Information Technology Act, 2000 | Law Optional Notes for UPSC PDF Download
Introduction
Imagine one morning you wake up to find that all your personal data stored across various applications like your phone's gallery, Facebook, Instagram, and WhatsApp has been compromised by a hacker. As you check your laptop, you discover that it too has been infiltrated. Faced with this situation, what should you do? Do you contemplate suing these social media platforms for failing to safeguard your data, or do you embark on a quest to find the hacker responsible?
This is where the Information Technology Act of 2000 becomes relevant. This legislation outlines a range of offenses related to data breaches and individual privacy violations, prescribing penalties and punishments for these transgressions. It also addresses the role of intermediaries and regulates the authority of social media platforms. The rapid growth of technology and e-commerce has witnessed a significant surge in cybercrimes and violations concerning data and confidential information. Even data associated with the nation's security and integrity has faced threats. Consequently, the government felt the need to oversee the operations of social media and the data they host. This article delves into the objectives and characteristics of the Act, shedding light on various offenses and their corresponding penalties as outlined in the legislation.
Background of Information Technology Act, 2000
In 1996, the United Nations Commission on International Trade Law introduced a model law pertaining to e-commerce and the complexities of the digital realm. This model law imposed an obligation on each country to establish its own legal framework concerning e-commerce and cybercrimes. With the primary aim of safeguarding the data of both its citizens and the government, India enacted the Information Technology Act in the year 2000, thereby becoming the 12th nation worldwide to implement legislation addressing cybercrimes. Commonly known as the IT Act, this legislation provides the necessary legal structure for protecting data associated with e-commerce and digital signatures. Subsequently, the Act underwent amendments in 2008 and 2018 to adapt to the evolving requirements of society. Furthermore, it outlines the authority and limitations of intermediaries.
Schedule of Information Technology Act, 2000
The Information Technology Act of 2000 is structured into 13 chapters, comprising 90 sections and including 2 schedules. Here is an overview of the chapters within the Act:
- Chapter 1 addresses the Act's scope and provides definitions for key terms used throughout the Act.
- Chapter 2 focuses on digital and electronic signatures.
- Electronic governance and electronic records are the subjects of Chapters 3 and 4, respectively.
- Chapter 5 is dedicated to the security of electronic records, while Chapter 6 concerns the regulation of certifying authorities.
- Chapter 7 outlines the prerequisites for issuing an electronic signature certificate.
- Chapter 8 delineates the responsibilities of subscribers, and Chapter 9 details various penalties.
- Chapter 10 contains provisions related to the Appellate Tribunal.
- Chapter 11 defines offenses pertaining to data breaches and stipulates the associated penalties.
- Chapter 12 establishes circumstances under which intermediaries are not held liable for offenses or breaches of data privacy.
- The final chapter, Chapter 13, encompasses miscellaneous provisions.
The Act also includes 2 schedules:
- Schedule 1 enumerates documents and data to which the Act does not apply.
- Schedule 2 addresses electronic signatures and methods of authentication.
Applicability of Information Technology Act, 2000
The Information Technology Act of 2000 has a broad applicability. As per Section 1, it extends to the entire territory of India, encompassing Jammu and Kashmir. Moreover, the Act holds extra-territorial jurisdiction, which means it can apply to individuals who commit offenses outside of India. If the source of the offense, such as a computer or a similar device, is located in India, the Act can be invoked to penalize the perpetrator, regardless of their nationality.
However, there are exceptions outlined in the Act. It does not apply to documents detailed in Schedule 1, which includes:
- Negotiable instruments, excluding cheques, as specified in Section 13 of the Negotiable Instruments Act, 1881.
- Powers of attorney as per Section 1A of the Powers of Attorney Act, 1882.
- Trusts in accordance with Section 3 of the Indian Trusts Act, 1882.
- Wills and testamentary dispositions under the Indian Succession Act, 1925.
- Contracts or sale deeds involving immovable property.
Objectives of Information Technology Act, 2000
The Information Technology Act of 2000 was established to address the complexities of e-commerce, digital signatures, and digital transactions, with the following key objectives:
- Safeguarding electronic transactions: The Act aims to provide protection for all activities conducted through electronic means.
- Legal recognition for digital communication: In an era of reduced paperwork, it offers legal backing to electronic communication and data exchange.
- Protection of digital signatures: It ensures the security and legitimacy of digital signatures used for various legal purposes.
- Regulation of intermediaries: The Act exercises control over intermediaries by defining their powers and responsibilities.
- Defining and preventing offenses related to data privacy: The Act outlines various offenses to safeguard citizens' data privacy.
- Regulation and protection of sensitive electronic data: It provides a framework to oversee and safeguard critical data held by social media and other electronic intermediaries.
- Recognition of electronically maintained financial records: The Act acknowledges electronic accounting practices as regulated by the Reserve Bank of India Act, 1934.
Features of Information Technology Act, 2000
The Information Technology Act of 2000 exhibits several notable features, including:
- Model Law Foundation: The Act is built upon the Model Law on e-commerce as adopted by UNCITRAL.
- Extraterritorial Jurisdiction: It possesses the authority to apply beyond national borders, making it applicable to offenses committed outside the country, provided the source of the offense is within India.
- Definitions: The Act defines essential terms such as cyber cafes, computer systems, digital signatures, electronic records, data, asymmetric cryptosystems, and more in Section 2(1).
- Validation of Electronic Contracts: It safeguards transactions and contracts conducted through electronic means, declaring their validity (Section 10A).
- Recognition of Digital Signatures: The Act acknowledges and provides authentication methods for digital signatures.
- Controller's Appointment and Powers: It includes provisions related to the appointment of the Controller and outlines the Controller's authority.
- Recognition of Foreign Certifying Authorities: The Act allows for the recognition of foreign certifying authorities (Section 19).
- Penalties for System Damage: It defines penalties in cases where a computer system is damaged by someone other than the owner.
- Establishment of an Appellate Tribunal: The Act establishes an Appellate Tribunal to hear appeals from the decisions made by the Controller or other Adjudicating officers.
- Further Appeals to the High Court: Appeals from the tribunal can be taken to the High Court.
- Offenses Related to Data: Various offenses concerning data are described, along with their corresponding punishments.
- Intermediaries' Limited Liability: It provides circumstances where intermediaries are not held liable even in cases of data privacy breaches.
- Cyber Regulation Advisory Committee: The Act establishes a committee tasked with advising the Central Government on e-commerce and digital signature matters.
Overview of Information Technology Act, 2000
The Act deals with e-commerce and all the transactions done through it. It gives provisions for the validity and recognition of electronic records along with a license that is necessary to issue any digital or electronic signatures. The article further gives an overview of the Act.
Electronic Records and Signatures
The Act provides definitions related to electronic records and signatures, categorizing electronic records as any data, image, record, or file transmitted through electronic means. Digital signatures used for authenticating electronic records are referred to as electronic signatures, and their validity involves asymmetric cryptosystems and hash functions, as specified in Section 3.
Conditions for Reliable Electronic Signatures (Section 3A)
To be considered reliable, electronic signatures must meet several conditions:
- They should be linked to the signatory or authenticator.
- The signatory must maintain control over the signatures during the signing process.
- Any alterations to such signatures must be detectable, both in the signature itself and in the authenticated information.
- The Central Government may specify additional conditions.
The Act allows the government to establish rules regarding electronic signatures, as outlined in Section 10. It addresses the attribution of electronic records (Section 11), signifying that an electronic record is attributed if sent by the originator or another party on their behalf. When the originator hasn't specified a particular acknowledgment method, the recipient must acknowledge the receipt of the electronic record in any manner (Section 12).
Determination of Time of Receipt (Section 13)
The time of receipt of an electronic record is determined based on various scenarios:
- When the recipient designates a specific computer resource, receipt occurs upon the record's entry into that resource.
- When the record is dispatched to an external computer system, receipt takes place when the addressee retrieves the record.
- If the addressee hasn't specified a computer resource, the receipt occurs when the record enters any computer source owned by the addressee.
Certifying Authorities
Appointment of Controller (Section 17)
Section 17 outlines the appointment of the Controller, Deputy Controllers, Assistant Controllers, and other staff members of certifying authorities. The Controller holds authority over Deputy Controllers and Assistant Controllers and prescribes their roles. The Central Government determines the Controller's qualifications, experience, and terms of service, including the location of the Controller's head office.
Functions of the Controller (Section 18)
The Controller of certifying authorities performs several functions, including:
- Supervising certifying authorities' activities.
- Certifying public keys.
- Establishing rules and standards for certifying authorities.
- Defining qualifications and experience prerequisites for authority employees.
- Specifying procedures for maintaining authority accounts.
- Determining terms and conditions for appointing auditors.
- Overseeing authority's operations and transactions.
- Facilitating the establishment of an electronic system.
- Maintaining authority information and defining officer duties.
- Resolving conflicts between authorities and subscribers.
- Requiring official documents and information issued by authorities to bear the Controller's office seal.
License for Electronic Signatures (Sections 21 to 24)
To issue an electronic signature, one must obtain a license certificate. Section 21 allows individuals to apply for a license by submitting required documents to the Controller, who decides to accept or reject the application. The license's duration and terms are set by the Central Government.
Applicants must meet specific requirements outlined in Section 22:
- Certificate of practice statement.
- Identity proof.
- Payment of a fee (Rs. 25,000).
- Any other documents specified by the Central Government.
The license is renewable if an application, along with a renewal fee (Rs. 25,000), is submitted within 45 days of its expiration (Section 23).
Section 24 lists grounds for license suspension, such as providing false information, non-compliance with license terms, or failure to adhere to Act provisions. However, authorities must provide a reasonable opportunity for the applicant to be heard before suspending a license. The Controller must publish the suspension notice in their records.
Powers of Certifying Authorities
Certifying authorities have various powers and responsibilities:
- Use intrusion-free hardware (Section 30).
- Implement security procedures to protect electronic signature privacy.
- Publish information regarding their practices, electronic certificates, and their status.
- Issue electronic certificates (Section 35).
- Issue digital signature certificates and verify the following: the subscriber's ownership of both a private and public key, the key's ability to create and verify a digital signature, and the accuracy of the subscriber's information.
- Suspend digital signature certificates for up to 15 days (Section 37).
- Revoke certificates based on specific grounds, such as the subscriber's request, death, or the winding up of a company (Section 38).
Circumstances Where Intermediaries Are Not Held Liable:
Section 2(1)(w) of the Act defines an "intermediary" as an entity that receives, transmits, or stores data or information on behalf of others, providing services like telecommunications, search engines, internet services, online payments, etc. Typically, intermediaries are held liable when data stored by them is misused, but the Act specifies instances where they are not held liable under Section 79.
These include:
- Intermediaries will not be held liable for third-party information or communication.
- If the sole function of the intermediary was to provide access to a communication system without further involvement, they are not liable.
- When the intermediary does not initiate transmissions, select the receiver, or modify information in any transmission, they cannot be held liable.
- Intermediaries can avoid liability by performing their duties with care and due diligence.
However, the section outlines exemptions to these rules where intermediaries cannot be shielded from liability:
- If the intermediary is involved in any unlawful act by abetting, inducing, or through threats or promises.
- If the intermediary has not removed data or disabled access used for unlawful activities as notified by the Central Government.
Penalties under Information Technology Act, 2000:
The Act specifies penalties and compensation in several cases, including:
- Penalty for Damaging a Computer System (Section 43): If a person other than the owner damages a computer system, they are liable to pay compensation for all damages. Other reasons for penalties and compensation include downloading or copying stored information, introducing viruses, system disruption, denying access, tampering or manipulation, destruction, deletion, or alteration of stored information, and stealing information.
- Compensation in the Case of Failure to Protect Data (Section 43A): If a corporation or company fails to protect data stored in its computer system, it is liable to pay compensation.
- Failure to Furnish Required Information (Section 44): Individuals failing to provide requested information, documents, or maintain books of accounts face penalties. Penalties range from Rs. 50,000 to Rs. 1 lakh for reports and documents, and Rs. 5,000 for books of accounts or records.
- Residuary Penalty: If a person contravenes any Act provision for which no specified penalty or compensation exists, they will be liable to pay a penalty or compensation of Rs. 25,000.
Appellate tribunal
According to Section 48 of the Act, the Telecom dispute settlement and appellate tribunal under Section 14 of the Telecom Regulatory Authority of India Act, 1997 shall act as the appellate tribunal under the Information Technology Act, 2000. This amendment was made after the commencement of the Finance Act of 2017.
All the appeals from the orders of the controller or adjudicating officer will lie to the tribunal, but if the order is decided with the consent of the parties, then there will be no appeal. The tribunal will dispose of the appeal as soon as possible but in not more than 6 months from the date of such appeal. (Section 57)
According to Section 62 of the Act, any person if not satisfied with the order or decision of the tribunal may appeal to the High Court within 60 days of such order.
Powers
According to Section 58 of the Act, the tribunal is not bound to follow any provisions of the Code of Civil Procedure, 1908 and must give decisions on the basis of natural justice. However, it has the same powers as given to a civil court under the Code. These are:
- Summon any person and procure his attendance.
- Examine any person on oath.
- Ask to discover or produce documents.
- Receive evidence on affidavits.
- Examination of witnesses.
- Review decisions.
- Dismissal of any application.
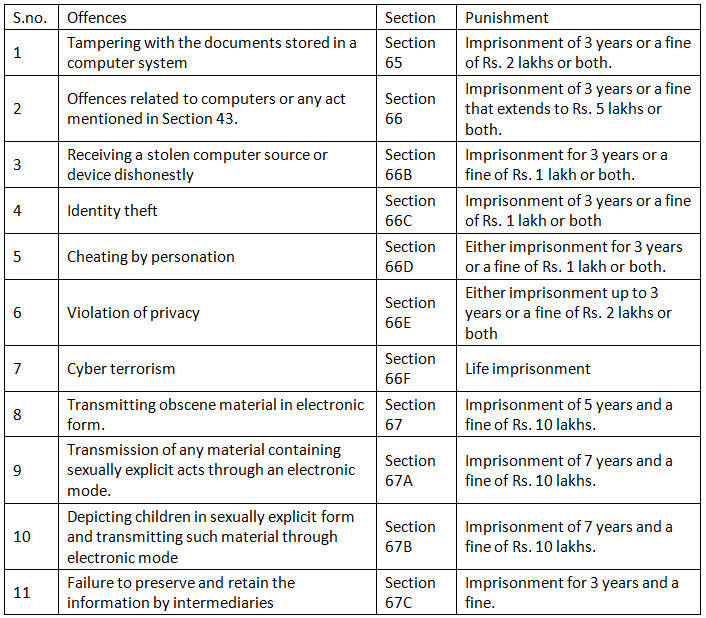
Offences and their punishments under Information Technology Act, 2000
Amendments to Information Technology Act, 2000
With the advancement of time and technology, it was necessary to bring some changes to the Act to meet the needs of society, and so it was amended.
Amendment of 2008
The amendment in 2008 brought changes to Section 66A of the Act. This was the most controversial section as it provided the punishment for sending any offensive messages through electronic mode. Any message or information that created hatred or hampered the integrity and security of the country was prohibited. However, it had not defined the word ‘offensive’ and what constitutes such messages, because of which many people were arrested on this ground. This section was further struck down by the Supreme Court in the case of Shreya Singhal v. Union of India (2015).
Another amendment was made in Section 69A of the Act, which empowered the government to block internet sites for national security and integrity. The authorities or intermediaries could monitor or decrypt the personal information stored with them.
The 2015 Amendment Bill
The bill was initiated to make amendments to the Act for the protection of fundamental rights guaranteed by the Constitution of the country to its citizens. The bill made an attempt to make changes to Section 66A, which provides the punishment for sending offensive messages through electronic means. The section did not define what amounts to offensive messages and what acts would constitute the offence. It was further struck down by the Supreme Court in the case of Shreya Singhal declaring it as violative of Article 19.
Information Technology Intermediaries Guidelines (Amendment) Rules, 2018
The government in 2018 issued some guidelines for the intermediaries in order to make them accountable and regulate their activities. Some of these are:
- The intermediaries were required to publish and amend their privacy policies so that citizens could be protected from unethical activities like pornography, objectionable messages and images, messages spreading hatred, etc.
- They must provide the information to the government as and when it is sought within 72 hours for national security.
- It is mandatory for every intermediary to appoint a ‘nodal person of contact’ for 24×7 service.
- They must have technologies that could help in reducing unlawful activities done online.
- The rules also break end-to-end encryption if needed to determine the origin of harmful messages.
Information Technology (Intermediaries Guidelines and Digital Media Ethics Code) Rules 2021
The government of India in 2021 drafted certain rules to be followed by the intermediaries. The rules made it mandatory for intermediaries to work with due diligence and appoint a grievance officer. They were also required to form a Grievance Appellate Tribunal. All complaints from users must be acknowledged within 24 hours and resolved within 15 days. It also provides a “Code of Ethics” for the people publishing news and current affairs, which makes it controversial. Many believe that the rules curtail freedom of speech and expression and freedom of the press.
The intermediaries were also required to share the information and details of a suspicious user with the government if there was any threat to the security and integrity of the country. As a result of this, writ petitions were filed in various high courts against the rules. Recently, the Bombay High Court stayed in the case of Agij Promotion of Nineteenonea Media Pvt. Ltd. vs. Union of India (2021) and Nikhil Mangesg Wagle vs. Union of India (2021) the two provisions of the rules related to the Code of Ethics for digital media and publishers.
Landmark judgments on Information Technology Act, 2000
Shreya Singhal v. Union of India (2015)
Facts
In this case, 2 girls were arrested for posting comments online on the issue of shutdown in Mumbai after the death of a political leader of Shiv Sena. They were charged under Section 66A for posting the offensive comments in electronic form. As a result, the constitutional validity of the Section was challenged in the Supreme Court stating that it infringes upon Article 19 of the Constitution.
Issue
Whether Section 66A is constitutionally valid or not?
Judgment
The Court, in this case, observed that the language of the Section is ambiguous and vague, which violates the freedom of speech and expression of the citizens. It then struck down the entire Section on the ground that it was violative of Article 19 of the Constitution. It opined that the Section empowered police officers to arrest any person whom they think has posted or messaged anything offensive. Since the word ‘offensive’ was not defined anywhere in the Act, they interpreted it differently in each case. This amounted to an abuse of power by the police and a threat to peace and harmony.
M/S Gujarat Petrosynthese Ltd and Rajendra Prasad Yadav v. Union of India (2014)
Facts
In this case, the petitioners demanded the appointment of a chairperson to the Cyber Appellate Tribunal so that cases can be disposed of quickly and someone can keep a check on the workings of CAT. The respondents submitted that a chairperson would be appointed soon.
Issue
Appointment of the chairperson of CAT.
Judgment
The Court ordered the appointment of the chairperson and must see this as a matter of urgency and take into account Section 53 of the Act.
Christian Louboutin SAS v. Nakul Bajaj and Ors (2018)
Facts
In this case, a suit was filed by a shoe company to seek an order of injunction against the defendants for using its trademarks and logo.
Issue
Whether the protection of “safe harbour” under Section 79 of the Act be applied in this case?
Judgment
The Court in this case observed that the defendant was not an intermediary as their website was a platform for the supply of various products. It used third-party information and promoted vendors in order to attract consumers for them. The Court held that e-commerce platforms are different from the intermediaries and the rights granted to them in Section 79 of the Act. It ordered the intermediaries to work with due diligence and not infringe the rights of the trademark owner. They must take steps to recognise the authenticity and genuineness of the products while dealing with any merchant or dealer.
The Court added that if the intermediaries act negligently regarding IPR and indulge in any sort of abetment or incitement of unlawful or illegal activity, they will be exempted from the protection of safe harbour under Section 79 of the Act. Any active participation in e-commerce would also lead to the same. It also referred to the intermediaries guidelines, which state that no intermediary must violate any intellectual property rights of anyone while displaying any content on its website.
[Intext Question]
Loopholes in Information Technology Act, 2000
The Act provides various provisions related to digital signatures and electronic records, along with the liability of intermediaries, but fails in various other aspects. These are:
No provision for breach of data
The provisions of the Act only talk about gathering the information and data of the citizens and its dissemination. It does not provide any remedy for the breach and leak of data, nor does it mention the responsibility or accountability of anyone if it is breached by any entity or government organization. It only provides for a penalty if an individual or intermediary does not cooperate with the government in surveillance.
No address to privacy issues
The Act failed in addressing the privacy issues of an individual. Any intermediary could store any sensitive personal data of an individual and give it to the government for surveillance. This amounts to a violation of the privacy of an individual. This concern has been neglected by the makers.
Simple punishments
Though the Act describes certain offences committed through electronic means, the punishments given therein are much simpler. To reduce such crimes, punishments must be rigorous.
Lack of trained officers
With the help of money and power, one can easily escape liability. At times, these cases go unreported because of a social stigma that police will not address such complaints. A report shows that police officers must be trained to handle cybercrimes and have expertise in technology so that they can quickly investigate a case and refer it for speedy disposal.
No regulation over Cyber Crimes
With the advancement of technology, cyber crimes are increasing at a greater pace. The offences described in the Act are limited, while on the other hand, various types of cyber crimes are already prevailing, which if not addressed properly within time, may create a menace. These crimes do not affect any human body directly but can do so indirectly by misusing the sensitive data of any person. Thus, the need of the hour is to regulate such crimes. This is where the Act lacks.
Conclusion
The Act is a step toward protecting the data and sensitive information stored with the intermediaries online. It gives various provisions which benefit the citizens and protect their data from being misused or lost. However, with the advancement of e-commerce and online transactions, it is necessary to deal with problems like internet speed and security, transactions that are struck, the safety of passwords, cookies, etc. Cyber crimes are increasing at a great pace, and there is a need to have a mechanism to detect and control them.
|
44 videos|393 docs
|
FAQs on Information Technology Act, 2000 - Law Optional Notes for UPSC
| 1. What is the main objective of the Information Technology Act, 2000? |  |
| 2. What are Certifying Authorities under the Information Technology Act, 2000? |  |
| 3. What are the offences and their punishments under the Information Technology Act, 2000? |  |
| 4. What is the role of the Appellate Tribunal under the Information Technology Act, 2000? |  |
| 5. What are the key amendments made to the Information Technology Act, 2000? |  |
















