cloud-native environments with microservices, a service mesh provides Zero Trust communication between services.
How it works:
- Each microservice has an associated proxy (called a "sidecar")
- All communication between services goes through these proxies
- Proxies authenticate services using cryptographic certificates
- Proxies encrypt all traffic between services (mutual TLS)
- The service mesh control plane manages policies, certificates, and traffic rules
Benefits:
- Strong service-to-service authentication
- Automatic encryption of all inter-service communication
- Fine-grained authorization policies
- Visibility into all service communications
Example implementations: Istio, Linkerd, Consul Connect
Implementing Zero Trust: A Practical Approach
Transitioning to Zero Trust Architecture is a journey, not a single project. Organizations should approach implementation systematically.
Phase 1: Assessment and Planning
1. Identify Protect Surfaces
Rather than trying to protect everything at once, identify your protect surfaces-the most critical data, applications, assets, and services (DAAS) that must be secured.
Questions to ask:
- What are our most valuable data assets?
- Which applications are business-critical?
- What services are essential for operations?
- Where does sensitive data reside?
2. Map Transaction Flows
For each protect surface, document how data flows:
- Who needs access?
- From where do they access it?
- Using what applications and protocols?
- What data moves where?
- What services communicate with each other?
3. Assess Current State
Evaluate your current security posture:
- What authentication mechanisms are in place?
- How is access currently controlled?
- What visibility exists into network traffic?
- What security tools are already deployed?
- Where are the gaps?
Phase 2: Foundation Building
1. Establish Strong Identity Management
Identity is foundational to Zero Trust. Implement:
- Centralized identity provider
- Multi-factor authentication for all users
- Single sign-on where appropriate
- Regular review and cleanup of user accounts
- Role-based access control (RBAC) definitions
2. Gain Visibility
You cannot protect what you cannot see. Implement:
- Comprehensive logging of authentication events
- Network traffic monitoring
- Endpoint detection and response (EDR) tools
- Security information and event management (SIEM) system
- Asset inventory and management
3. Implement Device Management
Establish control over devices accessing resources:
- Device registration and inventory
- Mobile device management (MDM) or unified endpoint management (UEM)
- Device compliance policies
- Automated patch management
Phase 3: Zero Trust Deployment
1. Start with a Pilot
Select one protect surface for initial Zero Trust implementation. Criteria for selection:
- High value or sensitivity
- Well-understood access requirements
- Limited scope for easier management
- Manageable impact if something goes wrong
2. Implement Micro-Segmentation
Isolate the pilot protect surface:
- Define network segments
- Implement firewall rules based on least privilege
- Use application-layer controls, not just network-layer
- Test thoroughly before enforcement
3. Deploy Policy Enforcement
Implement Zero Trust access controls:
- Define policies based on user identity, device health, and context
- Deploy policy enforcement points
- Start in monitoring mode to observe behavior
- Gradually move to enforcement mode
4. Enable Continuous Monitoring
Implement ongoing verification:
- Monitor user behavior for anomalies
- Continuously assess device compliance
- Analyze access patterns
- Integrate threat intelligence
- Set up alerts for suspicious activity
Phase 4: Expansion and Optimization
1. Expand to Additional Protect Surfaces
After successful pilot, extend Zero Trust to additional resources:
- Prioritize based on risk and business value
- Apply lessons learned from the pilot
- Scale infrastructure and tools
- Maintain consistent policies
2. Optimize and Mature
Continuously improve the Zero Trust implementation:
- Refine policies based on actual usage patterns
- Automate more decision-making
- Improve response times and user experience
- Enhance analytics and machine learning capabilities
- Conduct regular audits and assessments
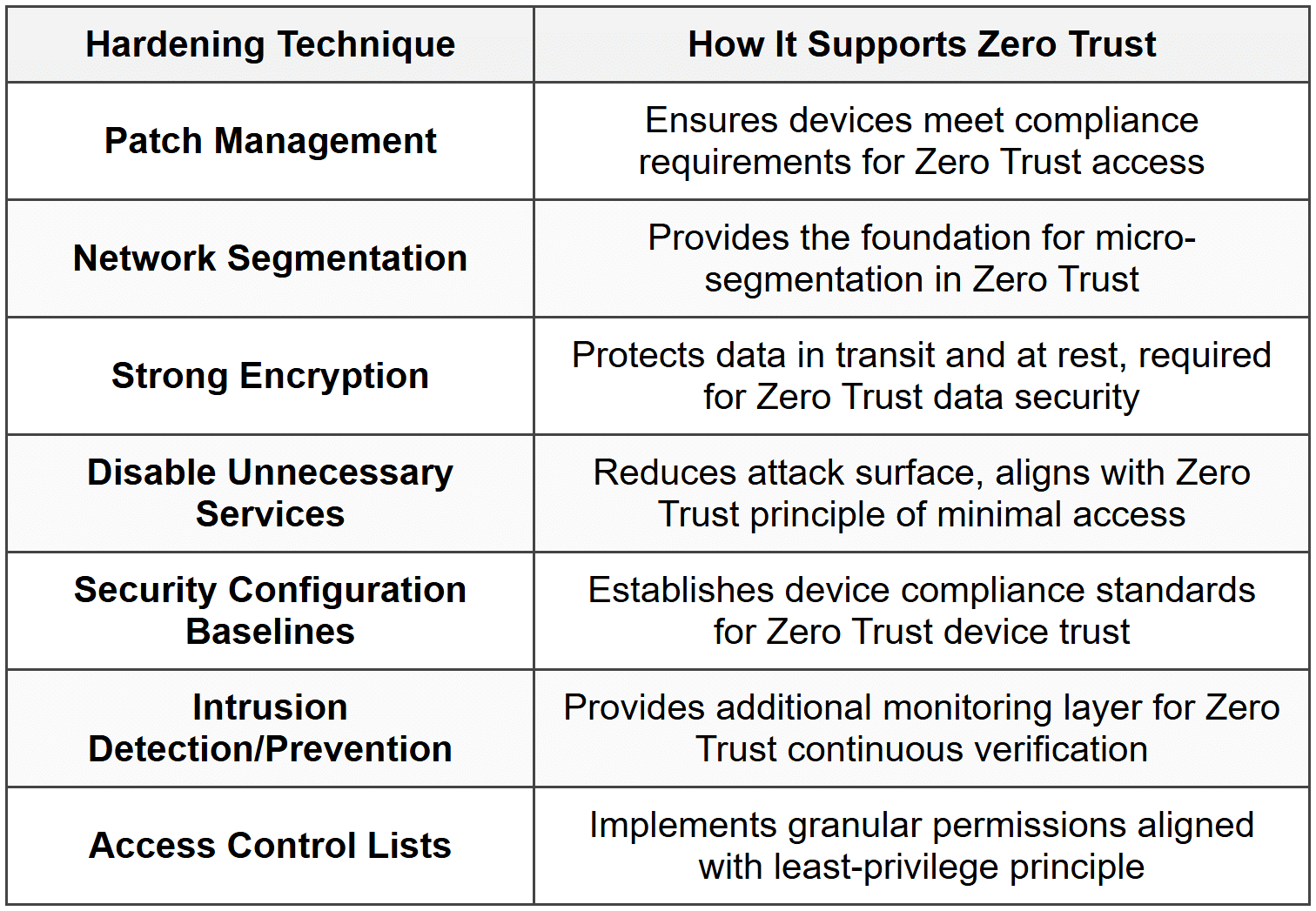
Zero Trust and Network Hardening
Zero Trust Architecture is a crucial component of comprehensive network hardening-the process of securing a network by reducing its vulnerability surface and implementing defense-in-depth strategies.
How Zero Trust Enhances Network Hardening
1. Reduces Attack Surface
Zero Trust makes resources invisible to unauthorized users, dramatically reducing the attack surface. Attackers cannot exploit what they cannot see or reach.
2. Limits Lateral Movement
Micro-segmentation and least-privilege access prevent attackers from moving freely through the network after initial compromise. Each movement requires re-authentication and authorization.
3. Provides Defense in Depth
Zero Trust adds multiple layers of security:
- Identity verification
- Device trust
- Network segmentation
- Application-level controls
- Data protection
- Continuous monitoring
If one layer fails, others continue providing protection.
4. Improves Detection and Response
Comprehensive logging and continuous monitoring enable faster detection of anomalies and security incidents. Granular controls allow precise, surgical responses to incidents.
Complementary Hardening Techniques
Zero Trust works best when combined with other network hardening practices:
Challenges and Considerations
While Zero Trust provides significant security benefits, organizations face several challenges during implementation.
Technical Challenges
1. Complexity
Zero Trust architectures are inherently complex, involving many integrated components. This complexity can:
- Increase initial deployment difficulty
- Require specialized skills
- Create potential for misconfiguration
- Complicate troubleshooting
Mitigation: Start small with pilot projects, invest in training, use automation where possible, and work with experienced vendors or consultants.
2. Legacy Systems
Older applications and systems may not support modern authentication protocols or integration with Zero Trust components.
Mitigation: Use proxy-based solutions to add Zero Trust controls without modifying legacy applications, plan for gradual modernization, or isolate legacy systems with compensating controls.
3. Performance Impact
Additional authentication, authorization, and encryption can introduce latency and reduce performance.
Mitigation: Deploy high-performance infrastructure, optimize policies, use caching where appropriate, and balance security with user experience.
4. Network Visibility Gaps
Zero Trust requires comprehensive visibility, but organizations often have blind spots in their networks.
Mitigation: Invest in monitoring and logging tools, implement network traffic analysis, deploy endpoint detection and response (EDR) solutions.
Organizational Challenges
1. Cultural Resistance
Users and IT staff may resist changes to familiar workflows and processes.
Mitigation: Communicate benefits clearly, involve stakeholders early, provide training, implement changes gradually, and minimize user friction where possible.
2. Cost and Resources
Zero Trust implementation requires investment in technology, people, and time.
Mitigation: Develop clear business case showing risk reduction and potential cost savings from preventing breaches, phase implementation to spread costs, leverage existing tools where possible.
3. Operational Changes
Zero Trust requires new operational processes, incident response procedures, and maintenance activities.
Mitigation: Document new processes, train operations teams, automate routine tasks, establish clear ownership and responsibilities.
Security Considerations
1. Zero Trust is Not Zero Risk
Zero Trust significantly improves security but does not eliminate all risk. Organizations must maintain realistic expectations.
2. Policy Errors Can Be Severe
Misconfigured policies in Zero Trust can either block legitimate access (availability impact) or inadvertently grant excessive access (security impact).
Mitigation: Test policies thoroughly before enforcement, implement change control processes, maintain emergency access procedures, conduct regular audits.
3. Identity System Is Critical
Since Zero Trust relies heavily on identity, the identity system becomes a high-value target. If attackers compromise the identity provider, they can bypass many controls.
Mitigation: Harden identity infrastructure, implement strong authentication for identity administrators, monitor identity systems closely, maintain backup authentication methods.
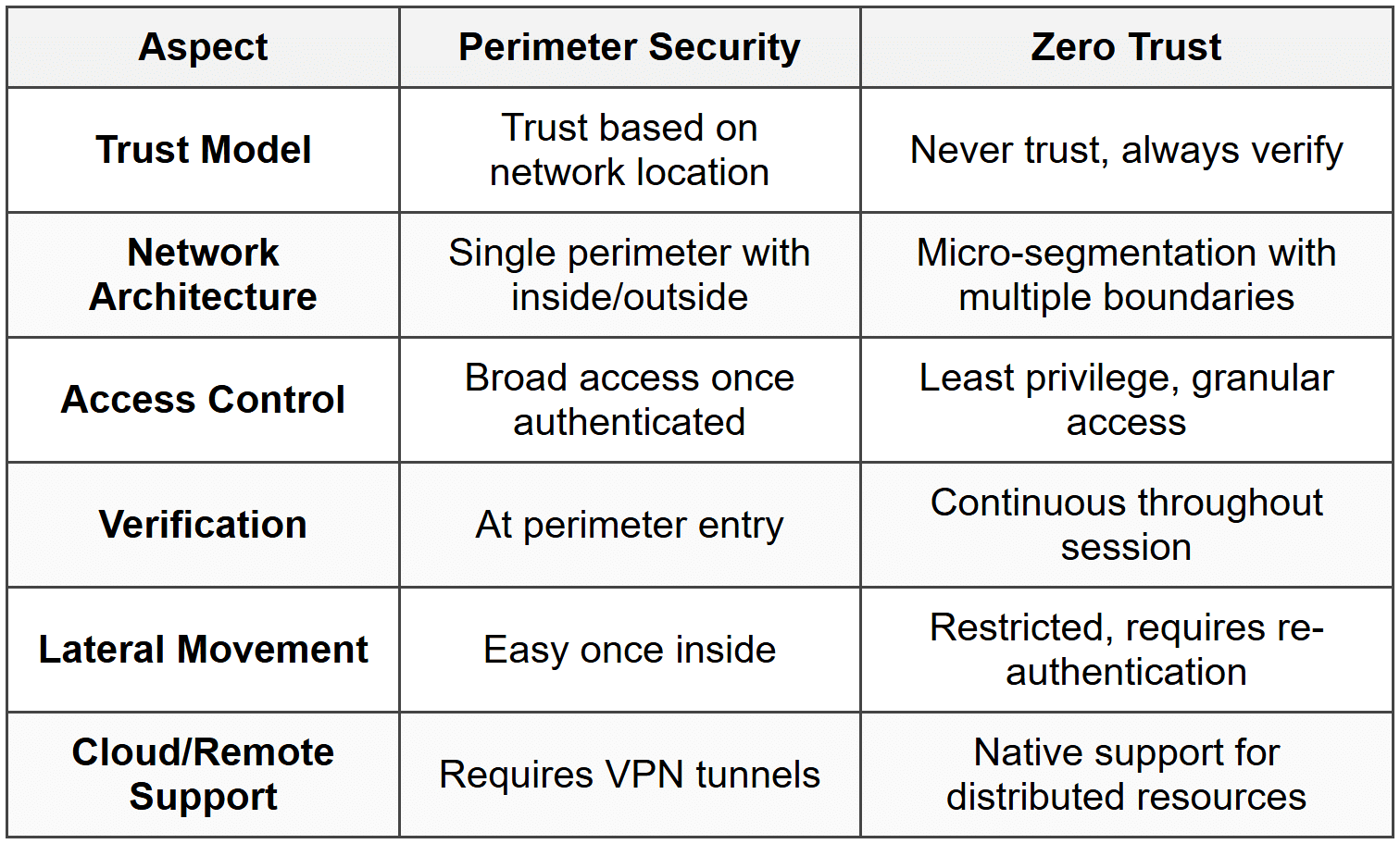
Zero Trust vs. Other Security Models
Understanding how Zero Trust compares to other security approaches helps clarify its unique benefits and appropriate use cases.
Zero Trust vs. Perimeter Security
Zero Trust vs. VPN
Virtual Private Networks (VPNs) have traditionally provided remote access to corporate networks. Zero Trust offers a different approach:
VPN Approach:
- Creates encrypted tunnel to corporate network
- User authenticates once at VPN gateway
- After connection, user typically has network-level access to many resources
- Access based on network location (inside VPN = trusted)
Zero Trust Approach:
- No network-level tunnel required
- User authenticates to each application or resource
- Access is application-specific, not network-wide
- Continuous verification regardless of connection method
Note: Some organizations use VPN as part of a Zero Trust architecture, adding additional authentication and authorization layers on top of the VPN connection.
Zero Trust vs. Defense in Depth
Zero Trust and defense in depth are complementary rather than competing approaches:
Defense in Depth: A security strategy that employs multiple layers of security controls. If one layer fails, others continue to provide protection.
Zero Trust implements defense in depth through:
- Identity verification (first layer)
- Device trust (second layer)
- Network segmentation (third layer)
- Application controls (fourth layer)
- Data protection (fifth layer)
- Monitoring and analytics (detection layer)
Both concepts emphasize multiple overlapping security measures rather than relying on a single security control.
Real-World Applications and Use Cases
Zero Trust Architecture applies to various scenarios and environments. Understanding practical applications helps illustrate its versatility.
Use Case 1: Remote Workforce
Scenario: Organization with thousands of employees working from home, coffee shops, and co-working spaces.
Zero Trust Implementation:
- Employees authenticate using SSO with MFA, regardless of location
- Device health is verified before granting access
- Applications are delivered through identity-aware proxy
- Access policies adapt based on location risk (home network vs. public Wi-Fi)
- No VPN required-applications accessible directly via secure channels
- Continuous monitoring detects anomalous behavior
Benefits: Secure access from anywhere, improved user experience (no VPN connection delays), reduced infrastructure costs, better visibility into access patterns.
Use Case 2: Third-Party Access
Scenario: Organization needs to grant contractors, vendors, and partners access to specific resources without exposing the entire network.
Zero Trust Implementation:
- External users authenticate through dedicated identity provider
- Access limited to specific applications or data sets required for their work
- Time-bound access that automatically expires
- Cannot see or access other network resources
- All activities logged and monitored
- Session recording for compliance purposes
Benefits: Minimal exposure of internal resources, easy to grant and revoke access, clear audit trail, compliance with principle of least privilege.
Use Case 3: Multi-Cloud Environment
Scenario: Organization runs workloads across AWS, Azure, and Google Cloud, plus on-premises data centers.
Zero Trust Implementation:
- Centralized identity management across all environments
- Service mesh for secure service-to-service communication
- Consistent policies applied regardless of where workloads run
- Micro-segmentation within and between cloud environments
- Encrypted communications using mutual TLS
- Unified logging and monitoring across all platforms
Benefits: Consistent security posture, simplified management, visibility across hybrid environment, reduced risk from cloud misconfigurations.
Use Case 4: IoT and OT Networks
Scenario: Manufacturing facility with hundreds of IoT sensors, industrial control systems, and operational technology (OT) devices.
Zero Trust Implementation:
- Device identity and authentication for all IoT/OT devices
- Micro-segmentation isolates devices by function and risk level
- Strict controls on device-to-device communication
- Separate management plane for administrative access
- Continuous monitoring of device behavior
- Automated response to anomalies (e.g., quarantine compromised device)
Benefits: Protection against IoT-based attacks, containment of compromised devices, improved operational visibility, compliance with safety standards.
Use Case 5: Merger and Acquisition Integration
Scenario: Company acquires another business and needs to integrate networks and provide access to shared resources.
Zero Trust Implementation:
- Both companies' users authenticate through federated identity
- Access to shared resources based on role and business need
- Networks remain separate with no direct connectivity
- Zero Trust controls provide secure collaboration without trust between networks
- Easy to segment or separate if integration doesn't proceed
Benefits: Fast, secure integration, flexibility to maintain separation, reduced risk during transition period, clear access controls and audit trails.
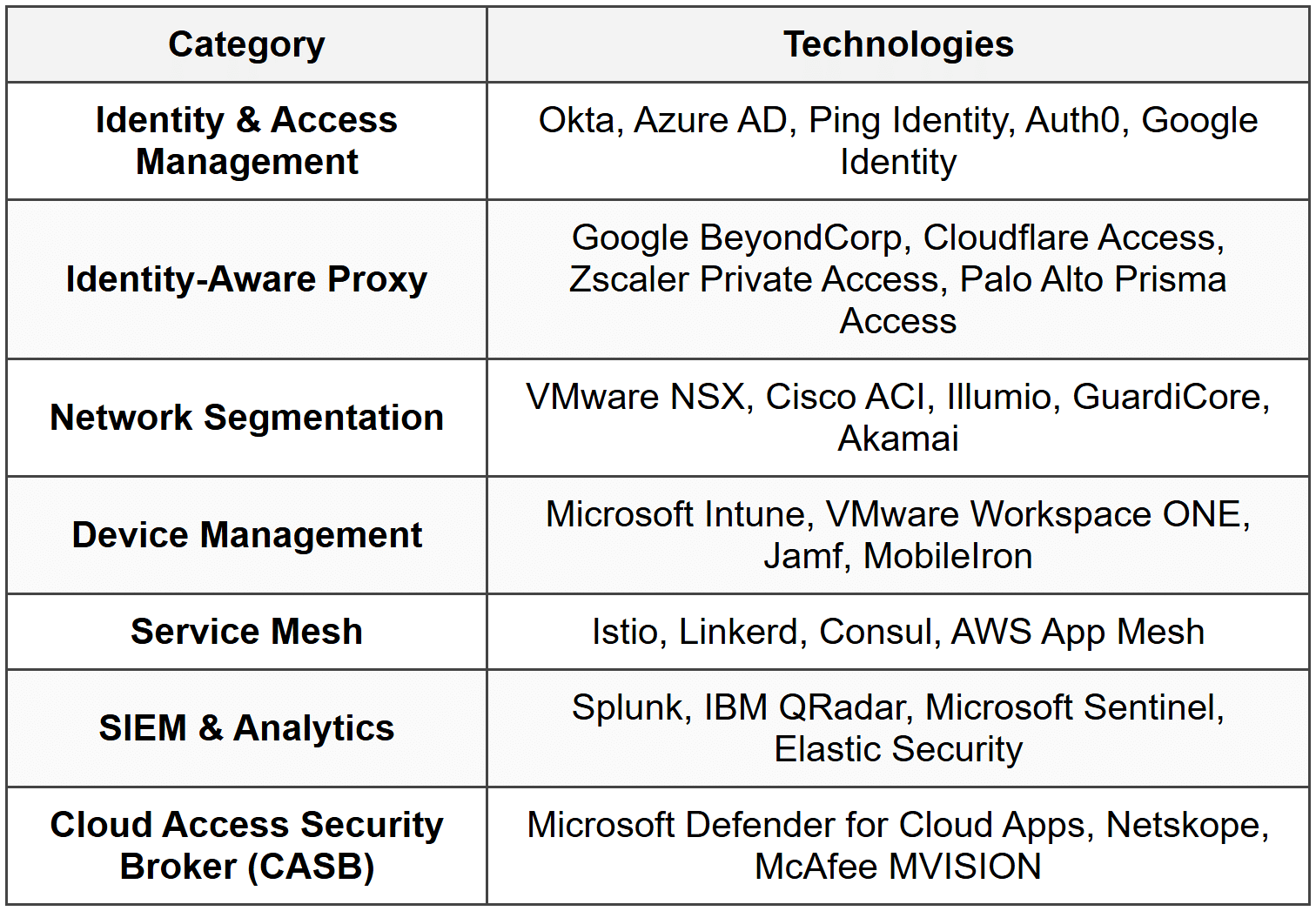
Zero Trust Technologies and Standards
Various technologies, protocols, and standards enable Zero Trust implementations.
Authentication and Authorization Standards
1. SAML (Security Assertion Markup Language)
An XML-based standard for exchanging authentication and authorization data between an identity provider and a service provider. Commonly used for enterprise single sign-on.
2. OAuth 2.0
An authorization framework that enables applications to obtain limited access to user accounts. Commonly used for API authorization and delegated access.
3. OpenID Connect (OIDC)
An identity layer built on top of OAuth 2.0 that adds authentication capabilities. Provides user identity information to applications.
4. FIDO2 / WebAuthn
Modern authentication standards that enable strong, passwordless authentication using cryptographic keys stored on hardware devices or built into devices.
Network and Encryption Technologies
1. TLS (Transport Layer Security)
Cryptographic protocol that provides secure communication over networks. Essential for encrypting Zero Trust traffic.
2. mTLS (Mutual TLS)
Extension of TLS where both client and server authenticate each other using certificates. Used for service-to-service authentication in Zero Trust architectures.
3. IPsec
Suite of protocols for securing IP communications through authentication and encryption. Used for network-layer security in some Zero Trust implementations.
4. WireGuard
Modern, lightweight VPN protocol used in some Zero Trust access solutions for creating encrypted tunnels.
Zero Trust Frameworks and Guidelines
1. NIST SP 800-207
The U.S. National Institute of Standards and Technology published Special Publication 800-207, "Zero Trust Architecture," which provides comprehensive guidance on Zero Trust principles, logical components, and deployment models. This is the primary reference document for Zero Trust implementation.
2. Forrester Zero Trust eXtended (ZTX)
Forrester Research developed the ZTX framework, expanding Zero Trust beyond network security to include data, workloads, and devices. Provides maturity model for Zero Trust adoption.
3. CISA Zero Trust Maturity Model
The U.S. Cybersecurity and Infrastructure Security Agency published a Zero Trust Maturity Model that defines five pillars (Identity, Devices, Networks, Applications and Workloads, Data) and maturity stages from traditional to optimal.
Key Technologies by Category
Measuring Zero Trust Success
Organizations need metrics to evaluate the effectiveness of their Zero Trust implementation and demonstrate progress.
Security Metrics
1. Reduction in Unauthorized Access Attempts
Track the number of blocked unauthorized access attempts over time. An effective Zero Trust implementation should reduce successful unauthorized access to near zero.
2. Mean Time to Detect (MTTD)
Measure how quickly security incidents are detected. Zero Trust's continuous monitoring should significantly reduce detection time.
3. Mean Time to Respond (MTTR)
Measure how quickly the organization responds to and contains incidents. Micro-segmentation should reduce response time by limiting blast radius.
4. Lateral Movement Prevention
Track instances where attempted lateral movement was prevented by micro-segmentation and access controls.
5. Compliance Violations
Monitor policy violations and compliance issues. Zero Trust should reduce violations through automated enforcement.
Operational Metrics
1. Policy Coverage
Percentage of resources protected by Zero Trust policies. Track progress toward 100% coverage.
2. Authentication Success Rate
Percentage of legitimate users successfully authenticated. Should remain high (>99%) even with stronger controls.
3. False Positive Rate
Instances where legitimate access is incorrectly blocked. Should be minimized through policy optimization.
4. User Experience Metrics
User satisfaction scores, help desk tickets related to access issues, and application performance metrics.
Business Metrics
1. Risk Reduction
Quantified reduction in risk exposure, often measured through risk assessments or cyber insurance evaluations.
2. Cost Avoidance
Estimated cost savings from prevented security incidents based on industry breach cost data.
3. Audit Results
Findings from security audits and compliance assessments. Zero Trust should improve audit outcomes.
4. Business Enablement
Ability to safely enable new business capabilities (remote work, cloud adoption, partner collaboration) that were previously too risky.
Future of Zero Trust
Zero Trust continues to evolve with advancing technology and changing threat landscapes.
Emerging Trends
1. AI and Machine Learning Integration
Artificial intelligence enhances Zero Trust through:
- More sophisticated behavioral analytics
- Automated policy optimization
- Predictive threat detection
- Adaptive authentication based on risk scoring
- Automated response to anomalies
2. Extended Detection and Response (XDR)
Integration of Zero Trust with XDR platforms provides:
- Unified visibility across endpoints, networks, and cloud
- Correlated threat intelligence
- Automated investigation and response
- Context-aware security decisions
3. Zero Trust for OT/IoT
Expansion of Zero Trust principles to operational technology and Internet of Things environments, addressing unique challenges of resource-constrained devices and real-time systems.
4. Passwordless Authentication
Movement toward eliminating passwords entirely using:
- Biometric authentication
- Hardware security keys
- Device-based certificates
- Risk-based authentication
5. Quantum-Resistant Cryptography
Preparation for quantum computing threats through adoption of post-quantum cryptographic algorithms in Zero Trust implementations.
Industry Adoption
Zero Trust adoption is accelerating across industries:
- Government: U.S. federal mandate requiring agencies to implement Zero Trust architectures
- Financial Services: High adoption due to regulatory requirements and high-value targets
- Healthcare: Growing adoption to protect sensitive patient data and comply with HIPAA
- Retail: Implementation to secure customer data and payment systems
- Manufacturing: Protection of intellectual property and industrial control systems
Review Questions
- What is the fundamental principle of Zero Trust Architecture, and how does it differ from traditional perimeter-based security?
- Explain the concept of "assume breach" and why it is important in Zero Trust Architecture.
- What are the three main pillars of Zero Trust, and what role does each play in securing the network?
- Describe what micro-segmentation is and explain how it prevents lateral movement attacks.
- What is the role of the Policy Engine and Policy Enforcement Point in a Zero Trust Architecture?
- Why is continuous verification important in Zero Trust, and what kinds of factors are evaluated during continuous verification?
- Explain the difference between least privilege access and traditional access control models.
- What is a Software-Defined Perimeter (SDP), and how does it implement Zero Trust principles?
- List and explain at least four challenges organizations face when implementing Zero Trust Architecture.
- How does Zero Trust Architecture support remote workforce security differently than traditional VPN approaches?
- What is the purpose of device trust in Zero Trust, and what factors are evaluated when assessing device health?
- Explain how Zero Trust complements other network hardening techniques to provide defense in depth.
- Why is comprehensive visibility and logging critical to Zero Trust implementation?
- What is the difference between authentication and authorization in the context of Zero Trust?
- Describe a practical scenario where Zero Trust would prevent a security incident that traditional perimeter security might miss.
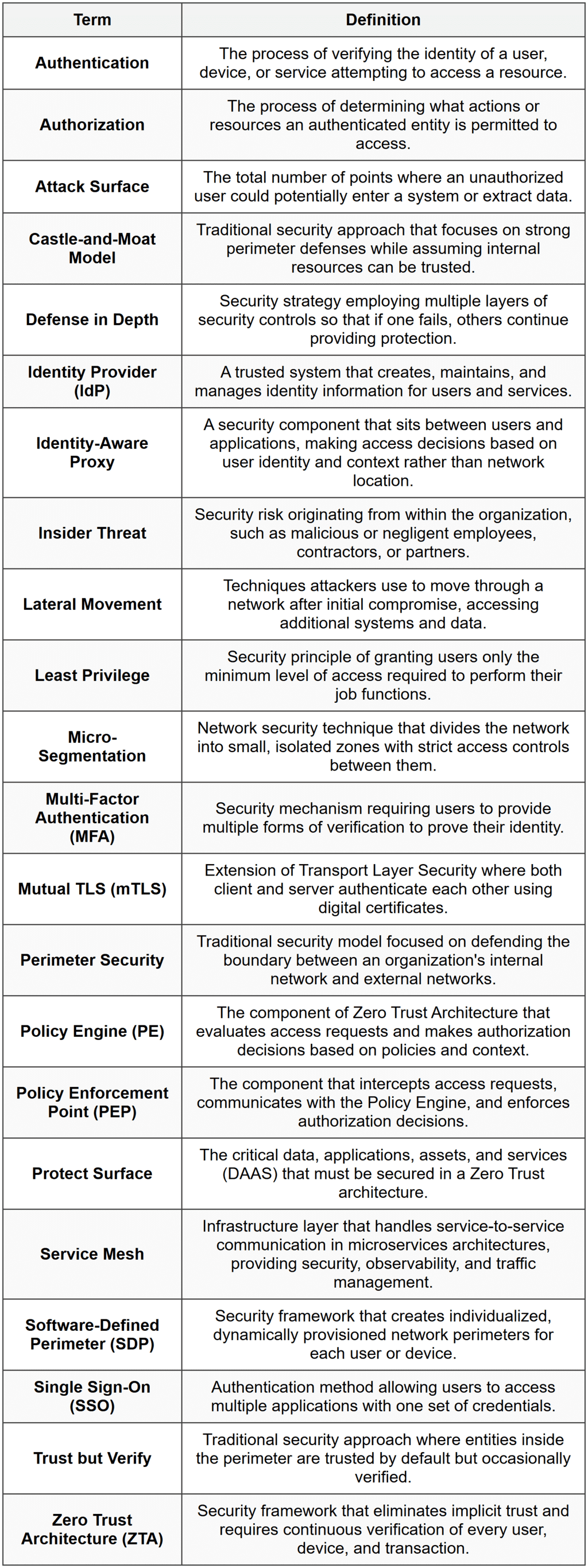
Glossary