Assignment : VPN & Remote Access
Section 1: Multiple Choice Questions
- Q1. A company wants to allow remote employees to securely access internal resources over the internet. Which VPN protocol would be most appropriate if they need strong encryption and compatibility with modern operating systems, but NAT traversal is a concern?
- PPTP because it offers the fastest connection speeds
- L2TP/IPsec because it combines strong encryption with wide compatibility and supports NAT traversal
- IPsec in transport mode because it encrypts only the payload
- GRE because it provides built-in encryption for tunneling
- Q2. An administrator notices that remote users connecting via VPN are experiencing slow performance when accessing cloud applications. The VPN is configured to route all traffic through the corporate network. What is the most likely cause and solution?
- The VPN server is underpowered; upgrade the server hardware
- Split tunneling is disabled, causing all internet traffic to route through the corporate network; enable split tunneling for cloud apps
- The encryption algorithm is too weak; switch to AES-256
- The remote users have insufficient bandwidth; require minimum internet speeds
- Q3. A site-to-site VPN connects two branch offices. Traffic between the offices is encrypted, but users report intermittent connectivity issues. Logs show repeated rekeying events. What is the most appropriate troubleshooting step?
- Disable encryption to improve stability
- Check if the IKE lifetime and IPsec SA lifetime settings match on both endpoints
- Switch from site-to-site VPN to remote access VPN
- Implement load balancing across multiple VPN tunnels
- Q4. An organization implements SSL VPN for remote access instead of IPsec VPN. Which scenario best justifies this decision?
- Users need to access resources from devices where they cannot install VPN client software and must work through web browsers
- The organization requires the fastest possible connection speeds for large file transfers
- All users have company-managed devices with pre-installed software
- The network infrastructure does not support TCP connections
- Q5. A remote access VPN is configured with two-factor authentication, AES-256 encryption, and perfect forward secrecy. However, an attacker who compromises the VPN server's storage could potentially decrypt previously captured traffic if which component is not properly implemented?
- The two-factor authentication system
- The perfect forward secrecy mechanism, which should ensure session keys are not derived from long-term keys
- The AES-256 encryption algorithm
- The user password policy
Section 2: Short Answer Questions
- Q1. Explain the difference between a site-to-site VPN and a remote access VPN. Provide one specific use case for each type.
- Q2. What is split tunneling in the context of VPN connections? Discuss one advantage and one security concern associated with enabling split tunneling.
- Q3. Describe the role of IPsec's two main protocols (AH and ESP) and explain why ESP is more commonly used in modern VPN implementations.
- Q4. What is the purpose of the IKE (Internet Key Exchange) protocol in IPsec VPNs, and what happens during IKE Phase 1 and Phase 2?
Section 3: Analytical / Applied Tasks
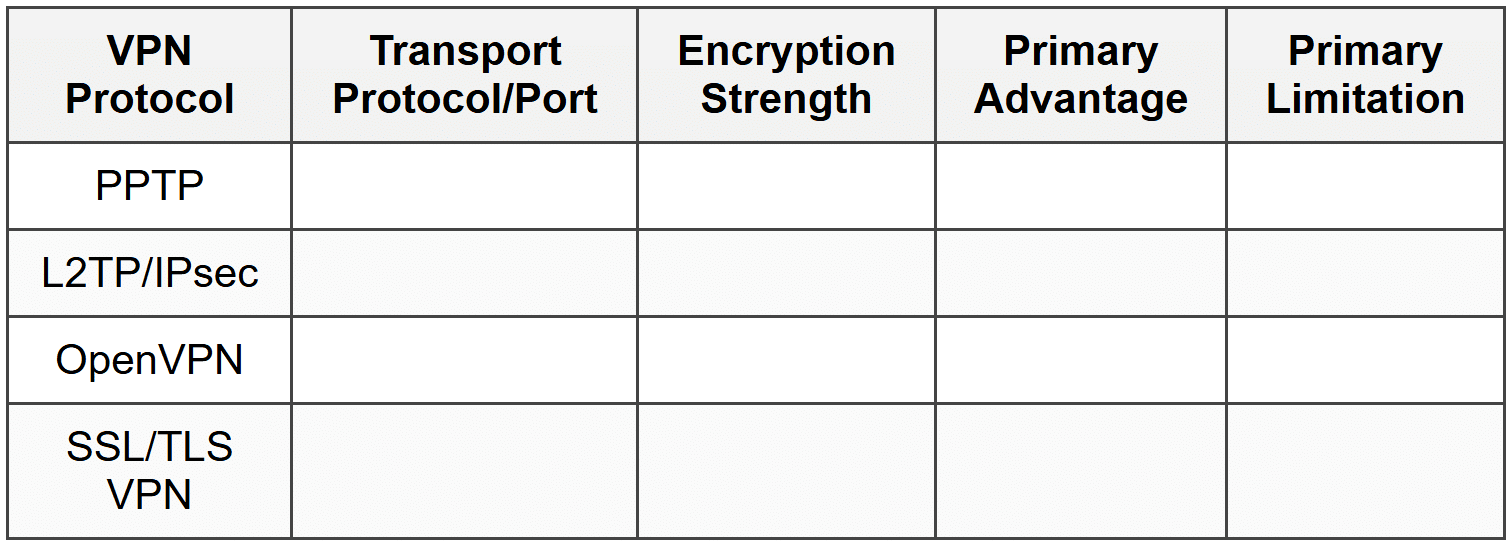
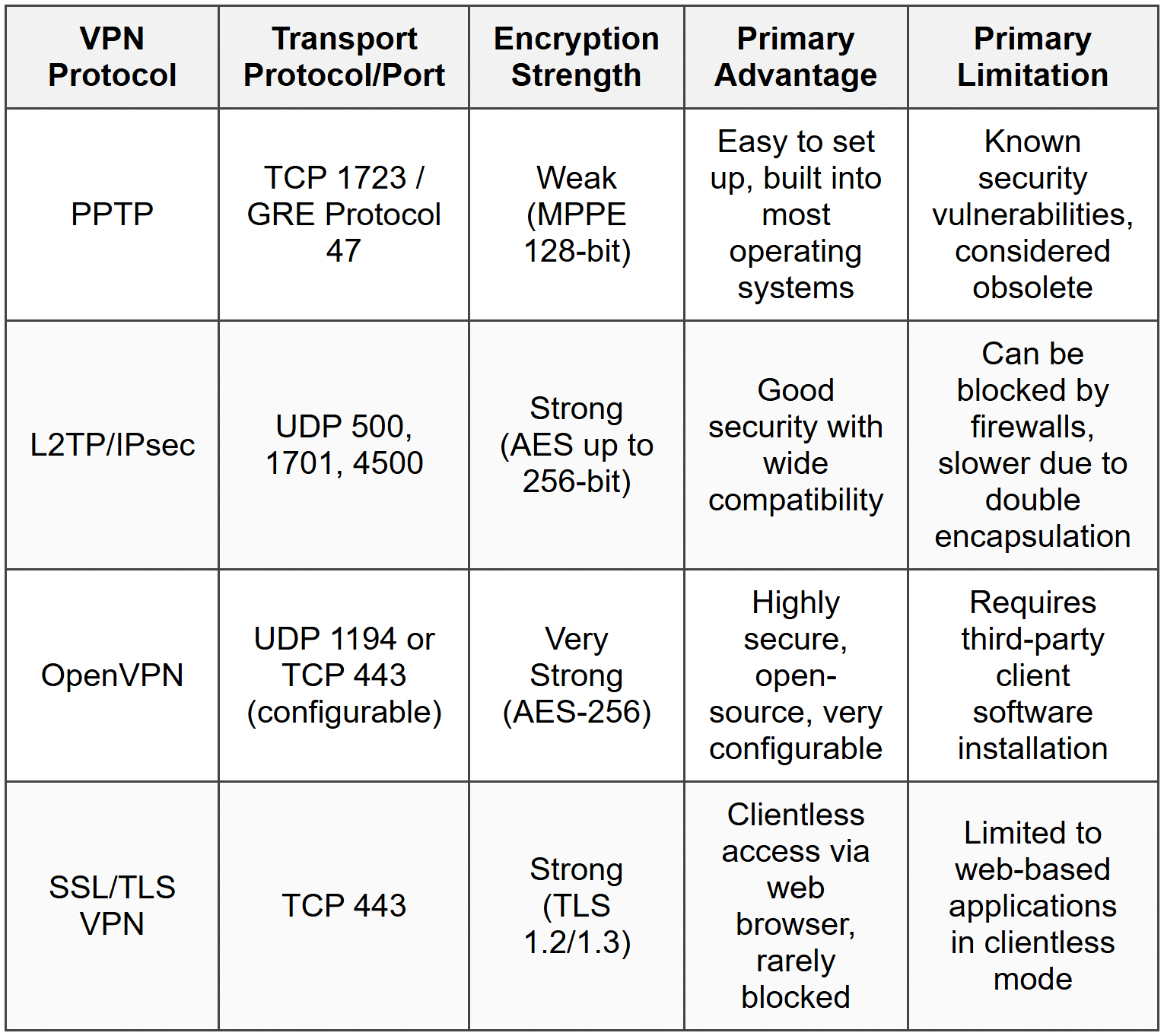
- Q1. Complete the following table comparing different VPN protocols:
- Q2. A company has three offices: Headquarters (HQ), Branch A, and Branch B. Draw a labeled network diagram description showing how site-to-site VPN tunnels would be configured to connect all three offices. Include the following elements:
- VPN gateways at each location
- VPN tunnels with labels indicating encryption
- Internal network subnets (you may use example addresses like 192.168.1.0/24)
- Internet connectivity at each site
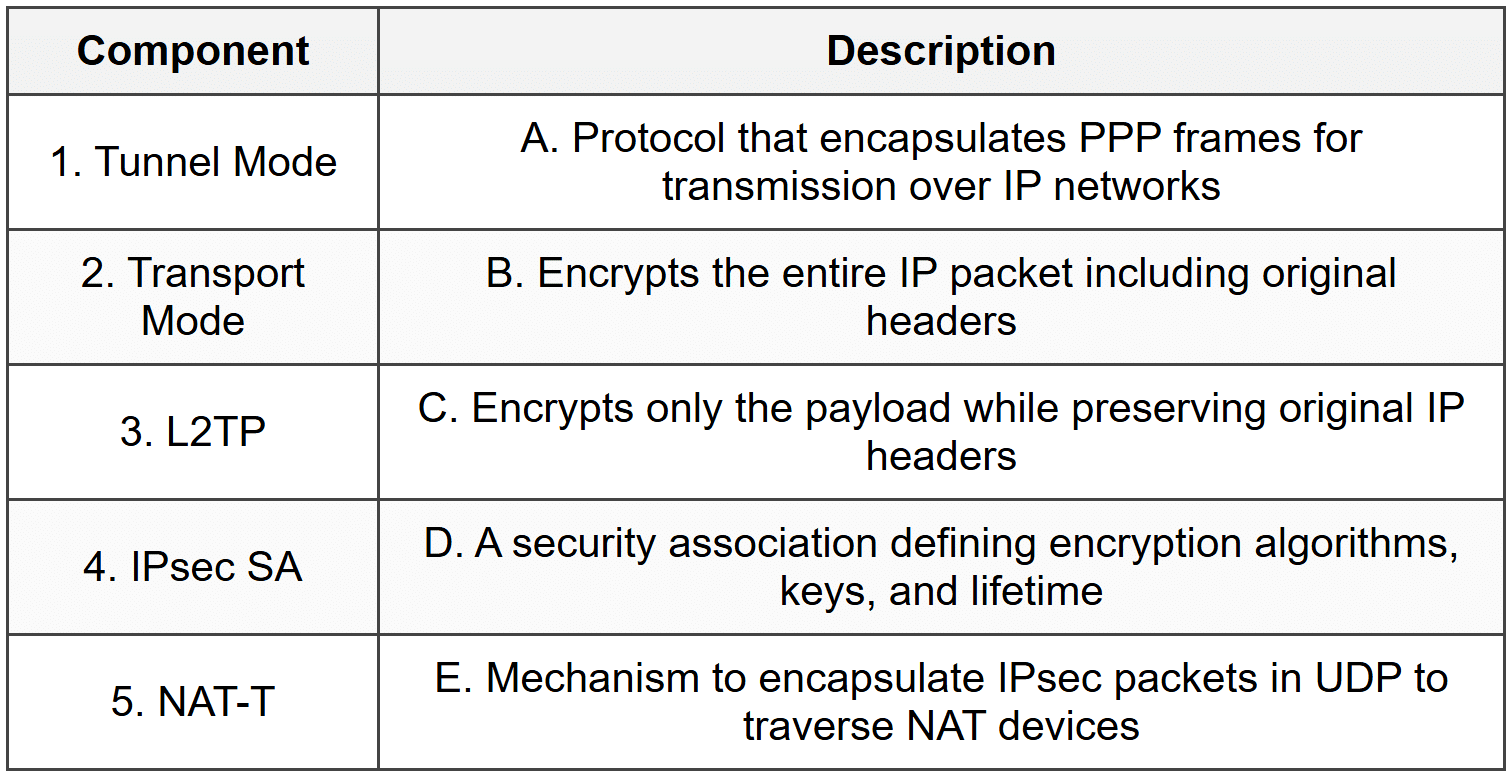
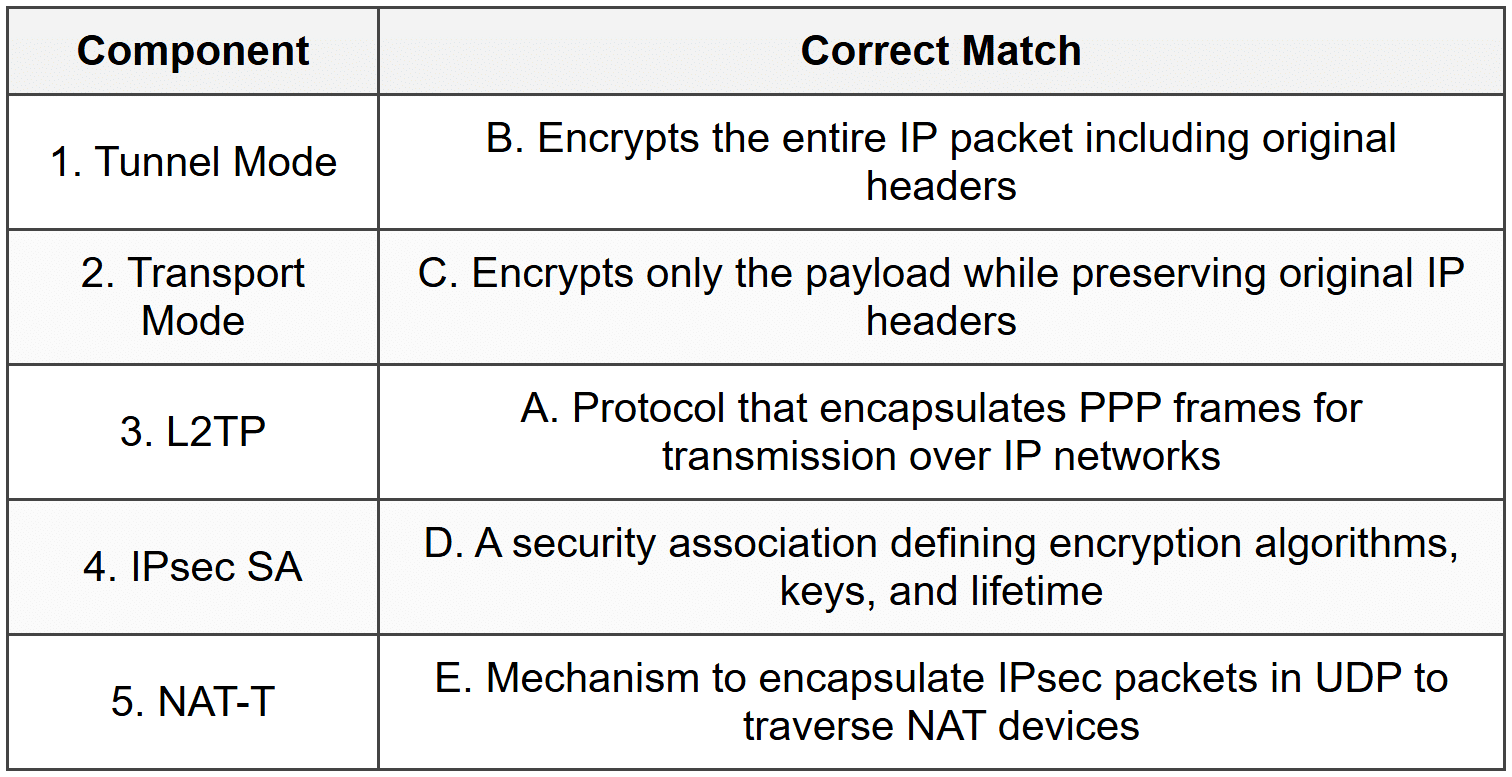
- Q3. Match the following VPN components with their correct descriptions:
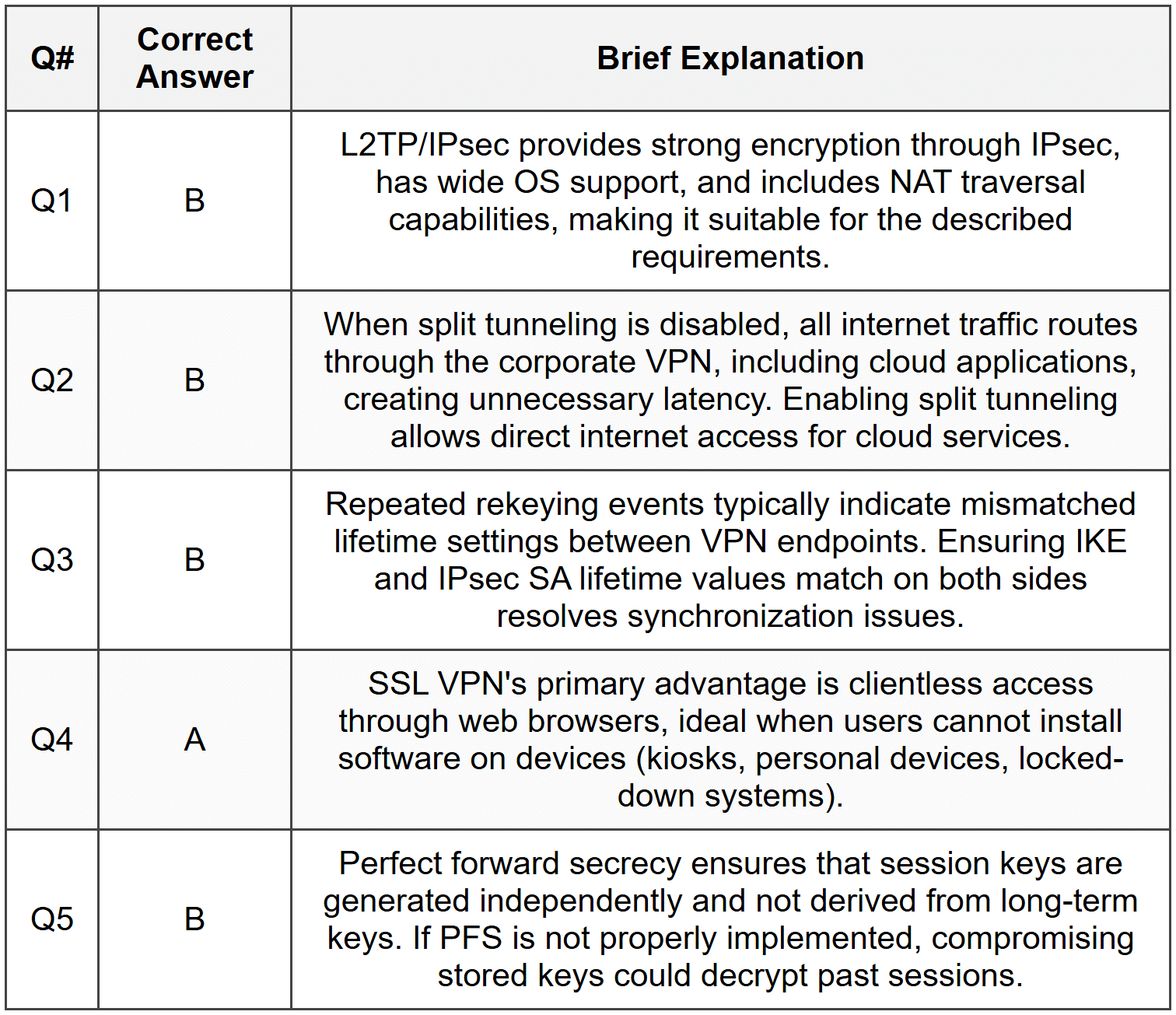
Section 4: Multiple Choice Questions
- Q1. Which port does PPTP use for its control channel?
- (A) TCP port 443
- (B) TCP port 1723
- (C) UDP port 500
- (D) UDP port 1701
- Q2. In IPsec, what is the primary function of Authentication Header (AH)?
- (A) Provide encryption of the payload data
- (B) Provide data integrity and authentication without encryption
- (C) Establish the initial tunnel connection
- (D) Perform network address translation
- Q3. What does perfect forward secrecy (PFS) ensure in VPN communications?
- (A) Each session uses unique encryption keys that cannot be derived from long-term keys
- (B) Data is encrypted twice for additional security
- (C) The VPN connection automatically reconnects after failure
- (D) All traffic is routed through multiple servers for anonymity
- Q4. Which VPN type allows users to access resources through a web browser without installing client software?
- (A) IPsec VPN
- (B) PPTP VPN
- (C) SSL/TLS VPN (Clientless)
- (D) L2TP VPN
- Q5. What is the primary purpose of Dead Peer Detection (DPD) in VPN connections?
- (A) To encrypt data more efficiently
- (B) To detect when a VPN tunnel has failed and initiate reconnection
- (C) To balance traffic across multiple VPN servers
- (D) To authenticate users with multiple factors
- Q6. In a remote access VPN scenario, what is the function of the VPN concentrator?
- (A) To compress data before encryption
- (B) To manage multiple VPN connections and handle authentication, encryption, and tunnel termination
- (C) To convert between different VPN protocols
- (D) To cache frequently accessed resources locally
- Q7. Which statement best describes IPsec transport mode?
- (A) Only the payload is encrypted; original IP headers remain visible
- (B) The entire packet including headers is encrypted and encapsulated in a new IP packet
- (C) No encryption is applied, only authentication
- (D) It is used exclusively for site-to-site VPNs
- Q8. What challenge does NAT typically create for IPsec VPNs, and how is it commonly addressed?
- (A) NAT changes IP addresses which breaks IPsec integrity checks; resolved using NAT Traversal (NAT-T) with UDP encapsulation
- (B) NAT blocks all encrypted traffic; resolved by disabling NAT
- (C) NAT reduces available bandwidth; resolved by using compression
- (D) NAT creates routing loops; resolved by implementing static routes
- Q9. Which encryption algorithm is currently considered most secure for VPN implementations?
- (A) DES
- (B) 3DES
- (C) AES-256
- (D) RC4
- Q10. In the context of VPN security, what does the term "crypto map" refer to in Cisco IOS devices?
- (A) A physical diagram showing encryption points in the network
- (B) A configuration element that defines IPsec parameters including peers, transform sets, and traffic to encrypt
- (C) A graphical interface for managing VPN connections
- (D) A tool for testing encryption strength
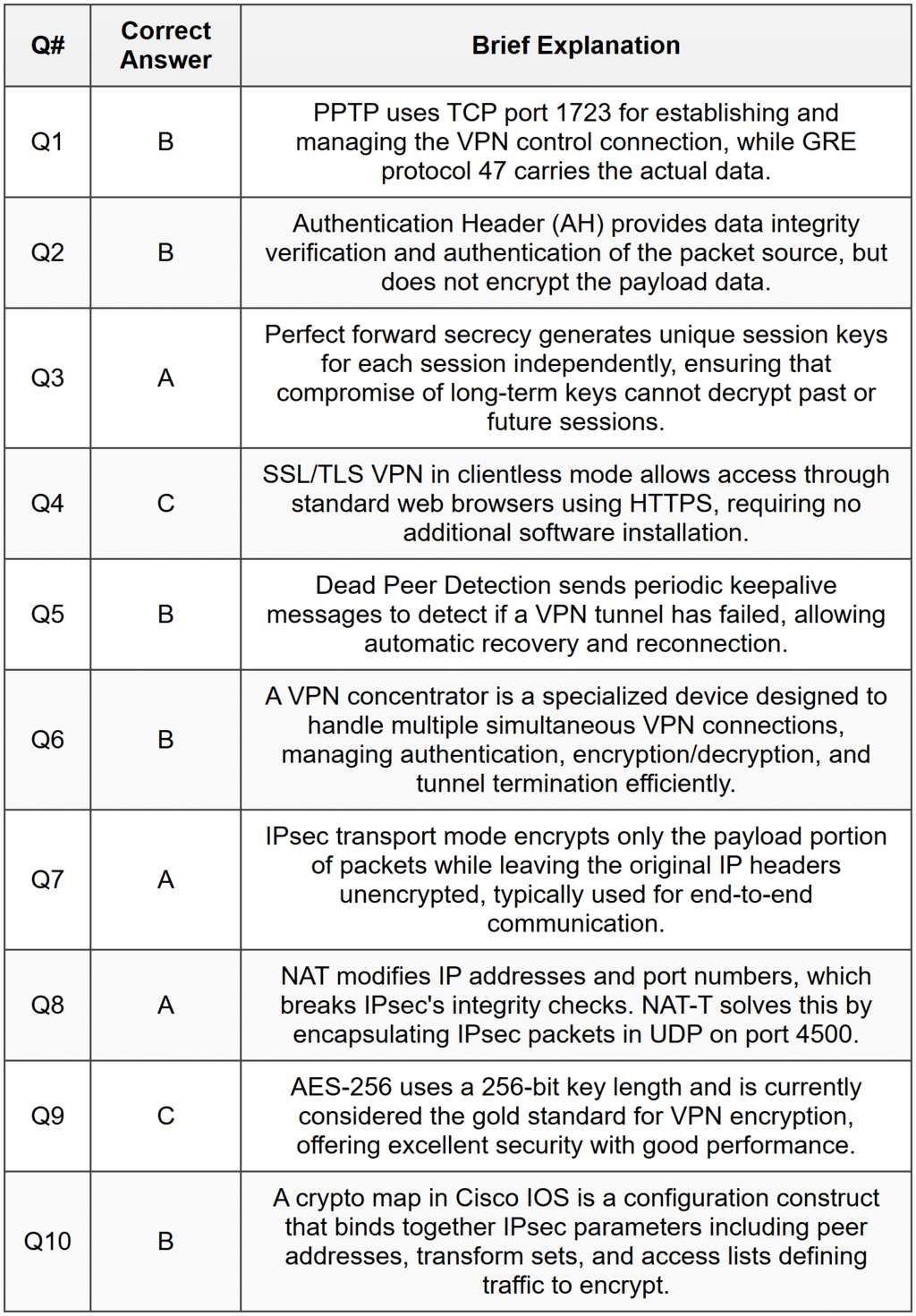
Answer Key
Section 1 - MCQ Answers
Section 2 Answers
Q1. A site-to-site VPN connects entire networks at different locations, creating a permanent encrypted tunnel between network gateways. This is typically used to connect branch offices to headquarters, allowing seamless resource sharing between locations. A remote access VPN allows individual users to connect to a network from remote locations using client software on their devices. This is used when employees work from home or travel and need to access corporate resources securely.
Q2. Split tunneling is a VPN configuration that allows some traffic to go through the encrypted VPN tunnel while other traffic accesses the internet directly. The advantage is improved performance, as users can access internet resources (like streaming or cloud services) without routing through the corporate network, reducing bandwidth consumption and latency. The security concern is that devices simultaneously connected to both the corporate network and the public internet create a potential bridge that could allow threats to bypass corporate security controls.
Q3. IPsec uses two main protocols: Authentication Header (AH) provides data integrity and authentication but no encryption, while Encapsulating Security Payload (ESP) provides encryption, authentication, and integrity. ESP is more commonly used because it offers comprehensive security including confidentiality through encryption, which AH lacks. Modern implementations rarely use AH alone because encryption is essential for protecting sensitive data, and ESP can provide both authentication and encryption in a single protocol.
Q4. IKE (Internet Key Exchange) is responsible for negotiating security parameters and establishing secure channels for IPsec VPNs. During IKE Phase 1, peers authenticate each other and establish a secure, encrypted channel called the IKE Security Association (SA), negotiating encryption and authentication algorithms. In IKE Phase 2, peers use the secure channel established in Phase 1 to negotiate IPsec SAs, which define the encryption and authentication methods for the actual data traffic, as well as the specific traffic to be protected.
Section 3 Answers
Q1. Completed VPN Protocol Comparison Table:
Q2. Network Diagram Description:
Headquarters (HQ):
- Internal subnet: 192.168.1.0/24
- VPN Gateway: HQ-VPN-GW connected to Internet
- Encrypted VPN Tunnel 1: HQ-VPN-GW ↔ BranchA-VPN-GW (IPsec/AES-256)
- Encrypted VPN Tunnel 2: HQ-VPN-GW ↔ BranchB-VPN-GW (IPsec/AES-256)
Branch A:
- Internal subnet: 192.168.2.0/24
- VPN Gateway: BranchA-VPN-GW connected to Internet
- Encrypted VPN Tunnel: BranchA-VPN-GW ↔ HQ-VPN-GW
Branch B:
- Internal subnet: 192.168.3.0/24
- VPN Gateway: BranchB-VPN-GW connected to Internet
- Encrypted VPN Tunnel: BranchB-VPN-GW ↔ HQ-VPN-GW
Packet Path from Branch A user to Branch B server:
1. User at Branch A (192.168.2.100) sends packet to server at Branch B (192.168.3.50)
2. Packet reaches BranchA-VPN-GW, which encrypts it using IPsec
3. Encrypted packet travels through Internet to HQ-VPN-GW
4. HQ-VPN-GW decrypts the packet, examines destination (192.168.3.50)
5. HQ-VPN-GW re-encrypts packet and sends through VPN tunnel to BranchB-VPN-GW
6. BranchB-VPN-GW decrypts packet and forwards to destination server (192.168.3.50)
Note: This hub-and-spoke topology requires traffic between branches to transit through HQ. An alternative full-mesh topology would have a direct tunnel between Branch A and Branch B.
Q3. Component Matching:
Section 4 - MCQ Answers