All India Computer Science Engineering (CSE) Group
Predict output of following program
#include <stdio.h>
int fun(int n)
{
if (n == 4)
return n;
else return 2*fun(n+1);
}
int main()
{
printf("%d ", fun(2));
return 0;
}- a)4
- b)8
- c)16
- d)Runtime Error
Correct answer is option 'C'. Can you explain this answer?
Predict output of following program
#include <stdio.h>
int fun(int n)
{
if (n == 4)
return n;
else return 2*fun(n+1);
}
int main()
{
printf("%d ", fun(2));
return 0;
}
#include <stdio.h>
int fun(int n)
{
if (n == 4)
return n;
else return 2*fun(n+1);
}
int main()
{
printf("%d ", fun(2));
return 0;
}
a)
4
b)
8
c)
16
d)
Runtime Error
|
|
Nitin Datta answered • 17 hours ago |
Program Explanation
The given program consists of a recursive function `fun(int n)` and a `main()` function that calls this recursive function with an initial value of 2.
Function Logic
- The function `fun(int n)` checks if `n` is equal to 4.
- If `n` equals 4, it returns `n` (which is 4).
- If `n` is not equal to 4, it makes a recursive call to itself with... more
The given program consists of a recursive function `fun(int n)` and a `main()` function that calls this recursive function with an initial value of 2.
Function Logic
- The function `fun(int n)` checks if `n` is equal to 4.
- If `n` equals 4, it returns `n` (which is 4).
- If `n` is not equal to 4, it makes a recursive call to itself with... more
|
|
Riddhi Shahani
asked a question
|
Consider the following statements:
Statement-I: The Rig Veda mentions Arya varna and Dasa varna.
Statement-II: The tribal society was divided into three groups - warriors, priests, and the people, leading to social inequalities.
Which one of the following is correct in respect of the above statements?- a)Both Statement-I and Statement-II are correct and Statement-II explains Statement-I
- b)Both Statement-I and Statement-II are correct, but Statement-II does not explain Statement-I
- c)Statement-I is correct, but Statement-II is incorrect
- d)Statement-I is incorrect, but Statement-II is correct
Correct answer is option 'C'. Can you explain this answer?
Consider the following statements:
Statement-I: The Rig Veda mentions Arya varna and Dasa varna.
Statement-II: The tribal society was divided into three groups - warriors, priests, and the people, leading to social inequalities.
Which one of the following is correct in respect of the above statements?
Statement-I: The Rig Veda mentions Arya varna and Dasa varna.
Statement-II: The tribal society was divided into three groups - warriors, priests, and the people, leading to social inequalities.
Which one of the following is correct in respect of the above statements?
a)
Both Statement-I and Statement-II are correct and Statement-II explains Statement-I
b)
Both Statement-I and Statement-II are correct, but Statement-II does not explain Statement-I
c)
Statement-I is correct, but Statement-II is incorrect
d)
Statement-I is incorrect, but Statement-II is correct
|
|
Meera Saha
asked a question
|
In humid highlands, several dissected plateaus like the Scottish Highlands are found. Which of the forces are responsible for the formation of such dissected plateaus? 1. Stream action2. Cuts done due to glaciation3. Abrasion by windWhich of the above statement(s) is/are correct?- a) 1 and 2 only
- b) 2 and 3 only
- c) 1 and 3 only
- d) All of the above
Correct answer is option 'D'. Can you explain this answer?
In humid highlands, several dissected plateaus like the Scottish Highlands are found. Which of the forces are responsible for the formation of such dissected plateaus?
1. Stream action
2. Cuts done due to glaciation
3. Abrasion by wind
Which of the above statement(s) is/are correct?
a)
1 and 2 only
b)
2 and 3 only
c)
1 and 3 only
d)
All of the above

|
Ankita Pal
asked a question
|
Which of the following statements is not correct regarding Human immunodeficiency virus (HIV) and Acquired immunodeficiency syndrome (AIDS)?- a)AIDS is a term that applies to the most advanced stages of HIV infection.
- b)HIV is not spread by kisses, hugs or sharing food.
- c)There is no cure for AIDS till now.
- d)None of the above.
Correct answer is option 'D'. Can you explain this answer?
Which of the following statements is not correct regarding Human immunodeficiency virus (HIV) and Acquired immunodeficiency syndrome (AIDS)?
a)
AIDS is a term that applies to the most advanced stages of HIV infection.
b)
HIV is not spread by kisses, hugs or sharing food.
c)
There is no cure for AIDS till now.
d)
None of the above.
|
|
Raksha Menon
asked a question
|
Tectonic plateaus are formed due to Earth movements that cause uplifts. Consider the following statements:1. Meseta of Central Iberia2. Harz of Germany3. Bolivian plateau found between two ranges of AndesWhich of the following are tectonic plateaus found on Earth? - a) 2 and 3 only
- b) 1 and 2 only
- c) 1 and 3 only
- d) All of the above
Correct answer is option 'D'. Can you explain this answer?
Tectonic plateaus are formed due to Earth movements that cause uplifts. Consider the following statements:
1. Meseta of Central Iberia
2. Harz of Germany
3. Bolivian plateau found between two ranges of Andes
Which of the following are tectonic plateaus found on Earth?
a)
2 and 3 only
b)
1 and 2 only
c)
1 and 3 only
d)
All of the above
|
|
Sanjana Roy
asked a question
|
Which of the following are true with respect to fold mountains?
1. Their tops are often buried beneath snow and ice.
2. They are caused by the contraction of the earth's crust.
3. They form rugged peaks.
4. Fold mountains are mostly found along continental margins facing oceans
- a)1 and 3 only
- b)1 and 2
- c)2, 3 and 4
- d)1, 3 and 4
Correct answer is option 'D'. Can you explain this answer?
Which of the following are true with respect to fold mountains?
1. Their tops are often buried beneath snow and ice.
2. They are caused by the contraction of the earth's crust.
3. They form rugged peaks.
4. Fold mountains are mostly found along continental margins facing oceans
a)
1 and 3 only
b)
1 and 2
c)
2, 3 and 4
d)
1, 3 and 4
|
|
Sinjini Kumar
asked a question
|
Why a very large thickness of sedimentary rocks is found in the Fold Mountains? - a) Due to the folding of sediments.
- b) Due to the folding of plains into mountains
- c) Due to accumulation of sediments in a geosyncline
- d) Sediments have been deposited in the valley for millions of years
Correct answer is option 'C'. Can you explain this answer?
Why a very large thickness of sedimentary rocks is found in the Fold Mountains?
a)
Due to the folding of sediments.
b)
Due to the folding of plains into mountains
c)
Due to accumulation of sediments in a geosyncline
d)
Sediments have been deposited in the valley for millions of years
|
|
Manisha Tiwari
asked a question
|
Regarding fold mountains, consider the following statements: 1. Alpine mountain building phase is the recent phase to which the Himalayan mountains belong to.2. The Ural Mountains were formed during Alpine orogeny (mountain building phase) too.Which of the above statement(s) is/are correct? - a) 1 only
- b) 2 only
- c) Both 1 and 2
- d) None of the above
Correct answer is option 'A'. Can you explain this answer?
Regarding fold mountains, consider the following statements:
1. Alpine mountain building phase is the recent phase to which the Himalayan mountains belong to.
2. The Ural Mountains were formed during Alpine orogeny (mountain building phase) too.
Which of the above statement(s) is/are correct?
a)
1 only
b)
2 only
c)
Both 1 and 2
d)
None of the above

|
Simran Udmale
asked a question
|
Consider the following:
1. President
2. Lok Sabha
3. Rajya Sabha
4. Legislative assemblies
5. Legislative councils
How many of the above are compulsorily involved in all the constitutional amendment processes? - a)Only two
- b)Only three
- c)Only four
- d)All five
Correct answer is option 'B'. Can you explain this answer?
Consider the following:
1. President
2. Lok Sabha
3. Rajya Sabha
4. Legislative assemblies
5. Legislative councils
How many of the above are compulsorily involved in all the constitutional amendment processes?
1. President
2. Lok Sabha
3. Rajya Sabha
4. Legislative assemblies
5. Legislative councils
How many of the above are compulsorily involved in all the constitutional amendment processes?
a)
Only two
b)
Only three
c)
Only four
d)
All five
|
|
Puja Ahuja
asked a question
|
Fold mountains are formed due to large- scale movements in the Earth’s surface when stresses are set up in the Earth’s crust. What is/are the possible reason(s) for this?1. Increased load of overlying rocks2. Flow movements in the mantle3. Magnetic intrusions in the crustChoose the correct answer using the codes below:- a) 1 and 2 only
- b) 2 and 3 only
- c) 1 and 3 only
- d) All of the above
Correct answer is option 'D'. Can you explain this answer?
Fold mountains are formed due to large- scale movements in the Earth’s surface when stresses are set up in the Earth’s crust. What is/are the possible reason(s) for this?
1. Increased load of overlying rocks
2. Flow movements in the mantle
3. Magnetic intrusions in the crust
Choose the correct answer using the codes below:
a)
1 and 2 only
b)
2 and 3 only
c)
1 and 3 only
d)
All of the above

|
Prak Ashi
asked a question
|
Article 324 of the Constitution has made which of the following provisions to safeguard and ensure the independent and impartial functioning of the Election Commission?1. The election commissioners are provided with the security of tenure because their term is fixed as provided in the constitution.2. The Constitution has prescribed the qualifications for appointment to the office of the Election Commission.Which of the above is/are correct?- a)1 only
- b)2 only
- c)Both 1 and 2
- d)None
Correct answer is option 'D'. Can you explain this answer?
Article 324 of the Constitution has made which of the following provisions to safeguard and ensure the independent and impartial functioning of the Election Commission?
1. The election commissioners are provided with the security of tenure because their term is fixed as provided in the constitution.
2. The Constitution has prescribed the qualifications for appointment to the office of the Election Commission.
Which of the above is/are correct?
a)
1 only
b)
2 only
c)
Both 1 and 2
d)
None
|
|
Ayush Gupta
asked a question
|
What is a notable feature of the Silkyara Bend-Barkot Tunnel project?- a) It is primarily funded by international donors
- b) It features an escape passage for safety
- c) It is the longest tunnel in India
- d) It is constructed using traditional methods
Correct answer is option 'B'. Can you explain this answer?
What is a notable feature of the Silkyara Bend-Barkot Tunnel project?
a)
It is primarily funded by international donors
b)
It features an escape passage for safety
c)
It is the longest tunnel in India
d)
It is constructed using traditional methods
|
|
Mahika Sengupta
asked a question
|
How does the Navy-Marine Expeditionary Ship Interdiction System (NMESIS) enhance U.S. military capabilities?- a) By enhancing cyber warfare capabilities
- b) By providing air support for ground troops
- c) By facilitating land-to-sea attack operations
- d) By improving logistical operations
Correct answer is option 'C'. Can you explain this answer?
How does the Navy-Marine Expeditionary Ship Interdiction System (NMESIS) enhance U.S. military capabilities?
a)
By enhancing cyber warfare capabilities
b)
By providing air support for ground troops
c)
By facilitating land-to-sea attack operations
d)
By improving logistical operations
|
|
Hiral Shah
asked a question
|
What is the main purpose of the newly unveiled seed germination database by the Ecological Restoration Alliance-India?- a) To catalog all plant species in India
- b) To promote genetically modified plants
- c) To create a commercial seed market
- d) To improve the success rates of growing native plants
Correct answer is option 'D'. Can you explain this answer?
What is the main purpose of the newly unveiled seed germination database by the Ecological Restoration Alliance-India?
a)
To catalog all plant species in India
b)
To promote genetically modified plants
c)
To create a commercial seed market
d)
To improve the success rates of growing native plants
|
|
Naina Agarwal
asked a question
|
What is the significance of the Supreme Court's recent ruling in the Tamil Nadu Governor case?- a) It reinforces the federal structure of the Constitution
- b) It allows governors to have absolute authority
- c) It emphasizes the governor's veto power
- d) It supports the centralization of power
Correct answer is option 'A'. Can you explain this answer?
What is the significance of the Supreme Court's recent ruling in the Tamil Nadu Governor case?
a)
It reinforces the federal structure of the Constitution
b)
It allows governors to have absolute authority
c)
It emphasizes the governor's veto power
d)
It supports the centralization of power
|
|
Aadhya Sharma
asked a question
|
What key change does the Waqf (Amendment) Act, 2025 implement regarding waqf properties?- a) It increases the number of waqf properties
- b) It allows non-Muslims to serve on waqf boards
- c) It recognizes waqf-by-user properties legally
- d) It prohibits any changes to waqf property designations
Correct answer is option 'B'. Can you explain this answer?
What key change does the Waqf (Amendment) Act, 2025 implement regarding waqf properties?
a)
It increases the number of waqf properties
b)
It allows non-Muslims to serve on waqf boards
c)
It recognizes waqf-by-user properties legally
d)
It prohibits any changes to waqf property designations
|
|
Vara Bhandari
asked a question
|
What characterizes Type 5 diabetes as recognized by the International Diabetes Federation?- a) It has a genetic basis
- b) It is caused by obesity and insulin resistance
- c) It affects lean, undernourished individuals in low-income countries
- d) It primarily affects older adults
Correct answer is option 'C'. Can you explain this answer?
What characterizes Type 5 diabetes as recognized by the International Diabetes Federation?
a)
It has a genetic basis
b)
It is caused by obesity and insulin resistance
c)
It affects lean, undernourished individuals in low-income countries
d)
It primarily affects older adults
|
|
Radhika Sharma
asked a question
|
What is the impact of the U.S. reciprocal tariffs on India's trade?- a) Elimination of trade deficits
- b) Increase in India's agricultural exports
- c) Decrease in U.S. exports to India
- d) A 26% tariff imposed on Indian goods
Correct answer is option 'D'. Can you explain this answer?
What is the impact of the U.S. reciprocal tariffs on India's trade?
a)
Elimination of trade deficits
b)
Increase in India's agricultural exports
c)
Decrease in U.S. exports to India
d)
A 26% tariff imposed on Indian goods
|
|
Myra Rao
asked a question
|
What is the primary concern raised regarding Mount Lewotobi after its recent eruption?- a) Increased tourism in the area
- b) Economic benefits for local farmers
- c) The formation of new lava domes
- d) Safety risks for aviation and local populations
Correct answer is option 'D'. Can you explain this answer?
What is the primary concern raised regarding Mount Lewotobi after its recent eruption?
a)
Increased tourism in the area
b)
Economic benefits for local farmers
c)
The formation of new lava domes
d)
Safety risks for aviation and local populations
|
|
Maitri Datta
asked a question
|
Consider the following statements regarding the town planning of the Harappan Civilization: - The grid system was a hallmark of Harappan urban design, with roads cutting across each other almost at right angles.
- The Harappan cities lacked any form of drainage system, reflecting a minimal concern for public health and hygiene.
Which one of the following is correct in respect of the above statements?- a)Both Statement-I and Statement-II are correct and Statement-II is the correct explanation for Statement-I.
- b)Both Statement-I and Statement-II are correct but Statement-II is not the correct explanation for Statement-I.
- c)Statement-I is correct but Statement-II is incorrect.
- d)Statement-I is incorrect but Statement-II is correct.
Correct answer is option 'C'. Can you explain this answer?
Consider the following statements regarding the town planning of the Harappan Civilization:
- The grid system was a hallmark of Harappan urban design, with roads cutting across each other almost at right angles.
- The Harappan cities lacked any form of drainage system, reflecting a minimal concern for public health and hygiene.
Which one of the following is correct in respect of the above statements?
a)
Both Statement-I and Statement-II are correct and Statement-II is the correct explanation for Statement-I.
b)
Both Statement-I and Statement-II are correct but Statement-II is not the correct explanation for Statement-I.
c)
Statement-I is correct but Statement-II is incorrect.
d)
Statement-I is incorrect but Statement-II is correct.
|
|
Tarun Dube
asked a question
|
Consider the following statements regarding the drainage system of the Indus Valley Civilization:
- Each house had a private drinking well connected to the city's main drainage system.
- The main drains were covered with limestone blocks or baked bricks.
- Small settling pools and traps were integrated into the drainage system for maintenance and cleaning.
How many of the statements given above are correct?
- a)Only one
- b)All three
- c)Only two
- d)None
Correct answer is option 'C'. Can you explain this answer?
Consider the following statements regarding the drainage system of the Indus Valley Civilization:
- Each house had a private drinking well connected to the city's main drainage system.
- The main drains were covered with limestone blocks or baked bricks.
- Small settling pools and traps were integrated into the drainage system for maintenance and cleaning.
How many of the statements given above are correct?
a)
Only one
b)
All three
c)
Only two
d)
None

|
Arpita Pillai
asked a question
|
Consider the following statements:Statement-I: The Indus Valley civilization is known for its highly developed town planning, featuring planned cities with a scientific drainage system.Statement-II: The lower town in Indus cities was primarily inhabited by the working class, while the citadel was reserved for the ruling elite and administrative buildings.Which one of the following is correct in respect of the above statements?- a)Both Statement-I and Statement-II are correct and Statement-II explains Statement-I
- b)Both Statement-I and Statement-II are correct, but Statement-II does not explain Statement-I
- c)Statement-I is correct, but Statement-II is incorrect
- d)Statement-I is incorrect, but Statement-II is correct
Correct answer is option 'B'. Can you explain this answer?
Consider the following statements:
Statement-I: The Indus Valley civilization is known for its highly developed town planning, featuring planned cities with a scientific drainage system.
Statement-II: The lower town in Indus cities was primarily inhabited by the working class, while the citadel was reserved for the ruling elite and administrative buildings.
Which one of the following is correct in respect of the above statements?
a)
Both Statement-I and Statement-II are correct and Statement-II explains Statement-I
b)
Both Statement-I and Statement-II are correct, but Statement-II does not explain Statement-I
c)
Statement-I is correct, but Statement-II is incorrect
d)
Statement-I is incorrect, but Statement-II is correct
|
|
Rhea Banerjee
asked a question
|
Consider the following statements:1. The town planning of Indus Valley Civilization was based on the division of towns into two main parts: citadel/acropolis and lower town.
2. The use of burnt bricks in the Harappan cities was a standard practice which was also observed in the contemporary buildings of Egypt.
3. Kalibangan is known for its houses that had individual wells.
Which of the statements given above is/are correct?- a)1 Only
- b)1 and 3 Only
- c)1 and 2 Only
- d)1, 2 and 3
Correct answer is option 'B'. Can you explain this answer?
Consider the following statements:
1. The town planning of Indus Valley Civilization was based on the division of towns into two main parts: citadel/acropolis and lower town.
2. The use of burnt bricks in the Harappan cities was a standard practice which was also observed in the contemporary buildings of Egypt.
3. Kalibangan is known for its houses that had individual wells.
Which of the statements given above is/are correct?
2. The use of burnt bricks in the Harappan cities was a standard practice which was also observed in the contemporary buildings of Egypt.
3. Kalibangan is known for its houses that had individual wells.
Which of the statements given above is/are correct?
a)
1 Only
b)
1 and 3 Only
c)
1 and 2 Only
d)
1, 2 and 3
|
|
Navya Iyer
asked a question
|
In the following question below are given some statements followed by some conclusions based on those statements Taking the given statements to be true even if they seem to be at variance from commonly known facts. Read all the conclusions and then decide which of the given conclusion logically follows the given statements.Statements:I. All Z are Y.II. Some Y are B.Conclusion:I. Some B are not Z.II. Some Y are not Z.III. Some Z are Y. - a)Both conclusions II and III follows
- b)Both conclusions I and III follows
- c)Only conclusion III follows
- d)All conclusion follows
Correct answer is option 'C'. Can you explain this answer?
In the following question below are given some statements followed by some conclusions based on those statements Taking the given statements to be true even if they seem to be at variance from commonly known facts. Read all the conclusions and then decide which of the given conclusion logically follows the given statements.
Statements:
I. All Z are Y.
II. Some Y are B.
Conclusion:
I. Some B are not Z.
II. Some Y are not Z.
III. Some Z are Y.
a)
Both conclusions II and III follows
b)
Both conclusions I and III follows
c)
Only conclusion III follows
d)
All conclusion follows
|
|
Vaishnavi Saha
asked a question
|
Consider the following statements:
- The Harappan Civilization is older than the chalcolithic cultures found in the region.
- The area covered by the Harappan Civilization was approximately 1,299,600 square kilometers.
- The Harappan Civilization used metal money for trade.
How many of the statements given above are correct?
- a)Only one
- b)Only two
- c)All three
- d)None
Correct answer is option 'B'. Can you explain this answer?
Consider the following statements:
- The Harappan Civilization is older than the chalcolithic cultures found in the region.
- The area covered by the Harappan Civilization was approximately 1,299,600 square kilometers.
- The Harappan Civilization used metal money for trade.
How many of the statements given above are correct?
a)
Only one
b)
Only two
c)
All three
d)
None
|
|
Nakul Menon
asked a question
|
Deepika went to a fruit shop with a certain amount of money. She retains 15% of her money for auto fare. She can buy either 40 apples or 70 oranges with that remaining amount. If she buys 35 oranges, how many more apples she can buy?- a)35
- b)40
- c)15
- d)20
Correct answer is option 'D'. Can you explain this answer?
Deepika went to a fruit shop with a certain amount of money. She retains 15% of her money for auto fare. She can buy either 40 apples or 70 oranges with that remaining amount. If she buys 35 oranges, how many more apples she can buy?
a)
35
b)
40
c)
15
d)
20
|
|
Dishani Mukherjee
asked a question
|
Consider a processor with 64 registers and an instruction set of size twelve. Each instruction has five distinct fields, namely, opcode, two source register identifiers, one destination register identifier, and twelve-bit immediate value. Each instruction must be stored in memory in a byte-aligned fashion. If a program has 100 instructions, the amount of memory (in bytes)
consumed by the program text is _________.Correct answer is '=> 500 bytes'. Can you explain this answer?
Consider a processor with 64 registers and an instruction set of size twelve. Each instruction has five distinct fields, namely, opcode, two source register identifiers, one destination register identifier, and twelve-bit immediate value. Each instruction must be stored in memory in a byte-aligned fashion. If a program has 100 instructions, the amount of memory (in bytes)
consumed by the program text is _________.
consumed by the program text is _________.

|
Mohit Punyani
asked a question
|
A machine has a 32-bit architecture, with 1-word long instructions. It has 64 registers, each of which is 32 bits long. It needs to support 45 instructions, which have an immediate operand in addition to two register operands. Assuming that the immediate operand is an unsigned integer, the maximum value of the immediate operand is ____________Correct answer is '64 registers means 6 bits (⌈log2 64⌉ = 6) for a register operand. So, 2 register operand requires 12 bits. Now, 45 instructions require another 6 bits for opcode (⌈log2 45⌉ = 6). So, totally 18 bits. So, we have 32 - 18 = 14 bits left for the immediate operand. So, the max value will be 214 − 1 = 16383 (as the operand is unsigned we do not need a sign bit and with 14 bits we can represent from 0 to 214 − 1)'. Can you explain this answer?
A machine has a 32-bit architecture, with 1-word long instructions. It has 64 registers, each of which is 32 bits long. It needs to support 45 instructions, which have an immediate operand in addition to two register operands. Assuming that the immediate operand is an unsigned integer, the maximum value of the immediate operand is ____________
|
|
Harshitha Pillai
asked a question
|
In a class of 60, along with English as a common subject, students can opt to major in Mathematics, Physics, Biology or a combination of any two. 6 students major in both Mathematics and Physics, 15 major in both Physics and Biology, but no one majors in both Mathematics and Biology. In an English test, the average mark scored by students majoring in Mathematics is 45 and that of students majoring in Biology is 60. However, the combined average mark in English, of students of these two majors, is 50. What is the maximum possible number of students who major ONLY in Physics?
... more
In a class of 60, along with English as a common subject, students can opt to major in Mathematics, Physics, Biology or a combination of any two. 6 students major in both Mathematics and Physics, 15 major in both Physics and Biology, but no one majors in both Mathematics and Biology. In an English test, the average mark scored by students majoring in Mathematics is 45 and that of students majoring in Biology is 60. However, the combined average mark in English, of students of these two majors, is 50. What is the maximum possible number of students who major ONLY in Physics?
|
|
Amrutha Sharma
asked a question
|
Consider the following sequence of instructions intended for execution on a stack machine. Each arithmetic operation pops the second operand, then pops the first operand, operates on them, and then pushes-the result back onto the stack
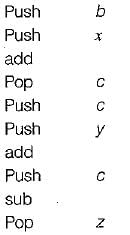
Which of the following statements is/are true?
1. If push and pop instructions each require 5 bytes of storage, and arithmetic operations each require 1 byte of storage then the instruction sequence as a whole requires a total of 40 bytes of storage.
2. At the end of execution, zcontainsthe same value as y.
3. At the end of execution, the stack is empty.- a)1 only
- b)2 only
- c)2 and 3 only
- d)1 and 3 only
Correct answer is option 'C'. Can you explain this answer?
Consider the following sequence of instructions intended for execution on a stack machine. Each arithmetic operation pops the second operand, then pops the first operand, operates on them, and then pushes-the result back onto the stack
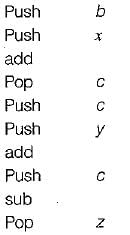
Which of the following statements is/are true?
1. If push and pop instructions each require 5 bytes of storage, and arithmetic operations each require 1 byte of storage then the instruction sequence as a whole requires a total of 40 bytes of storage.
2. At the end of execution, zcontainsthe same value as y.
3. At the end of execution, the stack is empty.
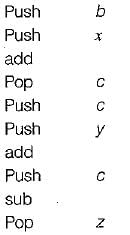
Which of the following statements is/are true?
1. If push and pop instructions each require 5 bytes of storage, and arithmetic operations each require 1 byte of storage then the instruction sequence as a whole requires a total of 40 bytes of storage.
2. At the end of execution, zcontainsthe same value as y.
3. At the end of execution, the stack is empty.
a)
1 only
b)
2 only
c)
2 and 3 only
d)
1 and 3 only
|
|
Kajal Tiwari
asked a question
|
Which countries, alongside India, have shown improvements in the UNCTAD ranking due to enhanced human capital?- a) Nepal and Bangladesh
- b) Sri Lanka and Pakistan
- c) China and Japan
- d) Bhutan, Morocco, Moldova, and Timor-Leste
Correct answer is option 'D'. Can you explain this answer?
Which countries, alongside India, have shown improvements in the UNCTAD ranking due to enhanced human capital?
a)
Nepal and Bangladesh
b)
Sri Lanka and Pakistan
c)
China and Japan
d)
Bhutan, Morocco, Moldova, and Timor-Leste
|
|
Sai Reddy
asked a question
|
What significant finding did the ChaSTE experiment reveal about the temperature conditions at the Moon's south pole?- a) Surface temperatures can reach up to 70°C during the lunar night
- b) There are no significant temperature variations at the lunar surface
- c) Temperatures at a depth of 80 mm can be around -10°C
- d) The lunar regolith is uniformly cold at all depths
Correct answer is option 'C'. Can you explain this answer?
What significant finding did the ChaSTE experiment reveal about the temperature conditions at the Moon's south pole?
a)
Surface temperatures can reach up to 70°C during the lunar night
b)
There are no significant temperature variations at the lunar surface
c)
Temperatures at a depth of 80 mm can be around -10°C
d)
The lunar regolith is uniformly cold at all depths
|
|
Rajat Basu
asked a question
|
Which morphological feature is distinctive for identifying the Euphaea wayanadensis species?- a) Brightly colored eyes.
- b) A shorter black patch on its wings compared to related species.
- c) Broader and interrupted body stripes in males.
- d) A longer black patch on its hind wing.
Correct answer is option 'D'. Can you explain this answer?
Which morphological feature is distinctive for identifying the Euphaea wayanadensis species?
a)
Brightly colored eyes.
b)
A shorter black patch on its wings compared to related species.
c)
Broader and interrupted body stripes in males.
d)
A longer black patch on its hind wing.
|
|
Sparsh Chakraborty
asked a question
|
What role does Section 40 play in the functioning of the Waqf Board according to the Waqf Act?- a) It allows the Board to increase the number of Waqf properties.
- b) It mandates the Board to report to the government on all Waqf properties.
- c) It provides guidelines for the sale of Waqf properties.
- d) It enables the Board to determine if a property is a Waqf property and make binding decisions.
Correct answer is option 'D'. Can you explain this answer?
What role does Section 40 play in the functioning of the Waqf Board according to the Waqf Act?
a)
It allows the Board to increase the number of Waqf properties.
b)
It mandates the Board to report to the government on all Waqf properties.
c)
It provides guidelines for the sale of Waqf properties.
d)
It enables the Board to determine if a property is a Waqf property and make binding decisions.
|
|
Jyoti Deshpande
asked a question
|
Which regions in India are highlighted as facing significant human-wildlife conflicts due to tigers venturing outside reserves?- a) Sundarbans and Eastern Ghats
- b) Central Indian Highlands and Terai plains
- c) Wayanad, Chandrapur, and Pilibhit
- d) Himalayas and Western Ghats
Correct answer is option 'C'. Can you explain this answer?
Which regions in India are highlighted as facing significant human-wildlife conflicts due to tigers venturing outside reserves?
a)
Sundarbans and Eastern Ghats
b)
Central Indian Highlands and Terai plains
c)
Wayanad, Chandrapur, and Pilibhit
d)
Himalayas and Western Ghats
|
|
Jhanvi Datta
asked a question
|
Why is the Arctic considered strategically important in the context of global competition?- a) It serves as a major agricultural hub.
- b) It is a key region for military alliances and exercises.
- c) It has the highest population density in the world.
- d) It contains abundant natural resources and disputed territories.
Correct answer is option 'D'. Can you explain this answer?
Why is the Arctic considered strategically important in the context of global competition?
a)
It serves as a major agricultural hub.
b)
It is a key region for military alliances and exercises.
c)
It has the highest population density in the world.
d)
It contains abundant natural resources and disputed territories.
|
|
Shreya Kulkarni
asked a question
|
Which states are included in the initial pilot implementation of the ZooWIN platform?- a) Maharashtra, Gujarat, and Punjab
- b) Tamil Nadu, Kerala, and Karnataka
- c) Delhi, Madhya Pradesh, Assam, Puducherry, and Andhra Pradesh
- d) Rajasthan, Uttarakhand, and West Bengal
Correct answer is option 'C'. Can you explain this answer?
Which states are included in the initial pilot implementation of the ZooWIN platform?
a)
Maharashtra, Gujarat, and Punjab
b)
Tamil Nadu, Kerala, and Karnataka
c)
Delhi, Madhya Pradesh, Assam, Puducherry, and Andhra Pradesh
d)
Rajasthan, Uttarakhand, and West Bengal
|
|
Shruti Bose
asked a question
|
Which naval vessels are part of the Indian contingent in the Tiger Triumph exercise?- a) USS Comstock and USS Ralph Johnson
- b) INS Vikrant and INS Kolkata
- c) INS Jalashwa, INS Gharial, INS Mumbai, and INS Shakti
- d) USS Nimitz and USS Ronald Reagan
Correct answer is option 'C'. Can you explain this answer?
Which naval vessels are part of the Indian contingent in the Tiger Triumph exercise?
a)
USS Comstock and USS Ralph Johnson
b)
INS Vikrant and INS Kolkata
c)
INS Jalashwa, INS Gharial, INS Mumbai, and INS Shakti
d)
USS Nimitz and USS Ronald Reagan
|
|
Priyanka Tiwari
asked a question
|
What was one of the primary mission objectives of the Pioneer 11 spacecraft?- a) To map the surface of Mars
- b) To send humans to the Moon
- c) To explore the asteroid belt
- d) To study the gravitational fields of Jupiter and Saturn
Correct answer is option 'D'. Can you explain this answer?
What was one of the primary mission objectives of the Pioneer 11 spacecraft?
a)
To map the surface of Mars
b)
To send humans to the Moon
c)
To explore the asteroid belt
d)
To study the gravitational fields of Jupiter and Saturn
|
|
Janhavi Choudhary
asked a question
|
What is the primary goal of the GP-DRASTI initiative introduced by the Gujarat Police?- a) To improve police response speed using drones
- b) To replace all traditional policing methods
- c) To eliminate gang violence entirely
- d) To conduct aerial surveillance without police presence
Correct answer is option 'A'. Can you explain this answer?
What is the primary goal of the GP-DRASTI initiative introduced by the Gujarat Police?
a)
To improve police response speed using drones
b)
To replace all traditional policing methods
c)
To eliminate gang violence entirely
d)
To conduct aerial surveillance without police presence
|
|
Niharika Iyer
asked a question
|
What is the primary purpose of the Hansa Next Generation (NG) trainer aircraft as developed by the National Aerospace Laboratories (NAL)?- a) To serve as a passenger aircraft
- b) To replace all existing aircraft in the Indian Air Force
- c) To increase the number of commercial flights in India
- d) To enhance pilot training capabilities
Correct answer is option 'D'. Can you explain this answer?
What is the primary purpose of the Hansa Next Generation (NG) trainer aircraft as developed by the National Aerospace Laboratories (NAL)?
a)
To serve as a passenger aircraft
b)
To replace all existing aircraft in the Indian Air Force
c)
To increase the number of commercial flights in India
d)
To enhance pilot training capabilities
|
|
Anjali Sengupta
asked a question
|
What is one of the main challenges that developing nations face in relation to AI and frontier technologies?- a) Overabundance of AI infrastructure
- b) Lack of interest in technological advancement
- c) Excessive investment in education
- d) Limited access to AI infrastructure
Correct answer is option 'D'. Can you explain this answer?
What is one of the main challenges that developing nations face in relation to AI and frontier technologies?
a)
Overabundance of AI infrastructure
b)
Lack of interest in technological advancement
c)
Excessive investment in education
d)
Limited access to AI infrastructure
|
|
Pritam Das
asked a question
|
What is the primary purpose of the Chandra's Surface Thermophysical Experiment (ChaSTE) in the Chandrayaan-3 mission?- a) To measure the vertical temperature profile of the lunar surface
- b) To study the gravitational field of the Moon
- c) To analyze the chemical composition of lunar regolith
- d) To map the lunar surface using high-resolution images
Correct answer is option 'A'. Can you explain this answer?
What is the primary purpose of the Chandra's Surface Thermophysical Experiment (ChaSTE) in the Chandrayaan-3 mission?
a)
To measure the vertical temperature profile of the lunar surface
b)
To study the gravitational field of the Moon
c)
To analyze the chemical composition of lunar regolith
d)
To map the lunar surface using high-resolution images
|
|
Aniket Saini
asked a question
|
What is the significance of the discovery of Euphaea wayanadensis in the context of biodiversity in Kerala?- a) It confirms the extinction of a previous species.
- b) It suggests that the Western Ghats are not biodiverse.
- c) It adds to the total number of odonate species in Kerala.
- d) It indicates a decrease in the population of damselflies.
Correct answer is option 'C'. Can you explain this answer?
What is the significance of the discovery of Euphaea wayanadensis in the context of biodiversity in Kerala?
a)
It confirms the extinction of a previous species.
b)
It suggests that the Western Ghats are not biodiverse.
c)
It adds to the total number of odonate species in Kerala.
d)
It indicates a decrease in the population of damselflies.

|
Mihir Kulkarni
asked a question
|
What is the primary concern raised by critics regarding the proposed removal of Section 40 from the Waqf Act?- a) It would enhance the independence of the Waqf Board in property determinations.
- b) It could weaken the authority of the Waqf Board and its ability to manage properties effectively.
- c) It would lead to more transparency in the management of Waqf properties.
- d) It would increase the number of Waqf properties managed by the government.
Correct answer is option 'B'. Can you explain this answer?
What is the primary concern raised by critics regarding the proposed removal of Section 40 from the Waqf Act?
a)
It would enhance the independence of the Waqf Board in property determinations.
b)
It could weaken the authority of the Waqf Board and its ability to manage properties effectively.
c)
It would lead to more transparency in the management of Waqf properties.
d)
It would increase the number of Waqf properties managed by the government.
|
|
Vanya Bhandari
asked a question
|
What is the primary goal of the "Tigers Outside Tiger Reserves" initiative launched by the Ministry of Environment, Forest and Climate Change?- a) To relocate all tigers to protected areas
- b) To eliminate human-wildlife conflicts completely
- c) To increase the number of designated tiger reserves
- d) To monitor and reduce poaching of tigers outside reserves
Correct answer is option 'D'. Can you explain this answer?
What is the primary goal of the "Tigers Outside Tiger Reserves" initiative launched by the Ministry of Environment, Forest and Climate Change?
a)
To relocate all tigers to protected areas
b)
To eliminate human-wildlife conflicts completely
c)
To increase the number of designated tiger reserves
d)
To monitor and reduce poaching of tigers outside reserves
|
|
Pari Mehta
asked a question
|
What is a significant consequence of the rising temperatures in the Arctic as mentioned in the context of international relations?- a) Increased biodiversity in Arctic ecosystems
- b) Decreased interest in Arctic exploration
- c) Enhanced cooperation among Arctic nations
- d) Escalating territorial claims and military tensions
Correct answer is option 'D'. Can you explain this answer?
What is a significant consequence of the rising temperatures in the Arctic as mentioned in the context of international relations?
a)
Increased biodiversity in Arctic ecosystems
b)
Decreased interest in Arctic exploration
c)
Enhanced cooperation among Arctic nations
d)
Escalating territorial claims and military tensions
|
|
Lavanya Agarwal
asked a question
|
What is the primary objective of the ZooWIN platform launched by the Indian government?- a) To provide financial assistance to healthcare workers
- b) To improve the quality of education in rural areas
- c) To monitor the stocks of anti-rabies vaccines and anti-snake venom in real-time
- d) To promote tourism in wildlife sanctuaries
Correct answer is option 'C'. Can you explain this answer?
What is the primary objective of the ZooWIN platform launched by the Indian government?
a)
To provide financial assistance to healthcare workers
b)
To improve the quality of education in rural areas
c)
To monitor the stocks of anti-rabies vaccines and anti-snake venom in real-time
d)
To promote tourism in wildlife sanctuaries
|
|
Urvashi Verma
asked a question
|
What is the primary objective of the Tiger Triumph exercise?- a) To improve interoperability during humanitarian assistance and disaster relief operations
- b) To conduct joint military offensives in the region
- c) To establish a new naval base in India
- d) To evaluate the performance of new military technologies
Correct answer is option 'A'. Can you explain this answer?
What is the primary objective of the Tiger Triumph exercise?
a)
To improve interoperability during humanitarian assistance and disaster relief operations
b)
To conduct joint military offensives in the region
c)
To establish a new naval base in India
d)
To evaluate the performance of new military technologies
|
|
Navya Iyer
asked a question
|
What is the primary objective of the India-U.S. tri-service Humanitarian Assistance and Disaster Relief (HADR) Exercise Tiger Triumph scheduled for April 2025?- a) To showcase new military technology to the public
- b) To train civilians in emergency response techniques
- c) To conduct military drills unrelated to disaster response
- d) To enhance collaboration and coordination in disaster response operations
Correct answer is option 'D'. Can you explain this answer?
What is the primary objective of the India-U.S. tri-service Humanitarian Assistance and Disaster Relief (HADR) Exercise Tiger Triumph scheduled for April 2025?
a)
To showcase new military technology to the public
b)
To train civilians in emergency response techniques
c)
To conduct military drills unrelated to disaster response
d)
To enhance collaboration and coordination in disaster response operations
|
|
Advait Das
asked a question
|
What significant finding was revealed about the Olive Ridley turtles residing in the Indian Ocean?- a) They are the oldest turtle populations globally.
- b) They are the smallest sea turtle species.
- c) They exclusively nest in Central America.
- d) They migrate only within the Pacific Ocean.
Correct answer is option 'A'. Can you explain this answer?
What significant finding was revealed about the Olive Ridley turtles residing in the Indian Ocean?
a)
They are the oldest turtle populations globally.
b)
They are the smallest sea turtle species.
c)
They exclusively nest in Central America.
d)
They migrate only within the Pacific Ocean.
|
|
Kunal Yadav
asked a question
|
What is a significant benefit of establishing local data centers in India?- a) They eliminate the requirement for data protection regulations.
- b) They solely create jobs in the technology sector.
- c) They can enhance national security and support AI development.
- d) They reduce the need for cloud computing services.
Correct answer is option 'C'. Can you explain this answer?
What is a significant benefit of establishing local data centers in India?
a)
They eliminate the requirement for data protection regulations.
b)
They solely create jobs in the technology sector.
c)
They can enhance national security and support AI development.
d)
They reduce the need for cloud computing services.
|
|
Zara Chawla
asked a question
|
What strategy is recommended to address the skill-industry mismatch in India's labor market?- a) Encourage youth to pursue entrepreneurship without formal training
- b) Increase the number of universities offering traditional degrees
- c) Promote outcome-based skilling through partnerships with NSDC and private sectors
- d) Decrease the focus on technical skills in education
Correct answer is option 'C'. Can you explain this answer?
What strategy is recommended to address the skill-industry mismatch in India's labor market?
a)
Encourage youth to pursue entrepreneurship without formal training
b)
Increase the number of universities offering traditional degrees
c)
Promote outcome-based skilling through partnerships with NSDC and private sectors
d)
Decrease the focus on technical skills in education
|
|
Nishant Sethi
asked a question
|
What is a significant issue highlighted regarding the female labor force participation rate (LFPR) in India?- a) It is significantly lower than that of males.
- b) It has been increasing rapidly in urban areas.
- c) It shows no variation across different age groups.
- d) It is equal to that of males.
Correct answer is option 'A'. Can you explain this answer?
What is a significant issue highlighted regarding the female labor force participation rate (LFPR) in India?
a)
It is significantly lower than that of males.
b)
It has been increasing rapidly in urban areas.
c)
It shows no variation across different age groups.
d)
It is equal to that of males.
|
|
Sahil Chawla
asked a question
|
What was the trend in the Labour Force Participation Rate (LFPR) for males in urban areas according to the Periodic Labour Force Survey 2024?- a) It increased from 74.3% to 75.6%
- b) It remained stable at 74.3%
- c) It decreased from 74.3% to 73.5%
- d) It increased from 75.0% to 76.0%
Correct answer is option 'A'. Can you explain this answer?
What was the trend in the Labour Force Participation Rate (LFPR) for males in urban areas according to the Periodic Labour Force Survey 2024?
a)
It increased from 74.3% to 75.6%
b)
It remained stable at 74.3%
c)
It decreased from 74.3% to 73.5%
d)
It increased from 75.0% to 76.0%
|
|
Akshara Kapoor
asked a question
|
What prompted India to terminate the transshipment facility for Bangladesh?- a)India aimed to improve its relations with the United States by reducing trade with Bangladesh.
- b)Rising air freight costs and strategic concerns regarding China's influence in the region influenced the decision.
- c)India wanted to strengthen its textile market by reducing competition from Bangladesh.
- d)Bangladesh's request for more direct trade routes to China necessitated India's withdrawal.
Correct answer is option 'B'. Can you explain this answer?
What prompted India to terminate the transshipment facility for Bangladesh?
a)
India aimed to improve its relations with the United States by reducing trade with Bangladesh.
b)
Rising air freight costs and strategic concerns regarding China's influence in the region influenced the decision.
c)
India wanted to strengthen its textile market by reducing competition from Bangladesh.
d)
Bangladesh's request for more direct trade routes to China necessitated India's withdrawal.

|
Vaibhav Malode
asked a question
|
Join Selectivity of a relation R in a natural join with a relation S is the _____- a)Ratio of the distinct attribute values for attribute A participating in the join to the total number of distinct attributes for the same attribute in R.
- b)Ratio of the non-distinct attribute values for attribute A participating in the join to the total number of distinct values for the same attribute in R.
- c)Ratio of the distinct attribute values for attribute A participating in the join to the total number of non-distinct values for the same attribute in R.
- d)None of the above
Correct answer is option 'A'. Can you explain this answer?
Join Selectivity of a relation R in a natural join with a relation S is the _____
a)
Ratio of the distinct attribute values for attribute A participating in the join to the total number of distinct attributes for the same attribute in R.
b)
Ratio of the non-distinct attribute values for attribute A participating in the join to the total number of distinct values for the same attribute in R.
c)
Ratio of the distinct attribute values for attribute A participating in the join to the total number of non-distinct values for the same attribute in R.
d)
None of the above
|
|
Arnav Trivedi
asked a question
|
What is one of the primary goals of reviving the WTO's Appellate Body as a mitigation strategy for India?- a) To facilitate South-South trade corridors
- b) To strengthen ties with the US
- c) To reduce production costs in India
- d) To increase tariffs on imports
Correct answer is option 'A'. Can you explain this answer?
What is one of the primary goals of reviving the WTO's Appellate Body as a mitigation strategy for India?
a)
To facilitate South-South trade corridors
b)
To strengthen ties with the US
c)
To reduce production costs in India
d)
To increase tariffs on imports
|
|
Aarav Singh
asked a question
|
What is a potential economic consequence of a full-scale trade war between major economies?- a) Enhanced technological collaboration
- b) Recession risks due to simultaneous economic slowdowns
- c) Increased global tourism
- d) Strengthened multilateral trade agreements
Correct answer is option 'B'. Can you explain this answer?
What is a potential economic consequence of a full-scale trade war between major economies?
a)
Enhanced technological collaboration
b)
Recession risks due to simultaneous economic slowdowns
c)
Increased global tourism
d)
Strengthened multilateral trade agreements
|
|
Eshan Agnihotri
asked a question
|
What principle of Lord Mahavira encourages sustainable lifestyles and aligns with global initiatives for environmental sustainability?- a) Ahimsa (Nonviolence)
- b) Aparigraha (Non-possessiveness)
- c) Satya (Truth)
- d) Anekantavada (Multiplicity of Truths)
Correct answer is option 'B'. Can you explain this answer?
What principle of Lord Mahavira encourages sustainable lifestyles and aligns with global initiatives for environmental sustainability?
a)
Ahimsa (Nonviolence)
b)
Aparigraha (Non-possessiveness)
c)
Satya (Truth)
d)
Anekantavada (Multiplicity of Truths)
|
|
Manav Verma
asked a question
|
What is one of the major reasons mentioned for India's high maternal mortality rate despite progress in healthcare?- a) High birth rates
- b) Cultural practices
- c) Insufficient healthcare infrastructure in rural areas
- d) Lack of women’s education
Correct answer is option 'C'. Can you explain this answer?
What is one of the major reasons mentioned for India's high maternal mortality rate despite progress in healthcare?
a)
High birth rates
b)
Cultural practices
c)
Insufficient healthcare infrastructure in rural areas
d)
Lack of women’s education
|
|
Riddhi Thakkar
asked a question
|
What is a significant challenge in accessing skilled birth care in rural areas?- a) Abundant healthcare facilities in remote areas
- b) High rates of immunization among mothers
- c) Increased availability of transportation for expectant mothers
- d) Lack of access to skilled birth attendants
Correct answer is option 'D'. Can you explain this answer?
What is a significant challenge in accessing skilled birth care in rural areas?
a)
Abundant healthcare facilities in remote areas
b)
High rates of immunization among mothers
c)
Increased availability of transportation for expectant mothers
d)
Lack of access to skilled birth attendants
|
|
Ananya Kapoor
asked a question
|
What is a significant concern regarding India's maternal mortality rate (MMR) despite its reported decrease?- a) There are no regional disparities in healthcare access.
- b) It remains the lowest in the world.
- c) The absolute number of maternal deaths is still high.
- d) It is decreasing faster than in most developed countries.
Correct answer is option 'C'. Can you explain this answer?
What is a significant concern regarding India's maternal mortality rate (MMR) despite its reported decrease?
a)
There are no regional disparities in healthcare access.
b)
It remains the lowest in the world.
c)
The absolute number of maternal deaths is still high.
d)
It is decreasing faster than in most developed countries.
|
|
Avani Patel
asked a question
|
What is a key challenge faced by smaller South Asian nations regarding India's role in regional integration?- a) Cultural exchange programs
- b) Environmental policies
- c) Perception of Hegemony
- d) Economic prosperity of India
Correct answer is option 'C'. Can you explain this answer?
What is a key challenge faced by smaller South Asian nations regarding India's role in regional integration?
a)
Cultural exchange programs
b)
Environmental policies
c)
Perception of Hegemony
d)
Economic prosperity of India
|
|
Divya Verma
asked a question
|
What role does India play in enhancing regional connectivity in South Asia?- a) It is involved in developing cross-border infrastructure and trade corridors.
- b) It primarily focuses on military alliances with neighboring countries.
- c) It maintains a strict isolationist policy regarding trade.
- d) It discourages economic collaboration with other South Asian nations.
Correct answer is option 'A'. Can you explain this answer?
What role does India play in enhancing regional connectivity in South Asia?
a)
It is involved in developing cross-border infrastructure and trade corridors.
b)
It primarily focuses on military alliances with neighboring countries.
c)
It maintains a strict isolationist policy regarding trade.
d)
It discourages economic collaboration with other South Asian nations.
|
|
Krish Mehta
asked a question
|
What is a primary reason for the shift from globalism to regionalism in the current global order?- a) A decline in national sovereignty
- b) Increased faith in multilateral governance
- c) The rise of authoritarian regimes worldwide
- d) Ongoing global conflicts and institutional paralysis
Correct answer is option 'D'. Can you explain this answer?
What is a primary reason for the shift from globalism to regionalism in the current global order?
a)
A decline in national sovereignty
b)
Increased faith in multilateral governance
c)
The rise of authoritarian regimes worldwide
d)
Ongoing global conflicts and institutional paralysis
|
|
Gaurav Bhandari
asked a question
|
What is one potential benefit of enhancing Indian investments in Sri Lanka's IT sector?- a) It will reduce the need for renewable energy solutions.
- b) It can lead to improved economic integration between the two countries.
- c) It will decrease trade relations between India and Sri Lanka.
- d) It may result in increased illegal fishing activities.
Correct answer is option 'B'. Can you explain this answer?
What is one potential benefit of enhancing Indian investments in Sri Lanka's IT sector?
a)
It will reduce the need for renewable energy solutions.
b)
It can lead to improved economic integration between the two countries.
c)
It will decrease trade relations between India and Sri Lanka.
d)
It may result in increased illegal fishing activities.
|
|
Wasima Thakur
asked a question
|
What is a significant concern for India regarding the Chinese presence in Sri Lanka?- a) Economic cooperation through trade agreements
- b) Cultural exchanges between the two nations
- c) Strategic encirclement due to the Belt and Road Initiative
- d) Joint military exercises with Sri Lanka
Correct answer is option 'C'. Can you explain this answer?
What is a significant concern for India regarding the Chinese presence in Sri Lanka?
a)
Economic cooperation through trade agreements
b)
Cultural exchanges between the two nations
c)
Strategic encirclement due to the Belt and Road Initiative
d)
Joint military exercises with Sri Lanka
|
|
Qiana Iyer
asked a question
|
What significant approval has the United States granted to Holtec International regarding nuclear technology in India?- a) The ability to construct military reactors
- b) The establishment of a nuclear weapons program in India
- c) The transfer of Small Modular Reactor (SMR) technology for peaceful civilian use
- d) The exclusive rights to sell nuclear fuel to India
Correct answer is option 'C'. Can you explain this answer?
What significant approval has the United States granted to Holtec International regarding nuclear technology in India?
a)
The ability to construct military reactors
b)
The establishment of a nuclear weapons program in India
c)
The transfer of Small Modular Reactor (SMR) technology for peaceful civilian use
d)
The exclusive rights to sell nuclear fuel to India
|
|
Ishan Shah
asked a question
|
What proposed measure aims to enhance the accountability of Governors in state governance?- a) Establishing a national committee for gubernatorial appointments
- b) Increasing the discretionary powers of Governors
- c) Implementing a direct election system for Governors
- d) Creating a state-level impeachment process for Governors
Correct answer is option 'D'. Can you explain this answer?
What proposed measure aims to enhance the accountability of Governors in state governance?
a)
Establishing a national committee for gubernatorial appointments
b)
Increasing the discretionary powers of Governors
c)
Implementing a direct election system for Governors
d)
Creating a state-level impeachment process for Governors
|
|
Keshav Sharma
asked a question
|
What is a significant concern regarding the role of Governors in India?- a) Their perceived partiality towards the ruling party at the Centre
- b) Their power to appoint state governors without approval
- c) Their ability to initiate legislation independently
- d) Their authority to conduct elections
Correct answer is option 'A'. Can you explain this answer?
What is a significant concern regarding the role of Governors in India?
a)
Their perceived partiality towards the ruling party at the Centre
b)
Their power to appoint state governors without approval
c)
Their ability to initiate legislation independently
d)
Their authority to conduct elections
|
|
Qamar Rao
asked a question
|
What action can a Governor take regarding a bill that has been passed by the State Legislature?- a) Automatically send the bill to the President
- b) Approve, withhold assent, or return the bill for reconsideration
- c) Modify the bill's content before it becomes law
- d) Only grant assent to the bill
Correct answer is option 'B'. Can you explain this answer?
What action can a Governor take regarding a bill that has been passed by the State Legislature?
a)
Automatically send the bill to the President
b)
Approve, withhold assent, or return the bill for reconsideration
c)
Modify the bill's content before it becomes law
d)
Only grant assent to the bill
|
|
Bhumi Patel
asked a question
|
What was the Supreme Court's ruling regarding the Governor's action of referring re-enacted Bills to the President?- a) The referral was considered a necessary step in the legislative process.
- b) The referral indicated the Governor's refusal to cooperate with the state government.
- c) The referral was upheld as a legitimate exercise of the Governor's power.
- d) The referral was deemed erroneous in law, emphasizing the absence of an absolute veto.
Correct answer is option 'D'. Can you explain this answer?
What was the Supreme Court's ruling regarding the Governor's action of referring re-enacted Bills to the President?
a)
The referral was considered a necessary step in the legislative process.
b)
The referral indicated the Governor's refusal to cooperate with the state government.
c)
The referral was upheld as a legitimate exercise of the Governor's power.
d)
The referral was deemed erroneous in law, emphasizing the absence of an absolute veto.
|
|
Omkar Rao
asked a question
|
What did the Supreme Court of India clarify regarding the role of governors in relation to state bills?- a) Governors can delay action on state bills indefinitely.
- b) Governors can refuse to act on state bills without providing reasons.
- c) Governors must act on state bills in a timely manner, following the advice of the council of ministers.
- d) Governors have the authority to amend state bills independently.
Correct answer is option 'C'. Can you explain this answer?
What did the Supreme Court of India clarify regarding the role of governors in relation to state bills?
a)
Governors can delay action on state bills indefinitely.
b)
Governors can refuse to act on state bills without providing reasons.
c)
Governors must act on state bills in a timely manner, following the advice of the council of ministers.
d)
Governors have the authority to amend state bills independently.
|
|
Abhijeet Unni
asked a question
|
Consider the following floating point number representation.
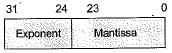
The exponent is in 2’s complement representation and mantissa is in the sign-magnitude representation. The range of the magnitude of the normalized numbers in this representation is- a)0 to 1
- b)0.5 to 1
- c)2-23 to 0.5
- d)0.5 to (1-2-23)
Correct answer is option 'D'. Can you explain this answer?
Consider the following floating point number representation.
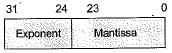
The exponent is in 2’s complement representation and mantissa is in the sign-magnitude representation. The range of the magnitude of the normalized numbers in this representation is
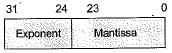
The exponent is in 2’s complement representation and mantissa is in the sign-magnitude representation. The range of the magnitude of the normalized numbers in this representation is
a)
0 to 1
b)
0.5 to 1
c)
2-23 to 0.5
d)
0.5 to (1-2-23)
Fetching relevant content for you
Ask a doubt
Recommended Content
|
|
|
|
|














