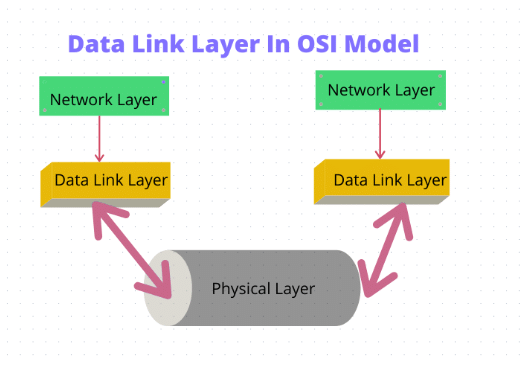
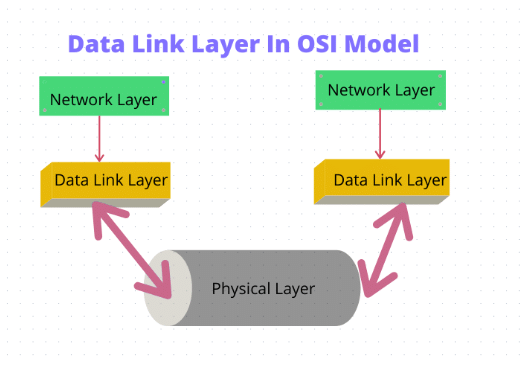
The Data Link Layer, the second layer from the bottom in the Open System Interconnection (OSI) model, is responsible for reliable node-to-node data transfer within a local network. It bridges the Physical Layer, which handles raw bit transmission, and the Network Layer, which manages packet routing. This layer is complex, as it hides hardware complexities from upper layers and ensures error-free communication over potentially unreliable physical media.
Overview
The Data Link Layer facilitates error-free data transfer between adjacent nodes connected via a physical link, which may be point-to-point (e.g., PPP) or broadcast (e.g., Ethernet LAN). It receives packets from the Network Layer, encapsulates them into frames, and transmits them bit by bit over the Physical Layer. At the receiving end, it reassembles signals into frames and passes them to the Network Layer. The layer handles framing, addressing, error control, flow control, and media access in shared networks, making it one of the most intricate OSI layers.
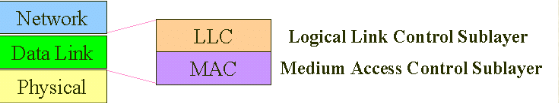
Sub-Layers of the Data Link Layer
The Data Link Layer is divided into two sub-layers, each with distinct responsibilities:
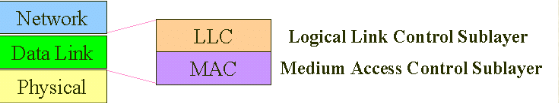
Logical Link Control (LLC)
The LLC sub-layer interfaces with the Network Layer and manages:
- Multiplexing data streams for multiple applications or services.
- Flow control to regulate data transfer rates.
- Error notifications and acknowledgments for reliable communication.
Media Access Control (MAC)
The MAC sub-layer interacts with the Physical Layer and handles:
- Frame addressing using MAC addresses.
- Access control to shared physical media (e.g., CSMA/CD in Ethernet).
- Conversion of packets into frames for transmission and vice versa.
Functions of the Data Link Layer
The Data Link Layer performs critical functions, such as:
Framing
Encapsulates Network Layer packets into frames by adding headers (e.g., source and destination MAC addresses) and trailers (e.g., CRC for error checking). Frames are transmitted bit-by-bit to the Physical Layer. At the receiver, signals are reassembled into frames. Framing techniques include:
- Character Count: Specifies frame length in the header.
- Byte Stuffing: Adds escape characters to distinguish data from control bytes.
- Bit Stuffing: Inserts bits to prevent misinterpretation of control sequences.
Addressing
Uses 48-bit MAC addresses, unique to each device, assigned during manufacturing. MAC addresses ensure accurate frame delivery within a local network.
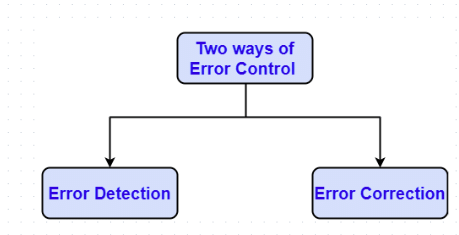
Error Control
Detects and, in some cases, corrects errors in transmitted frames. Common techniques include
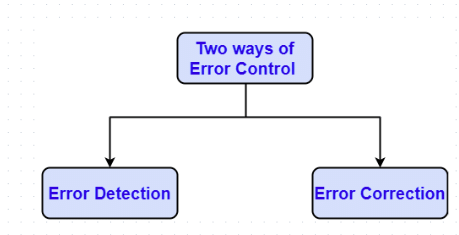
- Parity Check: Adds a parity bit to detect single-bit errors (simple but limited).
- Checksum: Computes a sum of data bits to detect errors; less robust for burst errors.
- Cyclic Redundancy Check (CRC): Uses polynomial division to detect burst errors; widely used in Ethernet (IEEE 802.3).
Errors are reported to the sender, and some protocols (e.g., HDLC) support retransmission for correction.
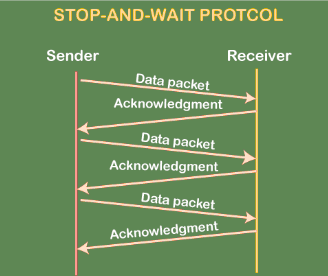
Flow Control
Ensures a fast sender does not overwhelm a slower receiver. Key techniques include:
- Stop-and-Wait: Sender transmits one frame and waits for acknowledgment (simple but inefficient).
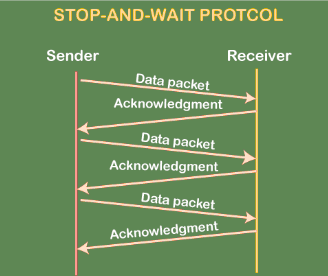
- Sliding Window: Allows multiple frames to be sent before acknowledgment, with protocols like Go-Back-N and Selective Repeat.
Synchronization
Ensures sender and receiver are aligned in timing for accurate frame transfer, critical in synchronous protocols like HDLC.
Multi-Access
Manages shared media access in broadcast networks to prevent collisions. Key protocols include:
- Carrier Sense Multiple Access with Collision Detection (CSMA/CD): Used in Ethernet to detect and resolve collisions.
- Carrier Sense Multiple Access with Collision Avoidance (CSMA/CA): Used in Wi-Fi (IEEE 802.11) to avoid collisions.
Protocols of the Data Link Layer
Data Link Layer has the following protocols:
- Synchronous Data Link Control (SDLC): A bit-oriented protocol for synchronous communication, used in IBM’s SNA.
- High-Level Data Link Control (HDLC): A versatile, bit-oriented protocol supporting point-to-point and multipoint links, with robust error and flow control.
- Serial Line Interface Protocol (SLIP): A simple protocol for point-to-point serial communication, lacking error control.
- Point-to-Point Protocol (PPP): Used for direct connections, supporting authentication, error detection, and compression.
- Link Access Procedure (LAP): Used in X.25 networks for reliable frame delivery.
- Link Control Protocol (LCP): Part of PPP, manages link establishment and configuration.
- Network Control Protocol (NCP): Part of PPP, configures Network Layer protocols.
Devices Operating at the Data Link Layer
- Switch: Forwards frames in LANs using MAC address tables, reducing collisions.
- Bridge: Connects multiple LAN segments, filtering frames based on MAC addresses to reduce traffic.
- Network Interface Card (NIC): Embeds MAC addresses and handles frame transmission/reception.
- Wireless Access Point (WAP): Manages wireless connections using IEEE 802.11 (Wi-Fi).
- Layer 2 Switches: Specialized switches focused on frame forwarding using MAC addresses.
Limitations of the Data Link Layer
- Limited Scope: Operates only within a local network, incapable of end-to-end communication.
- No Routing Capability: Relies on the Network Layer for inter-network routing.
- Increased Overhead: Headers, trailers, and error-checking bits increase data size.
- Error Handling Dependency: Handles basic error detection/correction but relies on upper layers for complex issues.
- Resource Usage: Flow control and error correction consume processing power and memory.
Applications of the Data Link Layer
- Local Area Networks (LANs): Supports Ethernet (IEEE 802.3) for reliable device communication.

- Wireless Networks: Manages Wi-Fi (IEEE 802.11) with media access and error control.
- Switches and MAC Addressing: Enables frame forwarding in LAN switches.
- Point-to-Point Connections: Supports direct links using protocols like PPP.
Address Resolution Protocol (ARP)
ARP maps IP addresses to physical addresses (e.g., destination host or next-hop router). Techniques include:
- Encoding the physical address in the host part of the IP address.
- Table-based mapping.
- ARP protocol:
- Maintains a table of IP-to-physical address bindings.
- Broadcasts a request if the IP address is not in the table.
- The target machine responds with its physical address.
- Table entries are discarded if not refreshed.
ARP Fields
- Hardware Type: Type of physical network (e.g., Ethernet).
- Protocol Type: Type of higher-layer protocol (e.g., IP).
- HLEN & PLEN: Length of physical and protocol addresses.
- Operation: Request or response.
- Source/Target Physical/Protocol Addresses.
Reverse Address Resolution Protocol (RARP)
RARP maps a physical address to an IP address, defined in RFC 903. It has been largely replaced by BOOTP and DHCP, which use UDP for IP address assignment.
Routing: Forwarding vs. Routing
- Forwarding: Selects an output port based on the destination address and routing table.
- Routing: Involves creating and managing the routing table.
Forwarding Table vs. Routing Table
- Forwarding Table: Maps a network number to an outgoing interface, including MAC details.
- Routing Table: Generated by the routing algorithm, maps network numbers to next hops.
Conclusion
The Data Link Layer is essential for reliable node-to-node communication in local networks. Its functions—framing, addressing, error control, flow control, synchronization, and multi-access—are extensively tested, alongside protocols (e.g., HDLC, PPP), devices (e.g., switches, NICs), and limitations.