Video Lectures of Get to know Ethical Hacking (English) for Software Development Exam
Watch free video lectures for Get to know Ethical Hacking (English) covering all chapters/topics as per the latest syllabus in 2026. These concept videos, recorded lectures, and audio notes are designed to help Software Development students understand every topic clearly — anytime, anywhere. Start learning on EduRev.
Get to know Ethical Hacking (English)
| Complete Ethical Hacking Course - Become a Hacker Today - #1 Hacking Terminology 04:29 min |  |
| Complete Ethical Hacking Course #2 - Installing Kali Linux 17:05 min |  |
| Parrot OS 3.5 Review | The Best Kali Linux Alternative 14:21 min |  |
| Nmap Tutorial For Beginners - 1 - What is Nmap? 13:23 min |  |
| Nmap Tutorial For Beginners - 2 - Advanced Scanning 10:19 min |  |
| Katoolin | How To Install Kali Linux Hacking Tools On Any Linux Distro 05:51 min |  |
| Zenmap Tutorial For Beginners 07:48 min |  |
| Nmap Tutorial For Beginners - 3 - Aggressive Scanning 11:23 min |  |
| How To Setup Proxychains In Kali Linux - #1 - Stay Anonymous 07:54 min |  |
| How To Setup Proxychains In Kali Linux - #2 - Change Your IP 10:59 min |  |
| How To Change Mac Address In Kali Linux | Macchanger 10:20 min |  |
| How To Setup And Use anonsurf On Kali Linux | Stay Anonymous 09:56 min |  |
| SQL Injection Tutorial For Beginners - Kali Linux - #1 10:39 min |  |
| SQL Injection Tutorial For Beginners - #2 - sqlmap - Hack Vulnerable Websites 13:00 min |  |
| VPN And DNS For Beginners | Kali Linux 09:53 min |  |
| Tails OS Installation And Review - Access The Deep Web/Dark Net 16:56 min |  |
| Steganography Tutorial - Hide Messages In Images 10:29 min |  |
| BackBox Linux Review 2017 - Is It Any Good? 14:08 min |  |
| The Lazy Script - Kali Linux 2017.1 - Make Hacking Simple! 14:52 min |  |
| The CIA Of Security - Confidentiality; Integrity; Availability 06:30 min |  |
| How To Setup VPN For Free On Kali Linux - Stay Anonymous 16:00 min |  |
| BeeLogger - Kali Linux 2017.1 - How To Create A Windows Keylogger 15:50 min |  |
| Python For Ethical Hacking - #1 - Introduction & Python Modules 07:47 min |  |
| Python For Ethical Hacking -#3 - Importing The Nmap Module 09:03 min |  |
| Netcat Tutorial - The Swiss Army Knife Of Networking - Reverse Shell 17:02 min |  |
| Gaining Access - Web Server Hacking - Metasploitable - #1 15:36 min |  |
| Web Server Hacking - FTP Backdoor Command Execution With Metasploit - #2 10:01 min |  |
| How To Install Kali Linux On VMware - Complete Guide 2018 33:35 min |  |
| Terminator - Kali Linux - Multiple Terminals 04:38 min |  |
| Shodan Search Engine Tutorial - Access Routers;Servers;Webcams + Install CLI 21:42 min |  |
| Metasploit Community Web GUI - Installation And Overview 10:13 min |  |
| Linux Expl0rer - Forensics Toolbox - Installation & Configuration 11:47 min |  |
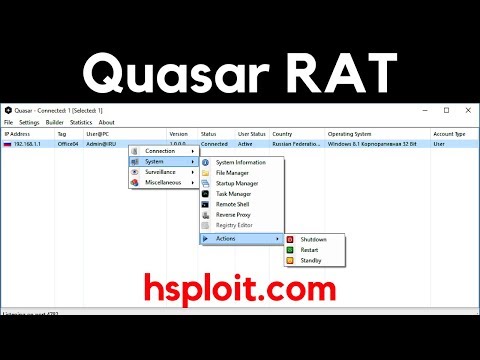
| QuasarRAT - The Best Windows RAT? - Remote Administration Tool for Windows 26:01 min |  |
| Metasploit For Beginners - #1 - The Basics - Modules; Exploits & Payloads 22:59 min |  |
| Metasploit For Beginners - #2 - Understanding Metasploit Modules 19:39 min |  |
| Fsociety Hacking Tools Pack - Mr. Robot Penetration Testing Framework 04:08 min |  |
| Metasploit For Beginners - #3 - Information Gathering - Auxiliary Scanners 12:19 min |  |
| Metasploit For Beginners - #4 - Basic Exploitation 11:48 min |  |
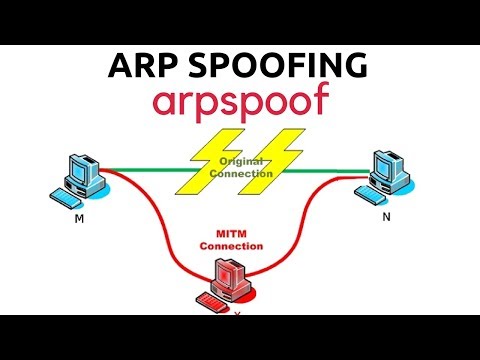
| ARP Spoofing With arpspoof - MITM 10:02 min |  |
| Generating A PHP Backdoor with weevely - Post Exploitation 09:33 min |  |
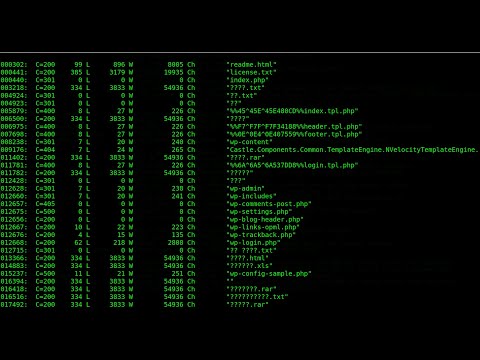
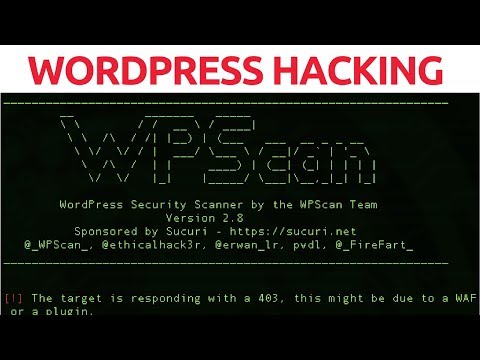
| WordPress Hacking With WPScan 14:21 min |  |
| MITM Attack With Ettercap - ARP Poisoning 08:19 min |  |
| Password Cracking With John The Ripper - RAR/ZIP & Linux Passwords 12:27 min |  |
| How To Detect Rootkits On Kali Linux - chkrootkit & rkhunter 14:35 min |  |
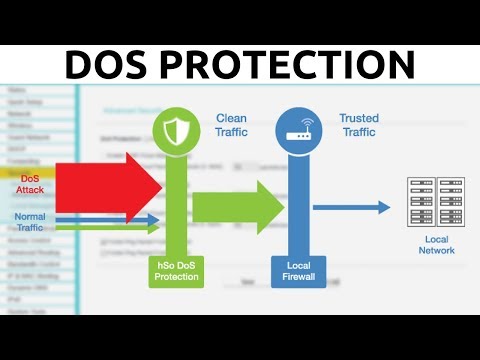
| DoS/DDoS Protection - How To Enable ICMP; UDP & TCP Flood Filtering 03:47 min |  |
| BeEF Browser Exploitation - Client Side Attacks With Kali Linux 19:10 min |  |
| The Complete DNS Guide - How To Change Your DNS + Cloudflare DNS 12:15 min |  |
| Armitage Kali Linux Tutorial - Scanning & Exploitation 14:49 min |  |
| How To Setup A Virtual Penetration Testing Lab 28:54 min |  |
| How To Use A VPN With Proxychains | Maximum Anonymity 07:44 min |  |
| EternalBlue Exploit Tutorial - Doublepulsar With Metasploit (MS17-010) 17:48 min |  |
| The Complete Meterpreter Guide | Privilege Escalation & Clearing Tracks 20:09 min |  |
| Veil-Evasion - How To Generate Undetectable Payloads | Antivirus Bypass 17:21 min |  |
| Network Discovery With netdiscover - Discover Internal IP Addresses 10:15 min |  |
| Android Hacking With zANTI - MITM & Vulnerability Assessment 20:05 min |  |
| PentestBox - Portable Penetration Testing Environment For Windows 18:10 min |  |
| WSL - How To Install xfce4 On Kali Linux | Windows 10 08:49 min |  |
| GDPR Explained - What It Means For You 18:23 min |  |
| Parrot OS 4.0.1 Review - New System Updates & Changes 14:20 min |  |
| Web App Penetration Testing - #8 - SQL Injection With sqlmap 15:35 min |  |
| RouterSploit - Router Exploitation Framework 15:24 min |  |
| Recon-ng - Introduction And Installation 07:46 min |  |
| Recon-ng - Commands; Workspaces And Data Management 13:00 min |  |
| Nipe - How To Fully Anonymize Your System With Tor 07:15 min |  |
| Tortilla - Securely & Anonymously Route Your Traffic Through Tor 16:02 min |  |
| The PenTesters Framework - Install Penetration Testing Tools On Any Distribution 15:20 min |  |
| Generating Rainbow Tables With RainbowCrack 13:08 min |  |
| How To Setup Port Forwarding For Metasploit 19:51 min |  |
| Sphere Browser Review - Anonymous; Secure & Free 19:21 min |  |
| Scapy - Packet Manipulation & Sniffing 22:55 min |  |
| Installing And Configuring OpenVAS 07:39 min |  |
| Vulnerability Analysis With OpenVAS 16:20 min |  |