Framing
Introduction
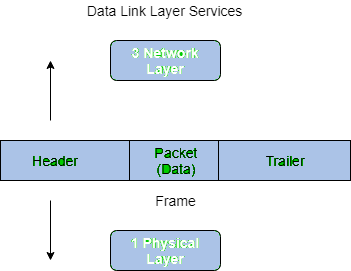
Frames are the basic units of digital transmission used at the data link layer of the network stack. A frame is a sequence of bits (or bytes) that represents a single logical block of data transmitted from one device to another over a point-to-point or multiaccess link. Framing provides boundaries so that the receiver can identify the start and end of each block and recover the original message reliably.
- Frames provide a way for a sender to transmit a set of bits that are meaningful to the receiver. Common data link technologies such as Ethernet, Token Ring and Frame Relay use specific frame formats.
- Frames typically include a header containing control information (for example, addresses and length/type), a payload (data), and trailer bytes such as an error-check sequence (for example, FCS implemented with CRC) that enable the receiver to detect transmission errors.
- Framing is essential because a raw wire or channel carries a continuous stream of bits; without framing the receiver cannot determine where one message ends and the next begins.
Why framing is needed (functions of data link layer)
- Boundary recognition: mark the start and end of each frame so that receivers extract correct blocks of data.
- Addressing: include sender and receiver addresses so frames can be delivered to the correct station on multiaccess links.
- Error detection: include checks (for example FCS/CRC) so corrupted frames are detected and dealt with (dropped or retransmitted by higher-layer protocols).
- Flow and access control: support for managing when stations transmit on a shared medium and controlling the data transfer rate between sender and receiver.
Problems in framing
- Detecting the start of a frame: the receiver must be able to detect the first bit or byte of a frame reliably. Many protocols use a special pattern called a start-of-frame delimiter (SFD) or a start flag (for example a predefined byte or bit pattern) to indicate the beginning of a frame.
- How a station detects a frame: stations monitor the link looking for the SFD or start flag. A sequential or pattern-detection circuit recognises the delimiter pattern. Once the SFD is found, the station reads the subsequent fields (addresses, length/type, payload) and checks the destination address to accept or discard the frame.
- Detecting end of frame: the receiver must know when to stop reading the current frame and where the next frame begins. Techniques include fixed-length frames, length fields, and end delimiters (flags).
- Data transparency (delimiter occurrence in data): if the chosen start/end pattern occurs within payload data, the receiver might mistake it for a boundary. Framing protocols must make data transparent by using techniques such as byte/character stuffing or bit stuffing.
Common frame fields (typical elements of a frame)
- Preamble: a pattern used for bit synchronisation between sender and receiver.
- Start-of-frame delimiter (SFD) / Flag: a special bit/byte sequence that indicates where the frame starts.
- Destination address: identifies the intended recipient.
- Source address: identifies the sender.
- Length or Type field: indicates payload length or protocol type (used in different framing schemes).
- Payload (data): the actual information carried by the frame.
- Frame Check Sequence (FCS): error-detection code, commonly a CRC, used to detect corrupted frames.
- Padding: additional bytes added when payload is shorter than the minimum required frame size (used in some protocols such as Ethernet).
Types of framing
There are two broad categories of framing:
- Fixed-size framing - each frame has a fixed, predefined size so the frame boundaries are implicit.
- Variable-size framing - frames have variable payload lengths so some explicit method is needed to mark frame boundaries (for example, a length field or an end delimiter).
Fixed-size framing
When every frame has the same length, the receiver knows where a frame ends by counting the fixed number of bits or bytes. This simplifies boundary detection but has drawbacks.
- Drawback: internal fragmentation occurs when the data to be sent is smaller than the fixed frame payload; unused space within the frame is wasted.
- Solution: padding bytes are used to fill to the fixed length; the receiver discards padding after extracting the real data.
Variable-size framing
Variable-length frames require an explicit method to determine where each frame ends. Two common techniques are:
Length field
A field in the header gives the number of bytes (or bits) in the payload (or in the whole frame). The receiver reads the length field and then reads exactly that many bytes to obtain the payload. This is the method used by IEEE 802.3 (Ethernet), which can carry a length or a type field depending on the variant.
- Advantage: straightforward and fast when the length field is reliable.
- Problem: if the length field gets corrupted during transmission, the receiver will read the wrong amount of data and lose frame alignment. Error-detection fields such as the FCS/CRC help detect such corruption, and higher-layer protocols handle recovery.
End delimiter (end flag)
A special pattern marks the end (and possibly the start) of every frame. The receiver recognises this pattern and uses it to determine frame boundaries. Token Ring and many bit-oriented protocols use flag patterns as delimiters.
- Problem: the end-delimiter pattern may appear as a bit/byte sequence inside payload data. To avoid false boundary detection, framing protocols make the data transparent by transforming the payload so that delimiter patterns never appear inside the transmitted frame. Two common transparency techniques are character (byte) stuffing and bit stuffing.
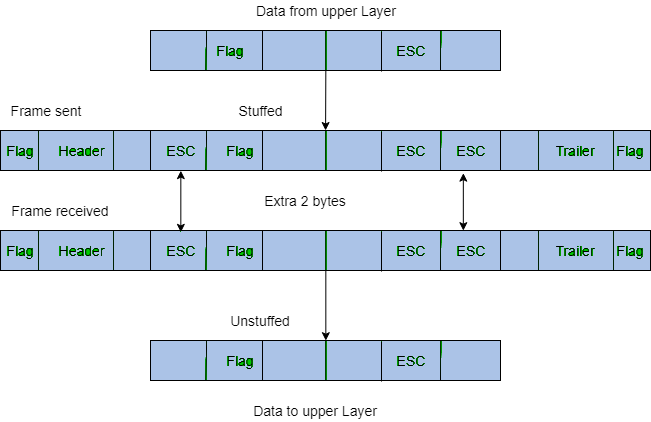
Character (byte) stuffing
Used when the link is byte-oriented (frames are sequences of bytes). A special escape byte (often called ESC) is defined. Whenever the payload contains the escape byte or the delimiter byte, the sender inserts an escape byte before it (this is called stuffing). The receiver removes escape bytes during de-stuffing.
- Example of a scheme: if the end delimiter is the byte "$" and ESC is "\" then every occurrence of "$" in the payload is transmitted as "\$". If the ESC itself appears in data it is transmitted as "\\" so the receiver can distinguish data ESC from ESC used for escaping.
- Advantage: simple when the data is organised in bytes.
- Disadvantage: adds extra bytes and processing; can be costly in some contexts and is considered obsolete for bit-oriented links.
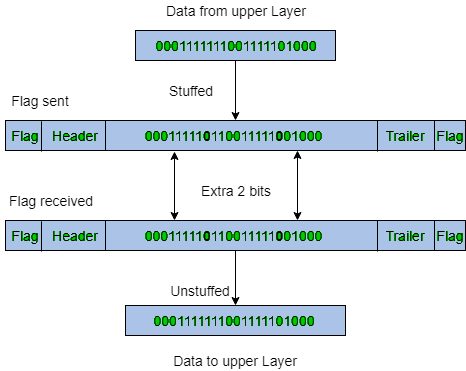
Bit stuffing
Used when the link is bit-oriented. A special bit pattern (flag) is used to delimit frames. To ensure that the flag pattern never occurs in the payload, the sender inserts (stuffs) a bit after a certain number of consecutive bits of the same value in the payload.
A common algorithm used in bit-oriented protocols (for example, HDLC) is:
- Define the frame flag (for example, HDLC uses 01111110).
- When transmitting payload bits, after every sequence of five consecutive 1 bits in the transmitted data, the sender inserts a 0 bit.
- The receiver monitors incoming bits; when it finds five consecutive 1 bits followed by a 0 it removes that 0 (de-stuffing) and recovers the original data. When the receiver detects five consecutive 1 bits followed by a 1 it recognises this as the flag boundary.
Advantages: provides transparency at the bit level and is efficient for bit-oriented channels. Disadvantage: small overhead when long runs of ones appear and the need for bit-level processing.
Practical notes and examples
Protocol designers choose a framing technique based on the link characteristics and the required efficiency, error control and simplicity. Ethernet (IEEE 802.3) uses a length/type field and minimum/maximum frame sizes with padding rules to handle short payloads. Bit-oriented protocols such as HDLC and Token Ring use flag bytes and bit stuffing to provide transparent framing.
Examples
- If Data → 011100011110 and ED → 0111 then, find data after bit stuffing?
→ 011010001101100 - If Data → 110001001 and ED → 1000 then, find data after bit stuffing?
→ 11001010011
Summary
Framing is a core function of the data link layer that converts a raw stream of bits into discrete, recoverable blocks called frames. Framing methods include fixed-size and variable-size schemes. Variable-size frames use length fields or end delimiters; the latter requires data transparency techniques such as byte stuffing or bit stuffing to avoid accidental delimiter patterns appearing inside payloads. Choice of framing method depends on link type, efficiency and complexity constraints. Error-detection fields such as FCS/CRC complement framing to ensure reliable detection of corrupted frames.
 | Explore Courses for Computer Science Engineering (CSE) exam |  |
 | Get EduRev Notes directly in your Google search |  |



