Assignment : IPv6 Addressing
IPv6 Addressing is a fundamental component of modern computer networking, introduced to overcome the address exhaustion problem of IPv4. IPv6 uses 128-bit addresses compared to IPv4's 32-bit addresses, providing an exponentially larger address space. Understanding IPv6 addressing structure, types, notation, and configuration methods is essential for network engineering and technical examinations. This topic covers address representation, header structure, address types, special addresses, and transition mechanisms from IPv4 to IPv6.
1. IPv6 Address Structure and Notation
1.1 Basic Address Format
- Address Length: IPv6 uses 128 bits (16 bytes) for addressing, compared to 32 bits in IPv4.
- Total Address Space: 2128 ≈ 3.4 × 1038 unique addresses.
- Hexadecimal Representation: IPv6 addresses are written in hexadecimal format, divided into 8 groups of 16 bits (4 hexadecimal digits) each.
- Standard Notation: Each group is separated by colons (:). Example: 2001:0DB8:0000:0000:0000:FF00:0042:8329
1.2 Address Compression Rules
- Leading Zero Suppression: Leading zeros within each 16-bit block can be omitted. Example: 2001:0DB8 becomes 2001:DB8
- Double Colon (::) Rule: Consecutive blocks of zeros can be replaced with double colon (::), but only once per address to avoid ambiguity.
- Example Compression: 2001:0DB8:0000:0000:0000:FF00:0042:8329 becomes 2001:DB8::FF00:42:8329
- Trap Alert: You cannot use :: more than once in a single address. If multiple zero sequences exist, compress the longest one; if equal length, compress the first one.
1.3 Prefix Notation
- CIDR Notation: IPv6 uses slash notation similar to IPv4 to indicate network prefix length.
- Format: IPv6-address/prefix-length. Example: 2001:DB8:ACAD:1::/64
- Network Portion: First n bits (specified by prefix length) represent the network.
- Interface ID Portion: Remaining bits (128 - n) represent the host/interface identifier.
- Common Prefix Lengths: /64 (standard subnet), /48 (organization), /32 (ISP allocation), /128 (single host).
2. IPv6 Address Types
2.1 Unicast Addresses
Unicast addresses identify a single network interface. A packet sent to a unicast address is delivered to that specific interface.
- Global Unicast Address (GUA): Routable on the internet, similar to IPv4 public addresses. Range: 2000::/3 (addresses starting with 2 or 3).
- Link-Local Address: Used for communication on a single link (subnet), not routable. Range: FE80::/10. Auto-configured on all IPv6-enabled interfaces.
- Unique Local Address (ULA): Private addresses for internal use, not routable on internet. Range: FC00::/7 (typically FD00::/8 used).
- Loopback Address: ::1/128 (equivalent to 127.0.0.1 in IPv4). Used for testing local TCP/IP stack.
- Unspecified Address: ::/128 (all zeros). Indicates absence of address, used by hosts during initial configuration.
2.2 Multicast Addresses
Multicast addresses identify a group of interfaces. A packet sent to a multicast address is delivered to all interfaces in the group.
- Range: FF00::/8 (all addresses starting with FF).
- Format: FF0S::/8, where S represents scope (1=interface-local, 2=link-local, 5=site-local, 8=organization-local, E=global).
- All Nodes Multicast: FF02::1 - reaches all IPv6 devices on the local link.
- All Routers Multicast: FF02::2 - reaches all IPv6 routers on the local link.
- Solicited-Node Multicast: FF02::1:FF00:0000/104 - used in Neighbor Discovery Protocol for address resolution.
- Trap Alert: IPv6 does NOT use broadcast addresses. Multicast addresses replace broadcast functionality.
2.3 Anycast Addresses
- Definition: Anycast addresses are assigned to multiple interfaces (typically on different nodes). Packet is delivered to the nearest interface (by routing metric).
- Format: Use the same address space as unicast addresses; distinction is in configuration, not address structure.
- Common Use: Load balancing, redundancy, DNS root servers.
- Subnet-Router Anycast: Address with all zeros in interface ID portion (e.g., 2001:DB8:ACAD:1::/64 becomes 2001:DB8:ACAD:1::).
3. IPv6 Global Unicast Address Structure
3.1 Address Components
- Global Routing Prefix: First 48 bits (typically). Assigned by ISP, identifies organization's network.
- Subnet ID: Next 16 bits. Allows organization to create internal subnets (65,536 subnets possible).
- Interface ID: Last 64 bits. Identifies specific interface on the subnet.
- Standard Allocation: /48 to organizations, allowing /64 subnets (IETF recommendation).
3.2 Interface ID Generation Methods
- EUI-64 (Extended Unique Identifier): Derives 64-bit interface ID from 48-bit MAC address. Inserts FFFE in the middle and flips the 7th bit (U/L bit).
- EUI-64 Process: Split MAC (24 bits + 24 bits) → Insert FFFE → Flip 7th bit → Create 64-bit interface ID.
- Example: MAC FC99:4775:CEE0 becomes FE99:47FF:FE75:CEE0 (after flipping 7th bit).
- Random Generation: Modern systems use privacy extensions (RFC 4941) to generate random interface IDs for security and privacy.
- Manual Configuration: Administrators can manually assign interface IDs.
- DHCPv6: Dynamic Host Configuration Protocol for IPv6 can assign complete addresses or interface IDs.
4. Special IPv6 Addresses and Prefixes
4.1 Reserved and Special Addresses
- Default Route: ::/0 - represents all IPv6 addresses (used in routing tables).
- IPv4-Mapped IPv6 Address: ::FFFF:0:0/96 - allows IPv6 applications to communicate with IPv4 nodes. Example: ::FFFF:192.0.2.1
- IPv4-Compatible IPv6 Address: ::/96 (deprecated) - used during early IPv6 transition.
- Documentation Prefix: 2001:DB8::/32 - reserved for examples and documentation (never routed on internet).
- 6to4 Prefix: 2002::/16 - used for automatic tunneling between IPv6 sites over IPv4 infrastructure.
4.2 Link-Local Address Details
- Mandatory Configuration: Every IPv6-enabled interface must have a link-local address, automatically configured.
- Format: FE80::/10 prefix + 54 zero bits + 64-bit interface ID = FE80:0000:0000:0000:interface-ID/64
- Usage: Neighbor Discovery Protocol, router advertisements, local communication, next-hop addresses in routing.
- Scope: Valid only on the specific link; routers do not forward packets with link-local source or destination.
- Zone ID: Link-local addresses may require zone identifier when multiple interfaces exist (e.g., FE80::1%eth0).
5. IPv6 Header Structure
5.1 Basic Header Format
- Fixed Header Size: 40 bytes (simplified compared to IPv4's variable header).
- Version (4 bits): Always set to 6 for IPv6.
- Traffic Class (8 bits): Used for QoS (Quality of Service) and prioritization, similar to IPv4 ToS field.
- Flow Label (20 bits): Identifies packets belonging to same flow for special handling (e.g., real-time traffic).
- Payload Length (16 bits): Size of payload (data after header) in bytes, maximum 65,535 bytes.
- Next Header (8 bits): Identifies type of header following IPv6 header (TCP, UDP, ICMPv6, or extension header).
- Hop Limit (8 bits): Decremented by 1 at each router; packet discarded when reaching 0 (equivalent to IPv4 TTL).
- Source Address (128 bits): IPv6 address of sender.
- Destination Address (128 bits): IPv6 address of intended recipient.
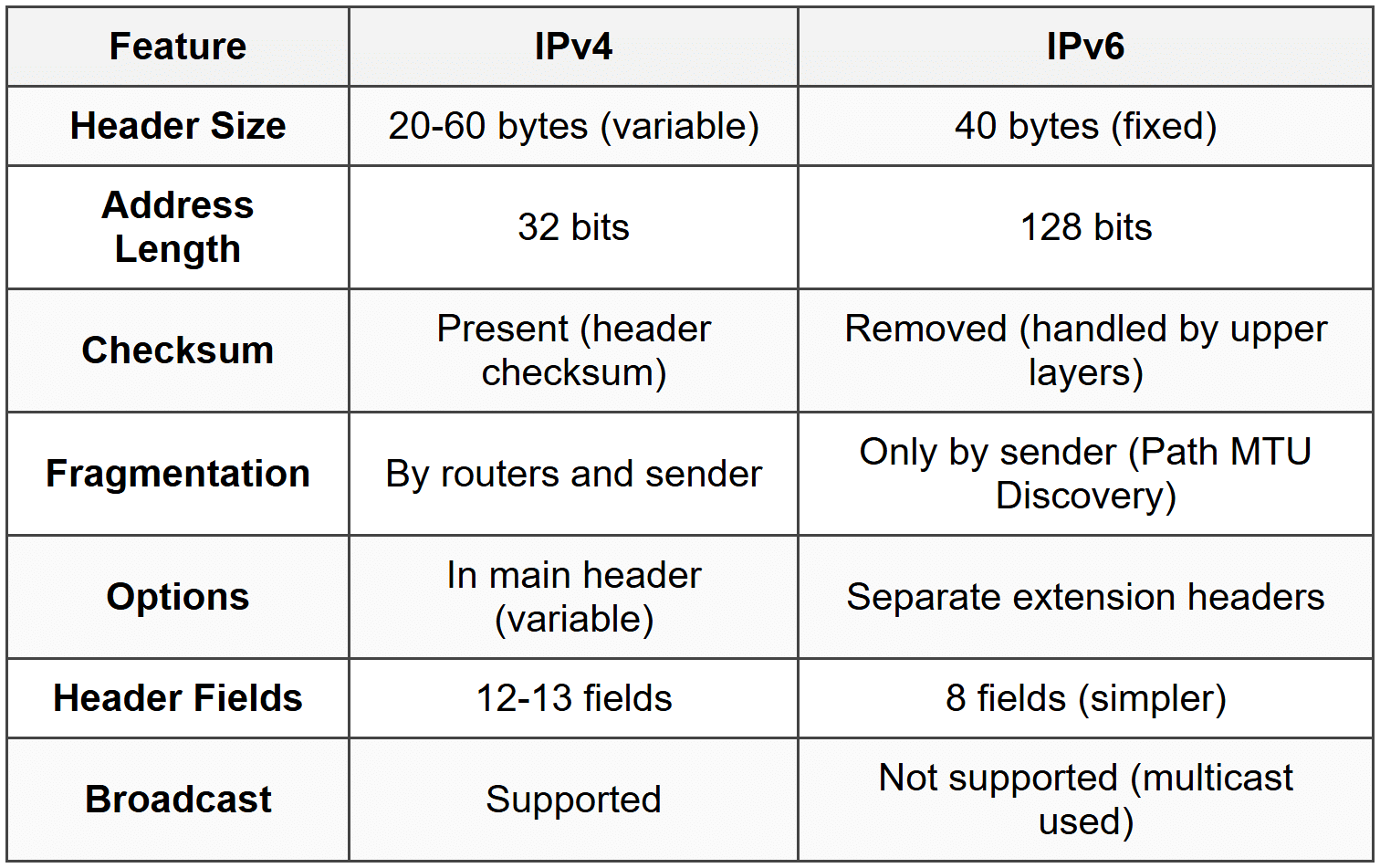
5.2 IPv6 vs IPv4 Header Comparison
5.3 Extension Headers
- Purpose: Provide optional functionality without increasing basic header size. Processed only by destination (except Hop-by-Hop).
- Hop-by-Hop Options: Examined by every node along path. Must immediately follow IPv6 header.
- Routing Header: Specifies list of intermediate nodes to visit (similar to IPv4 source routing).
- Fragment Header: Used by source to send packets larger than path MTU. Contains fragment offset and identification.
- Destination Options: Carries optional information for destination node only.
- Authentication Header (AH): Provides authentication and integrity (IPsec).
- Encapsulating Security Payload (ESP): Provides confidentiality, authentication, and integrity (IPsec).
- Chaining: Multiple extension headers can be chained; Next Header field indicates following header type.
6. IPv6 Address Configuration Methods
6.1 Stateless Address Autoconfiguration (SLAAC)
- Definition: Allows devices to automatically configure IPv6 addresses without DHCP server.
- Process Steps:
- Interface generates link-local address (FE80::/10 + EUI-64 or random interface ID).
- Performs Duplicate Address Detection (DAD) using Neighbor Solicitation messages.
- Sends Router Solicitation (RS) message to FF02::2 (all routers).
- Receives Router Advertisement (RA) containing network prefix, prefix length, and configuration flags.
- Combines received prefix with interface ID to create global unicast address.
- Configures default gateway from RA source address.
- Advantages: No server required, simple deployment, automatic configuration.
- Limitations: Cannot provide DNS server information, limited control over address assignment.
- RA Flags: M-flag (Managed) and O-flag (Other) control SLAAC vs DHCPv6 usage.
6.2 DHCPv6 (Dynamic Host Configuration Protocol for IPv6)
- Stateful DHCPv6: Server maintains state information, assigns complete addresses and configuration parameters (DNS, domain name).
- Stateless DHCPv6: Hosts use SLAAC for addresses; DHCPv6 provides only additional parameters (DNS servers, domain name).
- Message Types: SOLICIT, ADVERTISE, REQUEST, REPLY, RENEW, REBIND, RELEASE, DECLINE, INFORMATION-REQUEST.
- DHCPv6 Server Address: FF02::1:2 (All DHCP Agents multicast address).
- RA Flag Control: M-flag=1, O-flag=0 → Stateful DHCPv6. M-flag=0, O-flag=1 → Stateless DHCPv6. Both=0 → SLAAC only.
6.3 Manual Configuration
- Static Assignment: Administrator manually configures IPv6 address, prefix length, default gateway, and DNS servers.
- Use Cases: Servers, routers, network infrastructure devices requiring fixed addresses.
- Verification Required: Must ensure no address conflicts and correct prefix assignment.
7. Neighbor Discovery Protocol (NDP)
7.1 NDP Functions
Neighbor Discovery Protocol (NDP) operates at the network layer using ICMPv6 messages. It replaces several IPv4 protocols including ARP.
- Address Resolution: Determines link-layer address (MAC) from IPv6 address (replaces ARP).
- Router Discovery: Hosts locate routers on local link.
- Prefix Discovery: Hosts learn network prefixes for on-link determination.
- Parameter Discovery: Learns MTU, hop limit, and other parameters.
- Duplicate Address Detection (DAD): Ensures address uniqueness before use.
- Neighbor Unreachability Detection: Determines if neighbors are reachable.
- Redirection: Routers inform hosts of better first-hop routers for specific destinations.
7.2 NDP Message Types
- Router Solicitation (RS): ICMPv6 Type 133. Sent by hosts to request Router Advertisements. Destination: FF02::2.
- Router Advertisement (RA): ICMPv6 Type 134. Sent by routers periodically or in response to RS. Contains prefix, flags, lifetime.
- Neighbor Solicitation (NS): ICMPv6 Type 135. Used for address resolution, DAD, and neighbor reachability. Sent to solicited-node multicast.
- Neighbor Advertisement (NA): ICMPv6 Type 136. Response to NS, contains link-layer address.
- Redirect: ICMPv6 Type 137. Routers inform hosts of better next-hop for destination.
7.3 Solicited-Node Multicast Address
- Format: FF02::1:FF00:0000/104 + last 24 bits of target IPv6 address.
- Purpose: Efficient address resolution without broadcasting to all nodes.
- Example: For address 2001:DB8::1234:5678, solicited-node multicast is FF02::1:FF34:5678.
- Efficiency: Only nodes with matching last 24 bits listen; reduces processing overhead compared to broadcast.
8. IPv6 Subnetting
8.1 Subnetting Principles
- Standard Subnet: /64 is recommended subnet size. Provides 264 addresses per subnet and compatibility with SLAAC.
- Subnet Calculation: Borrow bits from interface ID portion to create subnet ID.
- Hexadecimal Math: Each hex digit represents 4 bits. Incrementing subnet ID increases hex values.
- Example: Given 2001:DB8:ACAD::/48, create /64 subnets by varying bits 49-64.
8.2 Subnetting Example
Organization receives 2001:DB8:CAFE::/48. Creating /64 subnets:
- Subnet 0: 2001:DB8:CAFE:0000::/64 (or 2001:DB8:CAFE::/64)
- Subnet 1: 2001:DB8:CAFE:0001::/64 (or 2001:DB8:CAFE:1::/64)
- Subnet 2: 2001:DB8:CAFE:0002::/64 (or 2001:DB8:CAFE:2::/64)
- Subnet 255: 2001:DB8:CAFE:00FF::/64 (or 2001:DB8:CAFE:FF::/64)
- Subnet 256: 2001:DB8:CAFE:0100::/64 (or 2001:DB8:CAFE:100::/64)
- Total Subnets: 216 = 65,536 /64 subnets from a /48 allocation.
8.3 Trap Alert - Common Subnetting Mistakes
- Mistake 1: Using subnet masks instead of prefix length. IPv6 uses only CIDR notation (/prefix).
- Mistake 2: Creating subnets smaller than /64 breaks SLAAC functionality.
- Mistake 3: Forgetting hexadecimal counting (0-9, A-F). After 9 comes A, not 10.
- Mistake 4: Confusing compressed and uncompressed formats when calculating boundaries.
9. IPv4 to IPv6 Transition Mechanisms
9.1 Dual Stack
- Definition: Devices run both IPv4 and IPv6 protocol stacks simultaneously.
- Operation: Application chooses appropriate protocol based on destination address and DNS response.
- Advantages: Simplest transition method, full functionality for both protocols, no translation required.
- Disadvantages: Requires maintenance of two separate infrastructures, does not solve IPv4 exhaustion.
- Use Case: Long-term coexistence during gradual migration period.
9.2 Tunneling Mechanisms
- Principle: Encapsulates IPv6 packets within IPv4 packets to traverse IPv4-only networks.
- Manual Tunneling: Administrators manually configure tunnel endpoints. Point-to-point, static configuration.
- 6to4 Tunneling: Automatic tunneling using 2002::/16 prefix. Embeds IPv4 address in IPv6 address for routing.
- 6to4 Format: 2002:IPv4-address-in-hex:subnet:interface-ID. Example: IPv4 192.0.2.1 → 2002:C000:0201::/48
- ISATAP (Intra-Site Automatic Tunnel Addressing Protocol): Automatic tunneling within organization. Uses 0000:5EFE in interface ID.
- Teredo: Tunneling for hosts behind NAT devices. Uses 2001:0000::/32 prefix. Encapsulates IPv6 in IPv4 UDP packets.
9.3 Translation Mechanisms
- NAT64: Network Address Translation between IPv6 and IPv4. Allows IPv6-only clients to access IPv4 servers.
- DNS64: Works with NAT64. Synthesizes AAAA records (IPv6) from A records (IPv4) when no native IPv6 address exists.
- Operation: IPv6 client queries DNS64 → receives synthesized IPv6 address → sends packet to NAT64 → NAT64 translates to IPv4.
- Well-Known Prefix: 64:FF9B::/96 used for algorithmic mapping between IPv6 and IPv4 addresses.
- Use Case: IPv6-only networks accessing legacy IPv4 services.
10. ICMPv6 (Internet Control Message Protocol for IPv6)
10.1 ICMPv6 Functions
- Error Reporting: Reports packet processing errors (destination unreachable, time exceeded, parameter problem).
- Diagnostic Functions: Echo Request/Reply (ping), used for connectivity testing.
- Neighbor Discovery: Implements NDP messages (RS, RA, NS, NA, Redirect).
- Multicast Listener Discovery (MLD): Manages multicast group memberships (replaces IGMP in IPv4).
- Path MTU Discovery: Discovers maximum transmission unit along path to avoid fragmentation.
10.2 Important ICMPv6 Message Types
- Type 1: Destination Unreachable (codes: no route, administratively prohibited, address unreachable, port unreachable).
- Type 2: Packet Too Big - used in Path MTU Discovery. Router cannot forward; packet exceeds link MTU.
- Type 3: Time Exceeded (hop limit exceeded or fragment reassembly time exceeded).
- Type 4: Parameter Problem (erroneous header field or unrecognized Next Header type).
- Type 128: Echo Request (ping request).
- Type 129: Echo Reply (ping response).
- Types 133-137: Neighbor Discovery Protocol messages.
- Types 130, 131, 132: Multicast Listener Discovery (MLDv1) messages.
10.3 ICMPv6 vs ICMPv4 Differences
- Integrated Functions: ICMPv6 includes neighbor discovery and multicast management (separate protocols in IPv4).
- No ARP: Address resolution handled by ICMPv6 Neighbor Solicitation/Advertisement, not separate ARP protocol.
- Mandatory: ICMPv6 is essential for IPv6 operation; blocking it breaks basic functionality (unlike ICMPv4).
- Packet Too Big: Routers must send this message when packet exceeds MTU (IPv6 routers don't fragment).
11. IPv6 Security Features
11.1 Built-in Security
- IPsec Mandatory Support: IPv6 specifications originally required IPsec implementation (now recommended, not mandatory).
- Authentication Header (AH): Provides data integrity and authentication. Protects against tampering and spoofing.
- Encapsulating Security Payload (ESP): Provides confidentiality (encryption), authentication, and integrity.
- End-to-End Security: No NAT in IPv6 enables true end-to-end IPsec without translation issues.
11.2 Security Considerations
- Larger Address Space: Makes network scanning difficult but not impossible. Reconnaissance attacks require new techniques.
- Privacy Extensions: RFC 4941 temporary addresses prevent tracking based on static interface IDs (EUI-64 reveals MAC).
- NDP Vulnerabilities: Router Advertisement spoofing, Neighbor Solicitation/Advertisement spoofing. Mitigated by SEcure Neighbor Discovery (SEND).
- SEND (RFC 3971): Uses cryptographic signatures to secure NDP messages. Prevents RA spoofing and man-in-the-middle attacks.
- First-Hop Security: RA Guard, DHCPv6 Guard, Binding Table, Neighbor Discovery Inspection implemented on switches.
11.3 Common IPv6 Security Threats
- Rogue Router Advertisements: Attacker sends fake RAs to redirect traffic or cause denial of service.
- Neighbor Cache Exhaustion: Flooding with NS messages fills neighbor cache, causing resource exhaustion.
- Extension Header Attacks: Malformed or excessively long extension header chains exploit processing vulnerabilities.
- Fragmentation Attacks: Crafted fragments bypass security filters or cause reassembly resource exhaustion.
- Tunneling Exploits: Transition mechanisms (6to4, Teredo) can bypass firewall policies and create covert channels.
12. IPv6 Address Planning and Best Practices
12.1 Address Allocation Strategy
- Hierarchical Allocation: RIRs → ISPs → Organizations → Subnets → Hosts. Enables aggregation and efficient routing.
- Provider-Independent (PI) vs Provider-Aggregatable (PA): PI addresses owned by organization; PA addresses from ISP pool.
- Sparse Allocation: Use non-contiguous subnet numbers to allow future growth and maintain flexibility.
- Documentation: Maintain clear IPv6 addressing scheme documentation and IPAM (IP Address Management) systems.
12.2 Best Practices
- Use /64 for Subnets: Always assign /64 to end-user subnets for SLAAC compatibility and standardization.
- Reserve /127 for Point-to-Point Links: Conserves addresses and prevents security issues on router-to-router links.
- Implement Privacy Extensions: Enable RFC 4941 temporary addresses on client devices for privacy.
- Plan for Growth: IPv6 abundance doesn't mean waste; plan logical, hierarchical addressing for manageability.
- Use Meaningful Patterns: Embed location, function, or VLAN information in subnet ID for easier troubleshooting.
- Consistent Addressing: Maintain consistent patterns across organization (e.g., routers always end in ::1).
12.3 Common Deployment Mistakes
- Treating IPv6 Like IPv4: IPv6's abundance requires different thinking; subnetting smaller than /64 is counterproductive.
- Ignoring Security: Deploying IPv6 without proper security controls (ACLs, firewalls updated for IPv6).
- No Monitoring: Failing to monitor IPv6 traffic separately; attacks can occur on IPv6 while monitoring only IPv4.
- Incomplete Dual-Stack: Enabling IPv6 without proper DNS AAAA records, application testing, or IPv6 firewall rules.
IPv6 addressing represents a fundamental shift in network architecture, providing virtually unlimited address space and improved functionality over IPv4. Understanding IPv6 address structure, types, configuration methods, and transition mechanisms is critical for modern network professionals. Key concepts include the 128-bit addressing scheme with hexadecimal notation, compression rules, multiple address types (unicast, multicast, anycast), the simplified 40-byte header, Neighbor Discovery Protocol replacing ARP, and SLAAC enabling automatic configuration. The transition from IPv4 to IPv6 involves dual-stack operation, tunneling mechanisms, and translation technologies. Mastery of IPv6 addressing requires understanding not only technical specifications but also security implications, planning strategies, and best practices for deployment in production environments.





