Video Lectures of Ethical Hacking using Kali Linux (in English) for Software Development Exam
Watch free video lectures for Ethical Hacking using Kali Linux (in English) covering all chapters/topics as per the latest syllabus in 2026. These concept videos, recorded lectures, and audio notes are designed to help Software Development students understand every topic clearly — anytime, anywhere. Start learning on EduRev.
Ethical Hacking using Kali Linux (in English)
| Lesson 1: Introduction to Kali Linux 16:49 min |  |
| Lesson 2 : What is Ethical hacking and penetration testing 08:06 min |  |
| Lesson 4 : Operating Systems 05:59 min |  |
| Lesson 3 : Kali Linux 11:48 min |  |
| Lesson 6 : Installing Operating Systems 09:00 min |  |
| Lesson 8 : Configuring Kali Linux 09:22 min |  |
| Lesson 7 : Installing Vmware Tools 10:23 min |  |
| Lesson 9 : Installing Kali Linux On MacBook 11:18 min |  |
| Lesson 12 : Footprinting Tools 12:24 min |  |
| Lesson 13: Introduction To Google Hacking 08:52 min |  |
| Lesson 16 : Who is Lookup 10:15 min |  |
| Lesson 15 : Google Hacking Processes 06:40 min |  |
| Lesson 17: DNS Footprinting Overview 06:47 min |  |
| Lesson 19 : Determining Operation System 09:43 min |  |
| Lesson 21 : Phishing Attacks Details 06:20 min |  |
| Lesson 20 : Introduction To Phishing Attacks 07:26 min |  |
| Lesson 23 : Introduction To Nmap And Zenmap 10:19 min |  |
| Lesson 22 : Connecting Information Database 12:03 min |  |
| Lesson 24 : Nmap 07:30 min |  |
| Lesson 25 : Zenmap 07:29 min |  |
| Lesson 26 : The Harvester Overview 06:34 min |  |
| Lesson 28 : WHO IS and dnsenum Overview 07:49 min |  |
| Lesson 27 : The Harvester Process and Functions 06:00 min |  |
| Lesson 30 : URLcrazy 06:26 min |  |
| Lesson 29 : DNSenum 07:18 min |  |
| Lesson 32 : DNSrecon 09:22 min |  |
| Lesson 31 : DNSdict 05:46 min |  |
| Lesson 33 : DNSmapping 11:07 min |  |
| Lesson 34 : Introduction To Social Engineering and information Gathering 09:46 min |  |
| Lesson 35 : Types Of Social Engineering 09:57 min |  |
| Lesson 36 : Social Engineering Attacks 07:07 min |  |
| Lesson 37 : Spear Phishing Attacks 11:11 min |  |
| Lesson 38 : Phishing Attack 07:03 min |  |
| Lesson 39 : Phishing Attack Consequences 07:02 min |  |
| Lesson 40 : Mass mailer Attack 09:24 min |  |
| Lesson 41 : Introduction To Computer Malwares 06:43 min |  |
| Lesson 42 : Types Of Computer Malwares 07:54 min |  |
| Lesson 44 : Some Prominent Dangerous Viruses Of all Time 07:54 min |  |
| Lesson 45 : Installing Rootkit Hunter 06:45 min |  |
| Lesson 47 : Backdoor Process and Functions 06:37 min |  |
| Lesson 46 : Backdoor Overview 07:08 min |  |
| Lesson 48 : Backdoor Gaining Access 09:05 min |  |
| Lesson 49: Backdoor Maintaining Access 07:16 min |  |
| Lesson 50 : Backdoor Maitaining Access Continued 05:25 min |  |
| Lesson 51 : Introducing Command Prompt Backdoor 08:01 min |  |
| Lesson 53 : Meterpreter Backdoor 10:56 min |  |
| Lesson 52 : Command Prompt Backdoor Details 07:10 min |  |
| Lesson 54 : I am Root 13:52 min |  |
| Lesson 55 : Forensic Escaping 07:00 min |  |
| Lesson 56 : Hacking Win7 SAM database 11:34 min |  |
| Lesson 57 : Jack The Ripper 11:40 min |  |
| Lesson 58 : Meterpreter Commands 12:40 min |  |
| Lesson 59 : PDF Embedded Trojan Horse 11:21 min |  |
| Lesson 60 : Introduction To Java Applet Attack Method 06:38 min |  |
| Lesson 62 : MITM Attack 09:32 min |  |
| Lesson 61 : Java Applet Attack Method Continues 08:09 min |  |
| Lesson 65 : DNS Spoofing 10:00 min |  |
| Lesson 67 : DHCP Spoofing 12:27 min |  |
| Lesson 68 : Port Stealing 11:23 min |  |
| Lesson 69 : Introduction To ICMP redirection 10:17 min |  |
| Lesson 70 : ICMP redirection Visual Chart 10:16 min |  |
| Lesson 71 : IMPC redirection Process and Functions 09:54 min |  |
| Lesson 74 : Driftnet 09:53 min |  |
| Lesson 75 : Introducing EvilGrade 09:28 min |  |
| Lesson 76: EvillGrade Continues 08:47 min |  |
| Lesson 78 : DoS VS DDoS 06:31 min |  |
| Lesson 77 : Introduction To Dos 09:33 min |  |
| Lesson 82 : DDosing Windows 7 Methods 09:48 min |  |
| Lesson 83 : Introduction To Hacking 06:03 min |  |
| Lesson 86 : Introduction To Password Cracking 11:35 min |  |
| Lesson 87 : Password Cracking Strategy 11:50 min |  |
| Lesson 88 : Password Cracking Strategy Shown In Practicals 09:53 min |  |
| Lesson 89 : Windows Password Cracking Overview 08:06 min |  |
| Lesson 90 : Nuts And Bolts Of Windows Password Cracking Strategy 07:20 min |  |
| Lesson 93 : Generating Wordlist Overview 07:34 min |  |
| Lesson 94 : Generating Wordlist Process and Functions 10:19 min |  |
| Lesson 97 : WPA Continues 10:35 min |  |
| Lesson 99 : Wireless Cracking Overview 08:53 min |  |
| Lesson 101 : Mesterpreter Overview 14:15 min |  |
| Lesson 102 : Activating Payloads 09:07 min |  |
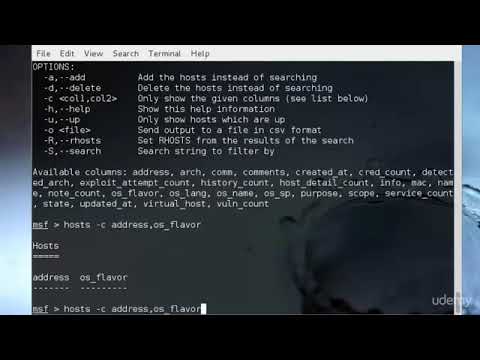
| Lesson 104 : MsDconsole Commands 11:55 min |  |
| Lesson 105 : Exploits 11:40 min |  |
| Lesson 107 : Generating Payloads 10:51 min |  |
| Lesson 106 : Payloads 09:55 min |  |
| Lesson 108 : Generating Payloads Continues 11:42 min |  |
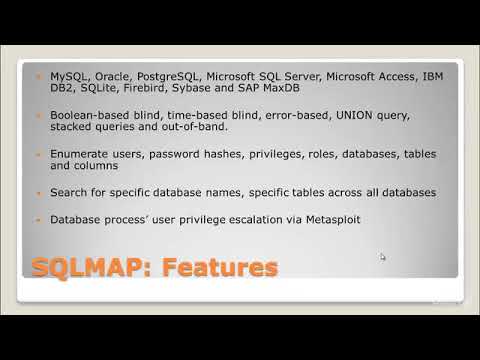
| Lesson 110 : SQL Injection To Google Dorks 11:28 min |  |
| Lesson 112 : Gathering Password And Cracking The Hash 09:13 min |  |
| Lesson 111 : SQL Mapping Via Kali Linux 09:57 min |  |
| Lesson 114 : Basic Concepts On Cryptography 07:13 min |  |
| Lesson 113 : Introduction To Cryptography 05:25 min |  |
| Lesson 117 : Pros and Cons Of Cryptography 08:12 min |  |
| Lesson 116 : Birthday Theorem & Digital Signature 09:37 min |  |
| Lesson 119: Exporting Databases 07:18 min |  |
| Lesson 118: Importing Databases 09:06 min |  |
| Lesson 120: Exporting Databases Shown in Practicals 05:41 min |  |